Last updated on May 21, 2015

Get the free USFK JCISA Acceptable Use Policy
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

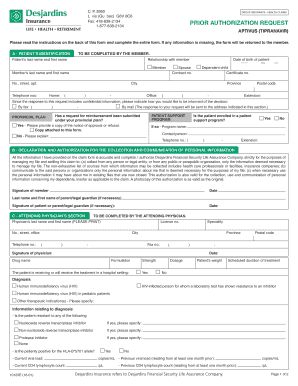
What is USFK Policy
The USFK JCISA Acceptable Use Policy is a policy form used by authorized personnel to understand their responsibilities while accessing USFK JCISA C2 Systems and Networks.
pdfFiller scores top ratings on review platforms




Who needs USFK Policy?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to USFK Policy
What is the USFK JCISA Acceptable Use Policy?
The USFK JCISA Acceptable Use Policy serves as a crucial document that delineates the parameters for using the USFK JCISA C2 Systems and Networks. It is essential for ensuring that all users understand the necessary rules and their implications. This policy outlines critical topics including access rules, handling of classified information, and proper conduct while using these systems.
Understanding the USFK network policy is vital as it directly impacts the security of sensitive data and operations. The policy provides guidance on expected behaviors and the importance of compliance to maintain a secure environment.
Purpose and Benefits of the USFK JCISA Acceptable Use Policy
The necessity of the USFK JCISA Acceptable Use Policy cannot be overstated; it is integral for maintaining security and ensuring compliance across all users. By adhering to this policy, users can significantly reduce their risk of unauthorized data access or breaches.
The benefits of understanding the USFK security policy extend to all personnel utilizing USFK JCISA C2 Systems, enabling them to navigate sensitive systems responsibly. Non-compliance not only jeopardizes security but also poses substantial risks, including disciplinary actions for involved personnel.
Key Features of the USFK JCISA Acceptable Use Policy
The USFK JCISA Acceptable Use Policy includes essential features designed to ensure compliance and security. Among these features are the guidelines regarding revocability of access, protection of personally identifiable information (PII), and adherence to minimum security protocols.
-
Revocability of user access under specific conditions.
-
Mandatory protections for PII to safeguard sensitive personal data.
-
Minimum security rules that users must follow to maintain network integrity.
Users are required to acknowledge their understanding of the policy by signing and indicating their compliance through checkboxes on the form. This acknowledgment is key to ensuring that all users are aware of their responsibilities regarding security standards.
Who Needs to Complete the USFK JCISA Acceptable Use Policy?
Completing the USFK JCISA Acceptable Use Policy is a critical requirement for all personnel who have been granted access to the relevant systems. This includes both U.S. and ROK personnel authorized for system access.
The policy is especially pertinent for users handling sensitive data or operating within classified systems. Military and civilian personnel alike must complete this form to demonstrate their eligibility and obligation to comply with the stipulated rules.
How to Fill Out the USFK JCISA Acceptable Use Policy Online
To complete the USFK JCISA Acceptable Use Policy online, follow these step-by-step instructions:
-
Access the policy form via the designated platform.
-
Carefully fill out each field, ensuring all required sections are completed.
-
Utilize the provided checkboxes to acknowledge understanding where applicable.
-
Sign the form electronically to validate your submission.
-
Review all information for accuracy before final submission.
These steps will help ensure that your completed form is accurate and ready for processing.
Submission Methods and Delivery of the USFK JCISA Acceptable Use Policy
After filling out the USFK JCISA Acceptable Use Policy, there are several acceptable methods for submission. Users can submit the form digitally through a secure upload feature or via email, depending on the guidelines provided.
Keep track of submissions and remember to confirm receipt once your form is submitted. Users should also note any potential fees or deadlines associated with their submissions to ensure compliance with the policy.
Security and Compliance for the USFK JCISA Acceptable Use Policy
Data protection is paramount when it comes to the USFK JCISA Acceptable Use Policy. Security measures, such as encryption and adherence to compliance regulations, ensure that sensitive data remains secure from unauthorized access.
Following the policy is essential for maintaining network security, safeguarding classified information, and meeting retention requirements related to data privacy. These measures are designed to protect both the users and the integrity of the systems.
Common Errors and How to Avoid Them When Filling Out the Form
When completing the USFK JCISA form, users often encounter common mistakes that can lead to issues with submission. Be aware of the following pitfalls:
-
Leaving required sections blank or failing to provide complete information.
-
Neglecting to sign the form or missing critical checkboxes.
To avoid these errors, carefully review the form before submission, ensuring that all sections are properly filled out and validation steps are completed.
Additional Resources for Understanding the USFK JCISA Acceptable Use Policy
For users seeking further information about the USFK JCISA Acceptable Use Policy, various resources are available. Official guidelines and documents can enhance understanding and clarity regarding the policy.
Contact information for inquiries can provide immediate support for any questions. Users are also encouraged to pursue additional training or resources related to security to ensure comprehensive knowledge.
Maximize Your Experience with pdfFiller for the USFK JCISA Acceptable Use Policy
Utilizing pdfFiller can greatly enhance your experience when completing the USFK JCISA Acceptable Use Policy. The platform’s features facilitate smooth form completion and ensure security throughout the process.
pdfFiller employs robust security measures, protecting documents during editing and sharing. Take advantage of pdfFiller for a streamlined approach to filling out forms and ensuring compliance with the policy.
How to fill out the USFK Policy
-
1.Access pdfFiller and log in to your account or create a new one if you haven't done so.
-
2.In the search bar, type 'USFK JCISA Acceptable Use Policy' to find the form.
-
3.Once you locate the form, click on it to open in the pdfFiller editor.
-
4.Carefully read the instructions provided within the document to ensure understanding.
-
5.Begin filling in the required fields indicated on the form, using clear and precise information.
-
6.If applicable, gather necessary documentation or information, such as identification or security clearances, before starting the completion process.
-
7.Utilize pdfFiller’s features, like the text box tool, to add information into designated areas, and checkboxes for agreement sections.
-
8.Review your inputs for accuracy and completeness, ensuring adherence to the stated policies.
-
9.Once all fields have been completed, use the review function to double-check for any errors or missing information.
-
10.After finalizing the document, look for the 'Save' option to store your work in your pdfFiller account.
-
11.You can download the completed form for your records or use the submission options provided by pdfFiller to send it directly to the required recipient.

Who is required to sign the USFK JCISA Acceptable Use Policy?
All authorized users, including US and ROK personnel who access USFK JCISA C2 Systems, must sign the policy to acknowledge their understanding of the rules and responsibilities outlined.
What happens if I do not submit the completed form?
Failure to submit the completed form may result in restricted access to USFK systems, as it is a requirement for maintaining compliance with security protocols.
Can I edit the form after signing it?
Once you sign the USFK JCISA Acceptable Use Policy, you may need to create an amendment or a new form should changes be required, as the signed document is considered final.
What should I do if I encounter issues while filling out the form?
If you face any difficulties while filling out the form on pdfFiller, consider consulting the help section for guidance or reaching out to customer support for assistance.
Is notarization required for this form?
No, notarization is not required for the USFK JCISA Acceptable Use Policy, simplifying the completion process for users.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.