Last updated on Feb 11, 2015

Get the free Activity Security Checklist
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

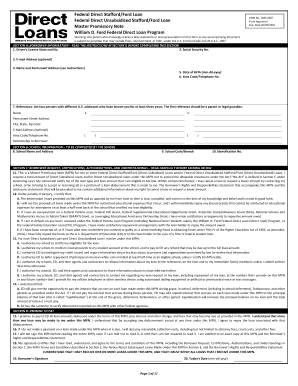
What is Security Checklist
The Activity Security Checklist is a fillable form used by organizations to conduct security inspections of work areas and ensure compliance with security protocols.
pdfFiller scores top ratings on review platforms




Who needs Security Checklist?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Security Checklist
What is the Activity Security Checklist?
The Activity Security Checklist is a pivotal form utilized for conducting security inspections. This checklist plays a significant role in ensuring compliance with security protocols by providing a structured approach to assessing a work area's security. It is aligned with the guidelines established by the National Archives and Records Administration (NARA) and the Information Security Oversight Office (ISOO). Additionally, this form serves as a daily security report, allowing for the consistent monitoring of security practices within organizations.
Purpose and Benefits of the Activity Security Checklist
The Activity Security Checklist is essential for government entities and organizations as it identifies potential security vulnerabilities effectively. Regular inspections supported by this checklist are crucial for maintaining a secure work environment. Moreover, utilizing this tool aids in compliance with federal security regulations, thereby reinforcing the organization’s commitment to safeguarding sensitive information.
Key Features of the Activity Security Checklist
This checklist is designed with several key features that enhance its effectiveness:
-
Fillable fields and checkboxes tailored for easy data entry.
-
A clear layout that facilitates user understanding and completion.
-
Initials requirement for each day’s reporting, ensuring accountability.
-
Incorporation of compliance details linked to 32 CFR part 2001.
Who Needs the Activity Security Checklist?
The primary users of the Activity Security Checklist include various government agencies and departments mandated to carry out security inspections. Additionally, personnel in specific roles within organizations, such as security officers and compliance managers, find this form indispensable. Furthermore, contractors who collaborate with government agencies are often required to utilize this checklist to adhere to security protocols.
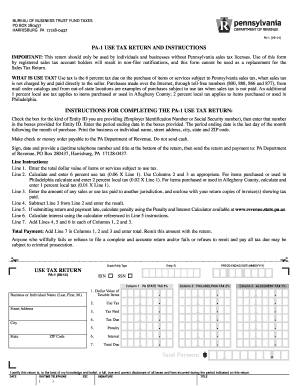
How to Fill Out the Activity Security Checklist Online
Completing the Activity Security Checklist online involves a straightforward process:
-
Access the online version of the checklist through the designated platform.
-
Follow field-by-field instructions to ensure accurate completion.
-
Review your entries to guarantee a thorough and complete submission.
It is advisable to check your responses multiple times to reduce errors.
Digital Signature vs. Wet Signature Requirements
Signing the Activity Security Checklist can be accomplished through digital signatures, which are considered legitimate. However, there may be instances where a wet signature is necessary. To navigate these requirements smoothly, users can utilize pdfFiller, which provides secure eSigning options for this form.
Where to Submit the Activity Security Checklist
Once completed, the Activity Security Checklist must be submitted according to established guidelines. Users should be aware of the specific submission methods available and any associated deadlines to ensure timely processing. Additionally, tracking the submission status is crucial for maintaining accountability and ensuring records are properly documented.
Common Errors and How to Avoid Them
When filling out the Activity Security Checklist, errors can often occur. Common pitfalls include:
-
Incomplete fields or failure to initial required entries.
-
Overlooking compliance details that need to be noted.
To minimize mistakes, it is essential to conduct a thorough review before submission and double-check all information for accuracy.
Importance of Security and Compliance for the Activity Security Checklist
Security and compliance are paramount when using the Activity Security Checklist. Adhering to data protection measures is essential for aligning with regulatory requirements. pdfFiller enhances security through features like 256-bit encryption, crucial for safeguarding sensitive forms. Non-compliance or inadequate record-keeping can lead to significant implications for organizations, emphasizing the need for diligence in security practices.
Optimize Your Experience with pdfFiller and the Activity Security Checklist
Utilizing pdfFiller for filling out the Activity Security Checklist can significantly enhance your experience. The platform provides efficient tools for editing and eSigning, making it easier for users to manage their documents. With the convenience of cloud access and dedicated support, users can effectively navigate the checklist completion process, ensuring a smooth workflow.
How to fill out the Security Checklist
-
1.To access the Activity Security Checklist on pdfFiller, go to the pdfFiller website and use the search function to find the form by name.
-
2.Once located, click on the form to open it in the pdfFiller editor, where you can start making your entries.
-
3.Before starting, gather necessary information such as the list of items to be checked and any relevant security protocols that apply to your work area.
-
4.Begin by filling in all required fields, which may include sections for checklist items. Use the filling tools provided by pdfFiller, like text boxes and checkboxes, to complete the form.
-
5.Review your entries to ensure all items are marked off according to the security criteria. Pay special attention to ensure initials are added for daily reports as required.
-
6.Once the form is completed to satisfaction, utilize pdfFiller's review functions to check for errors or omissions before finalizing.
-
7.Finally, save or download the form in your preferred format. If necessary, submit the completed checklist as instructed, ensuring it reaches the appropriate office or department.

Who is eligible to use the Activity Security Checklist?
The Activity Security Checklist is intended for use by government employees and security professionals responsible for conducting inspections across various work areas.
Are there any deadlines for submitting this checklist?
While specific deadlines are not mentioned, it is recommended to complete and submit the Activity Security Checklist regularly to maintain compliance with security protocols.
How should I submit the completed checklist?
Completed checklists can typically be submitted via email or the designated departmental submission portal, depending on your organization's policies.
What supporting documents do I need to complete this form?
You may need prior security inspection reports, a list of current security protocols, and any relevant incident reports, if applicable.
What are common mistakes to avoid when filling out the checklist?
Common mistakes include leaving fields uncompleted, forgetting to initial daily reports, and not reviewing the form for accuracy before submission.
How long does it take to process the submitted checklist?
Processing times may vary by department, but typically expect a response within one to two weeks after submission.
Is there a fee associated with this form?
There are no fees associated with completing or submitting the Activity Security Checklist, as it is part of standard compliance procedures.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.