Last updated on Sep 14, 2015

Get the free C-TPAT Security Profile Application
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

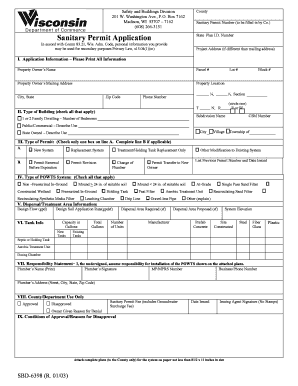
What is C-TPAT Application
The C-TPAT Security Profile Application is a business form used by foreign manufacturers to demonstrate adherence to C-TPAT minimum-security criteria for supply chain security certification.
pdfFiller scores top ratings on review platforms




Who needs C-TPAT Application?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to C-TPAT Application
What is the C-TPAT Security Profile Application?
The C-TPAT Security Profile Application is a crucial document designed for foreign manufacturers aiming to demonstrate compliance with security practices mandated by U.S. Customs and Border Protection. This application serves to illustrate adherence to C-TPAT's minimum-security criteria, showcasing how a manufacturing entity aligns with essential security measures.
Foreign manufacturers particularly benefit from completing this form, as it is a key element for meeting U.S. standards and ensuring that their security practices are robust. Understanding the C-TPAT Security Profile Application is vital for anyone involved in maintaining supply chain integrity and compliance.
Purpose and Benefits of the C-TPAT Security Profile Application
Completing the C-TPAT Security Profile Application holds numerous advantages for businesses. Primarily, it reinforces supply chain security, which is critical for operational success. By adhering to outlined security practices, foreign manufacturers enhance their credibility in the marketplace, which can lead to stronger business relationships.
Furthermore, proper adherence to the C-TPAT requirements can positively influence shipping efficiency. Manufacturers who maintain high compliance standards may notice a reduction in cargo discrepancies, thus streamlining their logistical operations.
Who Needs the C-TPAT Security Profile Application?
This application is primarily designed for foreign manufacturers that have supply chain roles involving transactions or shipments into the United States. Stakeholders such as supply chain security specialists and logistics coordinators may also need to participate in filling out the application.
It’s essential that these entities understand the importance of fulfilling business partner requirements related to security. Being proactive in completing the C-TPAT Security Profile Application can significantly benefit manufacturers in establishing trust and compliance across the supply chain.
Eligibility Criteria for the C-TPAT Security Profile Application
To submit the C-TPAT Security Profile Application, potential applicants must meet specific eligibility criteria. These criteria often include demonstrating established security practices that align with C-TPAT standards, along with relevant documentation that supports their application.
Applicants should be prepared to provide evidence of their existing security measures. Essential components include detailed descriptions of physical security implementations, personnel security verification procedures, and documentation regarding shipping and receiving practices.
How to Fill Out the C-TPAT Security Profile Application Online
Filling out the C-TPAT Security Profile Application online involves several steps to ensure accurate submission. Firstly, users should access the online form, where they will encounter various sections requiring specific information and document uploads.
-
Begin by providing necessary company information in the designated fields.
-
Upload supporting documents that validate your current security practices.
-
Carefully complete each section, ensuring data accuracy before moving on.
-
Perform validation checks to verify that all required fields are complete.
-
Finally, submit the application for processing.
Required Documents and Supporting Materials
When submitting the C-TPAT Security Profile Application, certain documents and materials must be prepared and included. These might involve security protocols, procedural documentation, and other relevant security evidence.
-
Security protocols detailing your current security measures.
-
Procedural documentation that outlines operational practices around security.
-
Any existing compliance certifications that reinforce your application.
Ensuring that these materials are gathered and organized effectively will facilitate smoother documentation processing during your application submission.
Common Errors and How to Avoid Them
Many applicants encounter pitfalls when completing the C-TPAT Security Profile Application. Common mistakes include missing information in required fields or submitting incomplete documentation.
To minimize these errors, it is advisable to double-check all entries before submission. Implement strategies such as performing a final review of uploaded documents and ensuring that all relevant sections are thoroughly completed to secure successful application processing.
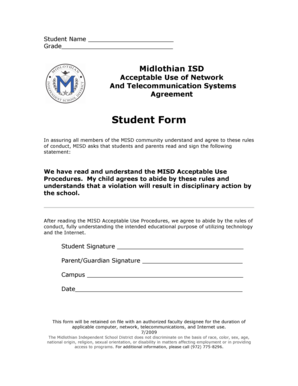
Security and Compliance for the C-TPAT Security Profile Application
Security is paramount when handling the C-TPAT Security Profile Application. The application process incorporates robust data protection measures to ensure the safety of sensitive information. Compliance with legal standards, such as HIPAA and GDPR, is crucial during this process.
pdfFiller aids in maintaining the highest levels of security for document processing and user data protection. Users can confidently submit their applications, knowing that their information is safeguarded throughout the application process.
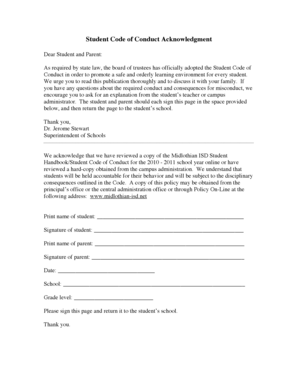
What Happens After You Submit the C-TPAT Security Profile Application
Post-submission, applicants can expect to receive confirmation of their application from the relevant authorities. It’s essential to track the status of the application to stay informed about processing timelines and any feedback received.
In the event that corrections or amendments are required, applicants should be prepared to act promptly based on any instructions provided after the initial submission. Understanding this process is key to maintaining an effective application flow.
Maximize Your C-TPAT Security Profile Application Experience with pdfFiller
Using pdfFiller for your C-TPAT Security Profile Application streamlines the form-filling process. Users benefit from a suite of editing tools that simplify the completion of documentation.
Additionally, pdfFiller’s security features ensure that all documents are handled with utmost care, protecting sensitive information. Leveraging this platform for all future document management needs can lead to enhanced efficiency in submitting necessary applications.
How to fill out the C-TPAT Application
-
1.To access the C-TPAT Security Profile Application form on pdfFiller, visit the pdfFiller website and use the search bar to locate the form by its name.
-
2.Once you find the form, click on it to open the interactive fillable version where you can begin entering your information.
-
3.Before starting, collect all necessary documents that show your company's security measures, including details of container and trailer inspections, personnel security policies, and procedures for documentation processing.
-
4.As you navigate through the form, use the fillable fields provided on pdfFiller to input your responses. Take note of sections that require document uploads and ensure you have the necessary files ready.
-
5.Each field needs careful attention. Ensure all answers are complete and accurately reflect your security practices, following any specific instructions highlighted within the form.
-
6.After you have filled in all required fields and uploaded any necessary documents, take time to review your inputs for accuracy and completeness.
-
7.Once satisfied, you can save the form directly on pdfFiller. Choose to download it to your device, or use the platform’s submission options to send it electronically to the appropriate office.

