Last updated on Mar 17, 2015

Get the free Security Incident Report Form
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

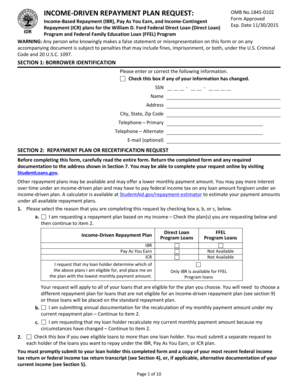
What is Security Incident Form
The Security Incident Report Form ISO-02 is a legal document used by employees of the Department of General Services in California to report security incidents involving sensitive information.
pdfFiller scores top ratings on review platforms




Who needs Security Incident Form?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Security Incident Form
What is the Security Incident Report Form?
The Security Incident Report Form ISO-02 is a crucial document designed for California state employees. This form serves the primary function of reporting security incidents involving sensitive information. It facilitates detailed documentation of incidents, which is vital for compliance and corrective action to mitigate future risks and enhance data security.
By utilizing the California security form, employees can systematically report any security breaches, ensuring that all incidents are properly documented and investigated.
Purpose and Benefits of the Security Incident Report Form
The Security Incident Report Form is essential for maintaining data integrity and compliance with regulatory standards. By formalizing incident reporting, it provides several key benefits:
-
Formal documentation protects sensitive information and ensures adherence to state regulations.
-
Assists in developing effective incident response and prevention strategies.
-
Promotes accountability among personnel involved in incident reporting.
Key Features of the Security Incident Report Form
This form boasts several important characteristics that enhance its usability:
-
Fillable fields for entering incident details, corrective actions, and required signatures.
-
Clear completion instructions to ensure comprehensive and accurate reporting.
-
A managerial approval requirement to bolster accountability and oversight.
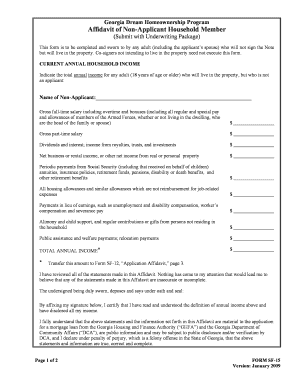
Who Needs to Use the Security Incident Report Form?
The Security Incident Report Form is predominantly utilized by specific personnel within the Department of General Services in California. This includes:
-
Employees who are responsible for reporting security incidents.
-
Managers who are required to review and approve the reports.
-
Understanding each role is crucial for streamlining the reporting process.
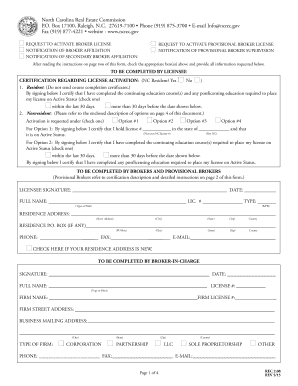
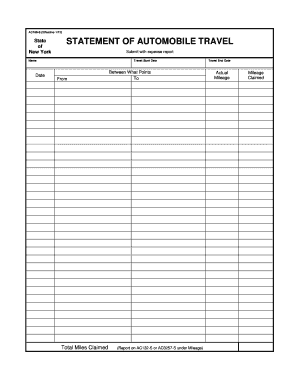
How to Fill Out the Security Incident Report Form Online (Step-by-Step)
Filling out the Security Incident Report Form online can be easily accomplished by following these steps:
-
Access the pdfFiller online platform to begin.
-
Locate the Security Incident Report Form and open it for editing.
-
Fill in the required fields, including incident details and corrective actions.
-
Review the form carefully for accuracy and completeness.
-
Obtain managerial approval and signatures before submission.
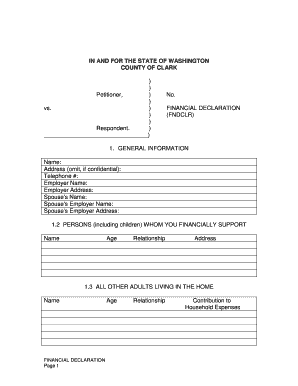
Submission Process for the Security Incident Report Form
Once the Security Incident Report Form is completed, it can be submitted through various methods:
-
Online portal via pdfFiller.
-
Email submission to the appropriate office.
-
Physical delivery of the printed form to designated locations.
Adhering to submission deadlines and local guidelines is critical to ensure timely processing and acknowledgment of the report.
Security and Compliance Considerations for Filing the Form
When submitting the Security Incident Report Form, it is imperative to consider security and compliance factors:
-
Implement privacy and data protection measures during the completion and submission process.
-
Ensure compliance with relevant regulations, such as HIPAA and GDPR.
-
Follow best practices for the secure handling of sensitive information throughout the reporting process.
What Happens After You Submit the Security Incident Report Form?
