Last updated on Feb 17, 2015

Get the free Activity Security Checklist Form
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

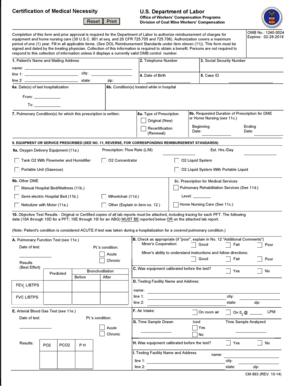
What is Security Checklist
The Activity Security Checklist Form is a government form used by organizations to conduct security inspections of work areas, ensuring compliance with NARA/ISOO regulations.
pdfFiller scores top ratings on review platforms




Who needs Security Checklist?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Security Checklist
What is the Activity Security Checklist Form
The Activity Security Checklist Form is an essential tool used to conduct thorough security inspections in work areas. This form is designed to support compliance with security measures as mandated by governing bodies such as NARA/ISOO, aligned with regulations like 32 CFR Part 2001 and Executive Order 13526. By providing a structured approach to security checks, it plays a critical role in establishing accountability and ensuring operational security.
-
Overview of the form and its historical background.
-
Clarification of its importance in security inspections.
-
Connection to relevant regulatory authorities.
Purpose and Benefits of the Activity Security Checklist Form
Utilizing the Activity Security Checklist Form is crucial for maintaining safety and compliance within any organization. Regular inspections of work areas bolster security protocols and promote a culture of vigilance and accountability. This form not only assists users in meeting regulatory requirements but also simplifies the security reporting process.
-
Facilitates systematic and regular security inspections.
-
Enhances accountability and compliance for users.
-
Streamlines the security reporting process.
Key Features of the Activity Security Checklist Form
The Activity Security Checklist Form is equipped with several noteworthy features that enhance usability and compliance. It includes various fillable fields and checkboxes, making it adaptable for daily reporting needs. With an intuitive layout, users can navigate the form easily, ensuring all necessary security measures are accounted for during inspections.
-
Fillable fields and checkboxes for efficient reporting.
-
User-friendly design that fosters easy navigation.
-
Focus on compliance with vital security measures.
Who Needs the Activity Security Checklist Form?
This form is relevant for a broad range of professionals and organizations tasked with maintaining security. Various roles within government agencies and security organizations utilize the Activity Security Checklist Form to ensure compliance and thorough inspections in their respective environments.
-
Government agencies involved in security oversight.
-
Security professionals conducting regular inspections.
-
Organizations interfacing with sensitive information.
How to Fill Out the Activity Security Checklist Form Online
Completing the Activity Security Checklist Form online is a straightforward process, especially with tools like pdfFiller at your disposal. To begin, access the form through the platform, where you will find various features designed for easy editing and completion.
-
Log in to pdfFiller and locate the Activity Security Checklist Form.
-
Utilize fillable fields for accurate input of necessary information.
-
Double-check entries to ensure compliance and accuracy.
Common Errors and How to Avoid Them When Filling the Form
Avoiding common mistakes while completing the Activity Security Checklist Form is crucial for successful submissions. Many users overlook necessary checks or details that can lead to issues in processing or compliance.
-
Frequent pitfalls include missing signatures and unchecked boxes.
-
Double-checking all entered information can prevent rejections.
-
Emphasizing accuracy in all aspects of security documentation is vital.
Submitting the Activity Security Checklist Form: Methods and Requirements
Submitting the Activity Security Checklist Form can be done through various methods, ensuring convenience for users. Whether opting for online submission or traditional methods, understanding the requirements is essential for timely processing.
-
Available submission methods include online and offline options.
-
Ensure all required information accompanies the form.
-
Be mindful of deadlines and follow-up processes once submitted.
Security and Compliance Considerations for the Activity Security Checklist Form
When handling the Activity Security Checklist Form, attention to security and compliance is paramount. It is essential to employ data protection measures to secure sensitive information during the form completion process.
-
Utilizing robust encryption and secure platform features enhances data protection.
-
Complying with privacy regulations is necessary during form handling.
-
Understanding record retention policies ensures effective management.
How pdfFiller Can Help with the Activity Security Checklist Form
pdfFiller provides numerous features to streamline the handling of the Activity Security Checklist Form. From editing to e-signing, these capabilities enhance user efficiency and security during the form submission process.
-
Editing and annotating capabilities simplify form customization.
-
Advanced security features, including encryption, ensure data safety.
-
Efficient submission and management tools create a seamless experience.
Next Steps for Completing Your Activity Security Checklist Form
Engaging with helpful platforms like pdfFiller will enhance the experience of completing the Activity Security Checklist Form. Starting promptly with a digital solution can significantly improve form management.
-
Begin using pdfFiller for an efficient form-filling experience.
-
Follow straightforward guides to get started quickly.
-
Emphasizing the benefits of digital platforms can enhance overall security processes.
How to fill out the Security Checklist
-
1.To access the Activity Security Checklist Form on pdfFiller, visit the website and use the search bar to find the form by typing its name.
-
2.Once located, click on the form to open it in the pdfFiller interface.
-
3.Review the form's fields and note any predefined checkboxes and blank spaces meant for user input.
-
4.Before beginning, gather necessary information about the security items that need to be checked in your work area.
-
5.Click on each field within the form to start filling in the details, using pdfFiller’s tools to add information or check boxes as required.
-
6.Be sure to initial any daily reporting sections as you complete each inspection item.
-
7.After filling in all required fields, double-check the information for accuracy and completeness using the preview feature.
-
8.When satisfied with your entries, click on the save button to keep a copy of the completed form.
-
9.You can then download the filled form to your device or submit it directly through pdfFiller’s submission options provided on the platform.

Who is eligible to complete the Activity Security Checklist Form?
Any individual or organization involved in security assessments within government or private sectors can complete this form, provided they have the authority to conduct such inspections.
What is the deadline for submitting the Activity Security Checklist Form?
There is typically no formal deadline for this form; however, it is recommended to complete and submit it regularly to maintain compliance and ensure ongoing security.
How can I submit the completed Activity Security Checklist Form?
You can submit the completed form directly through pdfFiller by using the provided submission options, or you can download it and submit it via email or mail, as required by your organization.
Are there any supporting documents required when using this form?
Generally, no additional documents are required with the Activity Security Checklist Form unless specified by your agency’s policies. However, having a security inspection report can be beneficial for reference.
What common mistakes should I avoid when filling out this form?
Ensure all fields are filled out completely and accurately. Common mistakes include skipping required initials, failing to check all necessary items, and not reviewing for correct information before submission.
How long does it take to process the Activity Security Checklist Form?
Processing time may vary based on the agency's internal review system. Typically, if submitted electronically via pdfFiller, processing can take anywhere from a few hours to a few days.
What should I do if I encounter issues accessing the form?
If you have trouble accessing the Activity Security Checklist Form on pdfFiller, check your internet connection or try using a different browser. You can also contact pdfFiller support for assistance.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.