Who is eligible to fill out the C-TPAT Security Profile Application?
Eligibility to fill out the C-TPAT Security Profile Application is primarily for foreign manufacturers that are required to demonstrate compliance with C-TPAT standards and security practices to U.S. Customs and Border Protection.
What kind of information is required for the application?
The application requires detailed information regarding your company's security measures, including but not limited to business partner requirements, container security protocols, physical access controls, and documentation procedures.
How do I submit the completed C-TPAT Security Profile Application form?
You can submit the completed C-TPAT Security Profile Application directly through pdfFiller by following the submission steps provided in the platform. Ensure all required fields are filled before submitting.
Are there any deadlines for submitting the application?
Deadlines for submitting the C-TPAT Security Profile Application may vary based on specific requests from U.S. Customs and Border Protection. It is advisable to check regularly for any updates or time-sensitive notices.
What supporting documents do I need to provide?
Supporting documents may include security process layouts, verification processes, evidence of physical access controls, and personnel security measures. Gather these documents beforehand to facilitate your application.
How long does it take to process the application?
Processing times for the C-TPAT Security Profile Application can vary. Typically, expect several weeks as U.S. Customs and Border Protection reviews the submission before issuing a certification.
What common mistakes should I avoid when filling out the application?
Common mistakes include incomplete fields, incorrect document uploads, and overlooking specific form instructions. Always double-check each section for accuracy to prevent delays in processing.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.