After submitting the Security Incident Report Form, the following steps typically occur:
-
The Information Security Office will review the submitted report within established timelines.
-
Feedback may be provided, or additional information requests may be issued as necessary.
-
Users should be informed on how to follow up on the submission status and any required next steps.
Common Errors and How to Avoid Them When Filing the Security Incident Report Form
To avoid delays in processing, here are some common errors to watch for while completing the form:
-
Missing fields or incomplete information provided.
-
Unclear descriptions of the incidents reported.
-
Failure to involve managers early on for their signatures and approvals.
A checklist can be particularly helpful for reviewing the form prior to submission.
Unlock Efficient Form Management with pdfFiller
Utilizing pdfFiller can greatly enhance your experience with form management:
-
Edit, sign, and share the Security Incident Report Form securely.
-
The platform is user-friendly, making it easy to complete the necessary documentation.
-
pdfFiller guarantees strong security features that protect sensitive information.
How to fill out the Security Incident Form
-
1.Access pdfFiller and search for the Security Incident Report Form ISO-02 by entering the form name in the search bar.
-
2.Once the form appears, click on it to open and review the layout and fields provided.
-
3.Before starting to fill out the form, gather all necessary information, including details of the incident, any corrective actions taken, and signatures from both the person reporting and their manager.
-
4.Begin filling in the form by clicking on each field. Use pdfFiller's features to enter text in the designated areas smoothly.
-
5.For checkboxes, click to select the appropriate options regarding the incident details and actions taken.
-
6.Review all entered information for accuracy and completeness, confirming that all required fields are filled out correctly.
-
7.Once you are satisfied with the form, use the pdfFiller tools to save your progress or finalize it by downloading a copy.
-
8.To submit the completed form, follow the prompts on pdfFiller to either email it directly to the designated recipient or save it for later submission.

Who is eligible to use the Security Incident Report Form?
This form is specifically designed for employees of the Department of General Services in California who need to report security incidents involving sensitive information.
What is the deadline for submitting the Security Incident Report Form?
While specific deadlines may vary by incident, it is recommended to submit the Security Incident Report Form as soon as possible to ensure prompt response from the Information Security Office.
How can I submit the completed Security Incident Report Form?
You can submit the completed form directly through pdfFiller by using the email feature or by downloading it for personal submission to the Information Security Office.
Are there any supporting documents required with the form?
Typically, the Security Incident Report Form does not require additional documentation; however, it’s best to include any relevant incident details or evidence if available.
What common mistakes should I avoid when filling out this form?
Ensure that all fields are completed accurately, especially the incident details. Avoid leaving any required fields empty and double-check for typos before submission.
How long does it take to process the Security Incident Report Form?
Processing times may vary based on the nature of the incident and the workload of the Information Security Office, so it’s advisable to follow up if you do not receive confirmation within a reasonable timeframe.
What happens after I submit the Security Incident Report Form?
Once submitted, the Information Security Office will review the report, investigate the incident, and follow up with you regarding any necessary actions or outcomes.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.