Get the free Texas-State-Device-Encryption-Exception-Request-Form. ...
Get, Create, Make and Sign texas-state-device-encryption-exception-request-form
Editing texas-state-device-encryption-exception-request-form online
Uncompromising security for your PDF editing and eSignature needs
How to fill out texas-state-device-encryption-exception-request-form
How to fill out texas-state-device-encryption-exception-request-form
Who needs texas-state-device-encryption-exception-request-form?
Texas State Device Encryption Exception Request Form Guide
Overview of the Texas State Device Encryption Exception Request Form
The Texas State Device Encryption Exception Request Form is a vital document for individuals or teams seeking authorization for devices that do not meet the standard encryption requirements set forth by Texas state regulations. This form serves an essential purpose in maintaining the integrity and security of sensitive data while allowing flexibility in certain cases.
Understanding who needs to use this form is crucial for compliance. The form is primarily utilized by employees of Texas state agencies, contractors, and other authorized users dealing with sensitive or confidential information in their job roles.
Assessing eligibility for an exception
Eligibility for a device encryption exception is determined by specific criteria aimed at ensuring that requests are justified and necessary. Applicants must demonstrate a legitimate need for the exception, which may include compatibility issues, technical limitations, or unique operational needs.
Identifying applicable devices plays a critical role in the eligibility assessment. The exception applies to devices that would normally require encryption but have a valid circumstance for exemption, such as older hardware or specialized equipment that doesn't support current encryption standards.
High-risk scenarios often necessitate careful evaluation. For example, devices handling classified government information may qualify for exceptions if encryption methods hinder performance or usability.
Step-by-step instructions for completing the form
Completing the Texas State Device Encryption Exception Request Form involves accurately filling out several sections. Each section collects critical information that will guide the approval process effectively.
Section 1: User information
The first section gathers personal user information, such as the applicant's name and the department they belong to. It is essential to fill all required fields completely to avoid any holdups in the processing.
Section 2: Device information
Section two requests detailed information about the specific device for which the exception is being requested. It's crucial to accurately report the device type and include the serial number to prevent miscommunication.
Section 3: Justification for exception
This section requires a clear and concise justification for the exception request. Applicants must explain why encryption is not feasible or necessary for the device in question. Supporting documentation is encouraged to back the claim effectively.
Section 4: Review and submission process
Understanding the review and submission protocol is essential. Once the form is completed, it undergoes an internal review by designated authorities prior to final approval. This review process helps to maintain stringent security standards.
Tips for optimizing your request
Submitting a well-prepared request is vital for a smooth approval process. Here are some common mistakes to avoid: incomplete information, lack of supporting documentation, and unclear justifications. Ensuring clarity and completeness in your form can significantly enhance the likelihood of approval.
Additionally, consider formatting your request for better readability. Clear headings and properly structured paragraphs can make a world of difference in how your request is perceived.
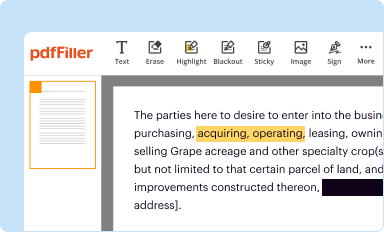
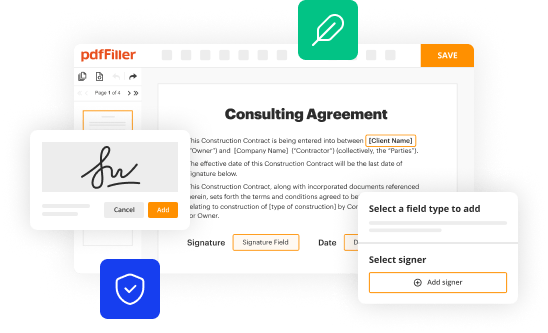
Interactive tools for form management
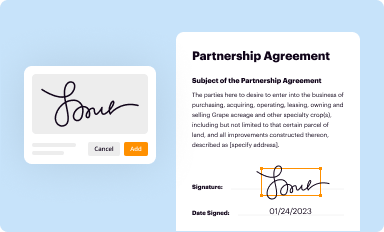
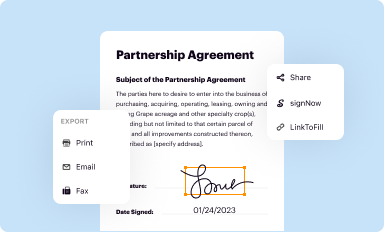
pdfFiller provides various tools to enhance your experience while filling out the Texas State Device Encryption Exception Request Form. With online editing features, users can adjust text easily and ensure all necessary details are included.
eSigning capabilities allow for a secure and efficient means of signing the form without needing to print it out first. This streamlines the approval process while maintaining compliance with digital standards.
Collaborative functionality
Moreover, pdfFiller’s platform supports collaborative functionality, enabling teams to work together in real time on the form. This feature is particularly beneficial for departments with multiple stakeholders involved in the exception request process.
Security and compliance considerations
Device encryption is a fundamental aspect of information security. Adhering to encryption policies is essential for protecting sensitive data against unauthorized access. The process of requesting an exception can have significant implications for your organization’s overall security posture.
When granting an exception, it's vital to assess how it impacts your data protection standards. Being cognizant of potential vulnerabilities helps ensure that any exceptions made will still abide by overarching security protocols.
Frequently asked questions (FAQs)
Many users encounter similar queries regarding the Texas State Device Encryption Exception Request process. Common questions may include the types of devices eligible, the appropriate timelines for submission and approval, and how to troubleshoot submission issues that arise.
Clarifications regarding state policies can also streamline the process and ensure all applicants are well-informed. This is especially crucial for first-time applicants who may be unfamiliar with the requirements.
Resources and support
For assistance with the Texas State Device Encryption Exception Request Form, contacting support is recommended. Access contact information for direct inquiries or to seek guidance on filling out the form correctly.
Furthermore, links to related state policies and accessing additional forms can facilitate better compliance and understanding of system requirements.
Revision history and updates
Staying aware of revisions to the Device Encryption Exception Request Form is critical for compliance. Regular updates ensure that the form aligns with current technological advancements and security measures.
A clear record of important dates along with changes over time helps users remain informed about upcoming compliance deadlines.
Acknowledgments & approvals
Lastly, acknowledging the stakeholders involved in the development of this form is essential. Understanding who has approved the document can provide users context about its legitimacy and application across Texas state agencies.
The approval process overview highlights the meticulous nature of creating such documents to protect sensitive data effectively.






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How can I manage my texas-state-device-encryption-exception-request-form directly from Gmail?
How do I edit texas-state-device-encryption-exception-request-form online?
How do I edit texas-state-device-encryption-exception-request-form on an iOS device?
What is texas-state-device-encryption-exception-request-form?
Who is required to file texas-state-device-encryption-exception-request-form?
How to fill out texas-state-device-encryption-exception-request-form?
What is the purpose of texas-state-device-encryption-exception-request-form?
What information must be reported on texas-state-device-encryption-exception-request-form?
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.