Last updated on Mar 25, 2015

Get the free Suspicious Activity Report Instructions
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is SAR Instructions
The Suspicious Activity Report Instructions is a legal notice document used by financial institutions to report suspicious transactions to authorities.
pdfFiller scores top ratings on review platforms




Who needs SAR Instructions?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to SAR Instructions
What is the Suspicious Activity Report (SAR) Instructions?
The Suspicious Activity Report (SAR) Instructions provide financial institutions with guidelines for reporting suspicious activities. This form is crucial in financial crime reporting and compliance, as it fulfills requirements outlined in the Bank Secrecy Act. Adhering to these guidelines is essential for institutions to maintain regulatory compliance.
Purpose and Benefits of the Suspicious Activity Report Instructions
Financial institutions must report suspicious activities to mitigate risks associated with financial crimes. Accurate and timely reporting not only protects the institutions under legal provisions but also assists regulatory bodies in monitoring compliance. Legal protections offer anonymity to the reporting parties, fostering a culture of accountability while ensuring regulatory standards are met.
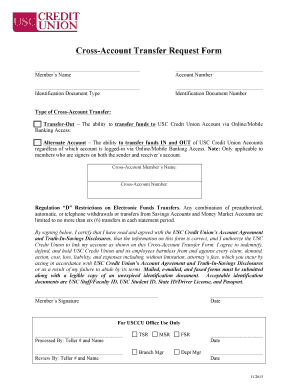
Who Needs to Use the Suspicious Activity Report Instructions?
Various parties within financial institutions are required to comply with the SAR instructions. These typically include banks, credit unions, and other financial entities, with specific roles like compliance officers and designated reporting agents responsible for filing. Any financial professional who encounters suspicious transactions must be familiar with these instructions to ensure adherence to compliance standards.
When and How to Submit the Suspicious Activity Report Instructions
Filing the SAR must occur within specific timelines to remain compliant. Institutions are usually required to submit reports within 30 days of detecting suspicious activity. The submission process can occur through electronic systems or paper forms, depending on the institution’s capabilities. Failing to file on time may result in regulatory penalties and increased scrutiny by authorities.
How to Fill Out the Suspicious Activity Report Instructions Online
Completing the SAR involves several critical steps to ensure accuracy. First, gather necessary information before you begin filling out the form. Be attentive to the following sections:
-
Identification of the subject of the report
-
Description of the suspicious transaction
-
Details of the reporting institution
Common pitfalls include omitting necessary details or providing inaccurate information. Review your entries thoroughly to prevent errors before submission.
Required Documents and Supporting Materials for the SAR
To accurately complete the SAR, specific documents are essential. You will need to gather the following:
-
Identification documents of involved parties
-
Transaction history and relevant data
-
Supporting documents related to the suspicious activity
Having a checklist can facilitate effective document preparation, ensuring all essential materials are collected before filing.
Common Errors and How to Avoid Them with the SAR Instructions
While filling out the SAR form, several frequent mistakes can occur. Common errors include:
-
Incomplete fields or missing signatures
-
Incorrect identification numbers
-
Failure to provide sufficient details about the suspicious activity
Best practices involve reviewing the form thoroughly and using a validation checklist to enhance accuracy before submitting it. This step is essential for maintaining compliance.
Security and Compliance Considerations for the Suspicious Activity Report Instructions
Security measures play a vital role in handling the sensitive information contained in SAR submissions. Institutions must ensure that protections such as encryption and secure access are in place. Emphasizing data privacy during submission and storage is critical to comply with regulations and safeguard client information.
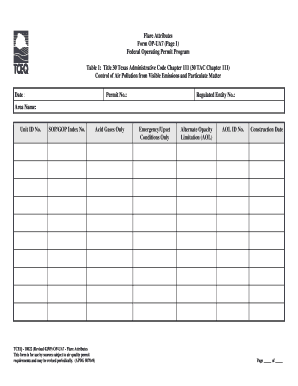
Sample of a Completed Suspicious Activity Report Instructions
Reviewing a filled-out SAR can serve as an invaluable template for institutions. A completed example illustrates how to properly complete each section of the form, showcasing vital components that require attention. Different scenarios may affect how the report is filled out, demonstrating the need for adaptation based on specific details of the case.
Experience Convenience with pdfFiller to Complete Your SAR Instructions
Utilizing pdfFiller allows users to efficiently complete and submit their SAR. The platform provides features geared towards document management, ensuring that submissions are accurate and secure. Commitment to compliance and thoroughness is paramount when filling out this vital form.
How to fill out the SAR Instructions
-
1.To access the Suspicious Activity Report Instructions on pdfFiller, go to the pdfFiller website and search for the form by its name or use the provided URL if available.
-
2.Once opened, familiarize yourself with the layout of the form, noting where input fields, checkboxes, and sections for text are located.
-
3.Before filling out the form, gather all pertinent information, including details of the suspicious transactions, involved parties, and any relevant documentation you might require.
-
4.Start by clicking on each input field and entering the required information. Use the tooltips provided by pdfFiller for guidance on what details are necessary for each section.
-
5.If there are checkboxes, simply click on them to select or deselect options as applicable to the suspicious activity being reported.
-
6.Continue scrolling through the document, making sure to complete all labeled fields to ensure comprehensive reporting.
-
7.Once you have filled out the form, review your entries for any errors or omissions. Pay particular attention to the clarity and accuracy of the names and addresses included.
-
8.After finalizing your entries and ensuring the form is complete, save your work. You can choose to download it to your device or submit it directly through pdfFiller.
-
9.For submission, follow the instructions provided by your financial institution regarding delivery methods—this may include electronic or physical submissions to appropriate authorities.

Who is eligible to fill out the Suspicious Activity Report Instructions?
Any financial institution or entity involved in the financial sector is eligible to fill out the Suspicious Activity Report Instructions, including banks, credit unions, and other regulated financial businesses.
Is there a deadline for submitting the Suspicious Activity Report?
Yes, there are specific timelines for reporting depending on the nature of the suspicious activity. It is typically advisable to submit the report as soon as you identify a suspicious transaction.
How can I submit the completed Suspicious Activity Report?
You can submit the completed Suspicious Activity Report either electronically through designated submission processes or physically by mailing it to the appropriate regulatory agency.
What supporting documents are required with the report?
Supporting documents may include transaction records, identification of involved parties, and any relevant correspondence or evidence that substantiates the suspicion of financial crime.
What common mistakes should I avoid when filling out the report?
Common mistakes include leaving fields blank, providing inaccurate information, and failing to check compliance with local reporting laws. Ensure every section is completed accurately to avoid delays.
What is the processing time for the Suspicious Activity Report?
Processing times can vary based on jurisdiction and the nature of the report. Generally, regulatory agencies aim to review the reports promptly but timelines may differ between agencies.
Are there any fees associated with filing the Suspicious Activity Report?
Typically, there are no fees involved in filing the Suspicious Activity Report. However, check with your financial institution for any operational costs related to document preparation or submission.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.