Last updated on Mar 26, 2015

Get the free Reporting Center Security Access Form
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

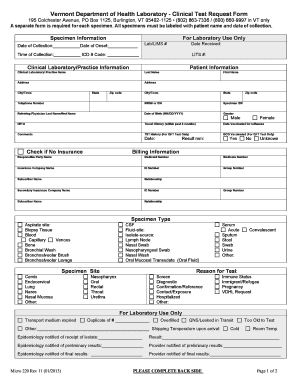
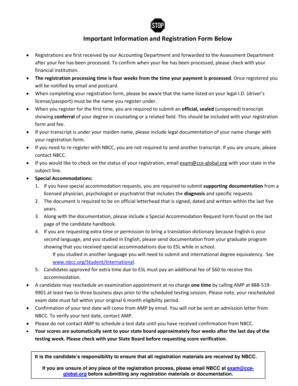
What is Security Access Form
The Reporting Center Security Access Form is a government document used by individuals within organizations to request access to sensitive financial, personnel, and workforce reports.
pdfFiller scores top ratings on review platforms




Who needs Security Access Form?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Security Access Form
What is the Reporting Center Security Access Form?
The Reporting Center Security Access Form is a crucial document used to request security access to various critical reports and systems within the National Finance Center. Its significance lies in managing the access to sensitive financial data and personnel information.
This form is issued by the relevant authorities within the US government and adheres to established regulations to ensure secure data handling. Individuals involved include users seeking access, their supervisors, and administrators responsible for approvals.
Purpose and Benefits of the Reporting Center Security Access Form
The primary purpose of the Reporting Center Security Access Form is to facilitate controlled access to essential financial, personnel, and workforce reports. By utilizing this form, organizations can effectively manage who accesses sensitive data.
Benefits of this structured approach include enhancing data security, ensuring compliance with government standards, and streamlining the process of access management. Effective usage of the government security access form correlates directly with improved operational efficiency.
Key Features of the Reporting Center Security Access Form
The Reporting Center Security Access Form includes several essential elements necessary for effective processing. These include
-
User information, including identification details
-
Defined access levels based on roles
-
Requirements for supervisor and administrator approvals
The form’s structure features clearly labeled sections and input fields to guide users during the completion process, ensuring all necessary data is collected accurately.
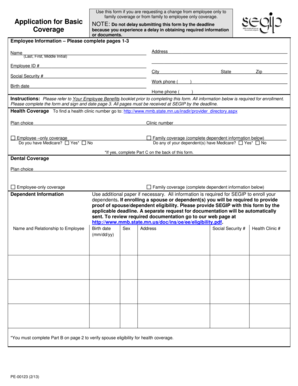
Eligibility Criteria for the Reporting Center Security Access Form
Not all individuals can apply for the Reporting Center Security Access Form. Only designated roles, such as Users, Supervisors, and Administrators, are authorized to request access. Each has a clear responsibility in the approval workflow.
It is essential for Supervisors and Administrators to sign off on the form to validate the request, ensuring that all security protocols are adhered to. This multi-layered approval process plays a crucial role in preventing unauthorized access.
How to Fill Out the Reporting Center Security Access Form Online
Filling out the Reporting Center Security Access Form online involves a few straightforward steps:
-
Access the form via the designated platform.
-
Complete each section, ensuring to provide accurate user details.
-
Seek the necessary approvals from supervisors and administrators.
-
Double-check all fields to avoid incomplete submissions.
Before beginning, it is beneficial to gather required information, including 'USER SIGNATURE DATE' and 'SUPERVISOR AUTHORIZATION DATE,’ to streamline the process.
Common Errors and How to Avoid Them When Completing the Reporting Center Security Access Form
When completing the Reporting Center Security Access Form, several common errors can arise. These include missing signatures, incomplete sections, or incorrect user information.
To prevent these mistakes, it is advisable to double-check all fields, ensure supervisor approvals are in place, and thoroughly review the form before submission to minimize the chance of delays.
Submission Methods for the Reporting Center Security Access Form
After completing the Reporting Center Security Access Form, it can be submitted through multiple channels. Applicants should confirm the submission methods available, whether they’re electronic or paper-based.
Among the options, electronic submission through platforms like pdfFiller is encouraged, providing a user-friendly experience for submitting the completed form securely.
Confirmation and Tracking Your Submission of the Reporting Center Security Access Form
After submitting the Reporting Center Security Access Form, applicants can expect various responses based on the review process. Understanding how to track the status of your application is essential.
Be prepared to follow up for any issues that may arise, and utilize any available tracking tools to monitor the progress of your submission.
Security and Compliance When Using the Reporting Center Security Access Form
Security is paramount when handling the Reporting Center Security Access Form. Platforms like pdfFiller implement stringent measures, including 256-bit encryption to protect sensitive information.
Furthermore, compliance with regulations such as HIPAA and GDPR ensures that user privacy is upheld during form handling, making it a reliable choice for individuals concerned with data security in the process of accessing government forms.
Streamline Completing the Reporting Center Security Access Form with pdfFiller
Utilizing pdfFiller to complete the Reporting Center Security Access Form can significantly enhance the experience. This platform offers unique features that facilitate efficient management of the form, from editing to eSigning.
By leveraging these capabilities, users can ensure a smoother process, reducing frustration and time spent on administrative tasks associated with government forms.
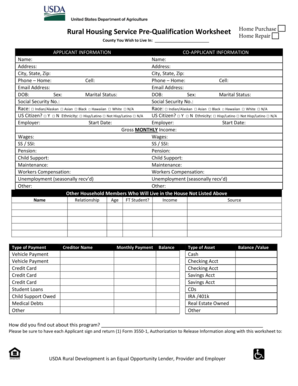
How to fill out the Security Access Form
-
1.Begin by accessing pdfFiller and searching for the Reporting Center Security Access Form.
-
2.Open the form in the editor where you will find labeled fields and checkboxes.
-
3.Gather all necessary information including your role, required access levels, and organizational structure details before starting to fill the form.
-
4.Input your personal details in the appropriate sections clearly marked on the form.
-
5.Make sure to provide all necessary approvals from supervisors and administrators as instructed.
-
6.Use the available fields for signatures, ensuring the date is included along with each signature.
-
7.Review your completed form thoroughly to ensure that all fields are filled correctly and all necessary approvals are included.
-
8.Once satisfied, save your progress frequently to avoid data loss.
-
9.After finalizing the form, use the 'Download' option on pdfFiller to save it or the 'Submit' option to send it directly as per your organization’s submission procedures.

Who is eligible to fill out the Reporting Center Security Access Form?
The form is designed for users within an organization who require access to sensitive reports, including employees, supervisors, and administrators involved in managing financial and personnel data.
What supporting documents are required with the form?
Typically, the form requires approvals from your supervisor and administrator, detailing your access needs. Ensure you have their consent before submitting the form.
How can I submit the Reporting Center Security Access Form?
You may submit the form through pdfFiller's submission features, which allows you to send it directly or download it for email submission based on your organization's guidelines.
What common mistakes should I avoid when completing this form?
Avoid incomplete fields and ensure all required signatures are obtained. Double-check that your access level request aligns with your job responsibilities.
Is there a deadline for submitting the form?
Deadlines may vary based on your organization’s regulations. It’s advisable to submit the form as soon as you gather all necessary approvals to facilitate timely access.
What is the processing time for the access request after submission?
Processing times generally depend on your organization’s policies and may take several days. Check with your supervisor for more specific timelines.
Does the Reporting Center Security Access Form require notarization?
No, this form does not require notarization, making it easier to complete and submit it through the designated channels within your organization.
Related Catalogs
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.