Last updated on May 31, 2015

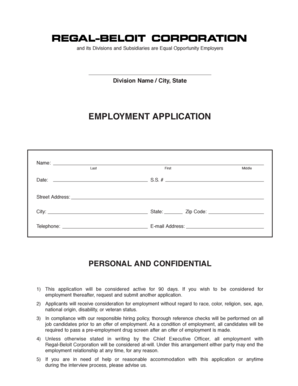
Get the free Security Incident Report Form
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is Security Incident Form
The Security Incident Report Form is a document used by organizations to report and document security incidents within 24 hours of detection.
pdfFiller scores top ratings on review platforms




Who needs Security Incident Form?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Security Incident Form
What is the Security Incident Report Form?
The Security Incident Report Form is a crucial document utilized by organizations to accurately record security incidents. This form is essential for ensuring that incidents are documented within 24 hours of detection. It provides a structured approach for organizations to assess and respond to security breaches effectively.
Understanding when and why to utilize the security incident report form can enhance incident response strategies, ensure compliance with regulatory requirements, and reinforce an organization's security posture.
Purpose and Benefits of the Security Incident Report Form
The timely completion of the Security Incident Report Form is vital for a range of reasons. First, it enables organizations to enhance their security measures by systematically analyzing reported incidents. Additionally, proper documentation supports compliance with legal and regulatory standards, ensuring that organizations retain adherence to necessary protocols.
-
Enhanced security by tracking and analyzing incidents
-
Facilitates compliance with regulatory requirements
-
Aids in better incident tracking and management
Key Features of the Security Incident Report Form
This form encompasses several key fields and attributes essential for comprehensive incident reporting. These include the Primary Contact, Computer Name, and IP Addresses associated with the incident. Furthermore, the form offers various options such as checkboxes for quick responses and sections designated for detailed descriptions of incidents.
-
Primary Contact for immediate communication
-
Fields for Computer Name and IP Addresses
-
Checkboxes for rapid assessment
Who Needs to Use the Security Incident Report Form?
The Security Incident Report Form is intended for a variety of roles within organizations. Primarily, IT departments, security professionals, and anyone responsible for managing data security within their sectors must familiarize themselves with this tool. Ensuring that those who handle incident reports understand its importance can significantly improve incident management processes.
-
IT departments
-
Security professionals
-
Business administrators
How to Fill Out the Security Incident Report Form Online
Completing the Security Incident Report Form online is a straightforward process. Users can access the form through pdfFiller, where they can navigate to each section and input the required information. It is advisable to be mindful of field requirements and common mistakes to ensure the form is completed accurately.
-
Access the form directly on pdfFiller
-
Complete each section accurately, following field prompts
-
Double-check for common pitfalls before submission
Submission Methods for the Security Incident Report Form
Once the Security Incident Report Form is filled out, users have multiple submission methods available. They can submit the completed form online, send it via email, or deliver it in person. Implementing tracking mechanisms for submissions can ensure that organizations confirm receipt of each report.
-
Online submission through pdfFiller
-
Emailing the completed form
-
In-person delivery for urgent incidents
Consequences of Not Filing or Late Filing of the Security Incident Report Form
Failing to file or submitting the Security Incident Report Form late can lead to significant repercussions. Organizations may face legal consequences and experience difficulties in maintaining compliance with established policies. Moreover, late filing increases the risk of vulnerabilities and may result in the loss of data integrity.
-
Potential legal ramifications
-
Increased risk of data breaches
-
Loss of data integrity
Security and Compliance for the Security Incident Report Form
Handling the Security Incident Report Form securely is paramount to protect sensitive data. pdfFiller employs stringent security measures, including encryption and compliance with relevant regulations. Implementing best practices for privacy and data protection during form completion and submission can further enhance security.
-
Encryption for data security
-
Compliance with HIPAA and GDPR regulations
-
Best practices for maintaining privacy during submission
Utilizing pdfFiller for the Security Incident Report Form
pdfFiller provides a robust platform that enhances the experience of filling out the Security Incident Report Form. Users can take advantage of features such as editing, eSigning, and creating fillable forms that simplify the reporting process. The platform is designed to make managing and processing security reports more efficiently.
-
Editing and annotating capabilities
-
eSigning for expedited approval
-
Creating fillable forms for easier completion
Get Started with the Security Incident Report Form Today!
Taking action to utilize the Security Incident Report Form via pdfFiller is crucial for proper incident reporting. Organizations should leverage pdfFiller's user-friendly interface and comprehensive support to enhance their reporting processes. Engaging with this tool can streamline operations and better prepare organizations to manage security incidents effectively.
How to fill out the Security Incident Form
-
1.To access the Security Incident Report Form on pdfFiller, visit the pdfFiller website and use the search bar to find the form by its name.
-
2.Once you locate the form, click on it to open it in pdfFiller's editing interface.
-
3.Before you start filling out the form, gather the necessary information, including incident details, contact information, and security tools used.
-
4.Begin filling out the fields starting with the 'Primary Contact' section, ensuring that all mandatory fields are properly completed.
-
5.Expand any sections with checkboxes and select the appropriate responses based on the incident being reported.
-
6.Continue to fill in fields such as 'Computer name', 'IP Addresses', and the detailed description of the incident, providing as much relevant detail as possible.
-
7.Use the navigation tools on the side of the pdfFiller interface to move between sections of the document efficiently.
-
8.Once you have completed all the required fields, review your entries for accuracy and completeness to ensure all essential information is captured.
-
9.After reviewing, save your progress and select the option to download the form or submit it directly through pdfFiller as per your organization's submission guidelines.

Who is eligible to use the Security Incident Report Form?
The Security Incident Report Form can be used by any organization that needs to document security incidents, including IT teams, business managers, and compliance officers.
What is the deadline for submitting the form?
The form should be completed and submitted within 24 hours of detecting a security incident to meet compliance and organizational standards.
How can I submit the Security Incident Report Form?
You can submit the form directly through pdfFiller by using the submission features available in the interface or by downloading it and sending it via email as per your organization’s procedures.
Are there any supporting documents required?
While specific supporting documents are not mandated for this form, providing screenshots or logs related to the incident can enhance the report's accuracy.
What are common mistakes to avoid when filling out this form?
Common mistakes include leaving mandatory fields blank, providing vague descriptions, and failing to collect all necessary information prior to completing the form.
How long does it take to process the Security Incident Report?
Processing times may vary, but organizations typically aim to address security incidents promptly after submission of the report.
What details should I include in the description of the incident?
Include specific information such as the nature of the incident, affected systems, actions taken, and any immediate responses implemented to manage the breach.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.