Last updated on Feb 17, 2026
Get the free Data Confidentiality and Security Statement with Confidentiality Statement of Unders...
Show details
A Confidentility and Security Statement and Confidentiality Statement of Understanding to be used by organization/company whose employees will be collecting and/or using data as part of a specific
We are not affiliated with any brand or entity on this form
Why choose pdfFiller for your legal forms?
All-in-one solution
pdfFiller offers a PDF editor, eSignatures, file sharing, collaboration tools, and secure storage—all in one place.
Easy to use
pdfFiller is simple, cloud-based, has a mobile app, and requires no downloads or a steep learning curve.
Secure and compliant
With encryption, user authentication, and certifications like HIPAA, SOC 2 Type II, and PCI DSS, pdfFiller keeps sensitive legal forms secure.
What is data confidentiality and security
Data confidentiality and security refers to the measures taken to protect sensitive information from unauthorized access and breaches.
pdfFiller scores top ratings on review platforms




I had a wonderful experience with PDFfiller. Try it and I know you will like it to.
New user! Very user friendly. Made things so much easie
This program is super user friendly, I am very satisfied with this product, I higgly recommend it!!!!!!
Works great on my PC and I love being able to sign and submit signatures from my tablet. Unfortunately, I'm not able to open my forms on my tablet.
it's very helpful and I enjoy the services of creating your own document, searching for documents.
FIRST TIME USER, EXCEED MY EXPECTATIONS!
Who needs data confidentiality and security?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Data Confidentiality and Security Form
How does data confidentiality and security impact research?
Data confidentiality and security significantly influence the integrity of research processes. Ensuring that sensitive information is kept confidential protects both researchers and participants, preventing misuse of data. A data confidentiality and security form is crucial for establishing trust and outlining how data will be protected, making it an essential element of any research project.
-
Data confidentiality refers to the protection of sensitive information from unauthorized access. Its importance lies in fostering trust between researchers and participants.
-
The data security form outlines the measures taken to protect data and is applicable to various research contexts, providing a clear framework.
-
Compliance with regulations such as HIPAA or GDPR is vital for protecting participant data, ensuring the research meets legal and ethical standards.
What are the key components of a data confidentiality and security policy?
A comprehensive data confidentiality and security policy should incorporate several critical elements to ensure thorough protection of research data. This helps organizations comply with ethical standards while reducing the risk of data breaches.
-
A clear statement that outlines the commitment to confidentiality is fundamental in maintaining trust among research participants.
-
An explanation of safeguarding measures details the strategies employed to protect data, including access controls and data encryption.
How can we safeguard confidential data effectively?
Identifying a confidentiality designee is essential for managing sensitive data. This designated individual is responsible for ensuring all measures for data protection are executed and understood by the team.
-
Having signed NDAs ensures that everyone involved understands the legal implications of disclosing sensitive information.
-
Clearly defining how sensitive data can be used greatly minimizes the risk of abuse.
-
Using advanced encryption techniques for computerized files prevents unauthorized access and enhances data security.
-
When sharing research results, employ strategies that maintain confidentiality, such as aggregating data and anonymizing participant details.
-
Establish clear protocols for sharing data with partners while ensuring all parties adhere to confidentiality standards.
What are the best practices for staff regarding confidentiality procedures?
Training staff on confidentiality procedures is vital to ensure compliance and protect sensitive data. General and specific procedures for different environments need to be communicated clearly.
-
Developing comprehensive procedures for staff will help identify and mitigate risks related to confidentiality during research.
-
Establish security measures in office environments that limit access to sensitive data effectively.
-
For staff that travel, precise field procedures should be implemented to ensure confidentiality remains intact regardless of the setting.
What should you do if you lose study materials with confidential data?
Loss of materials containing confidential data is a critical issue that requires immediate attention. Establishing protocols beforehand can help in managing such incidents effectively.
-
Develop protocols that specify the immediate actions to take upon discovering a loss of confidential materials.
-
Documenting the incident and the steps taken thereafter is crucial for compliance and for identifying areas of improvement.
-
Implementing measures to prevent future losses, such as regular audits and training, significantly reduces risks.
How do you create and utilize a data confidentiality and security form?
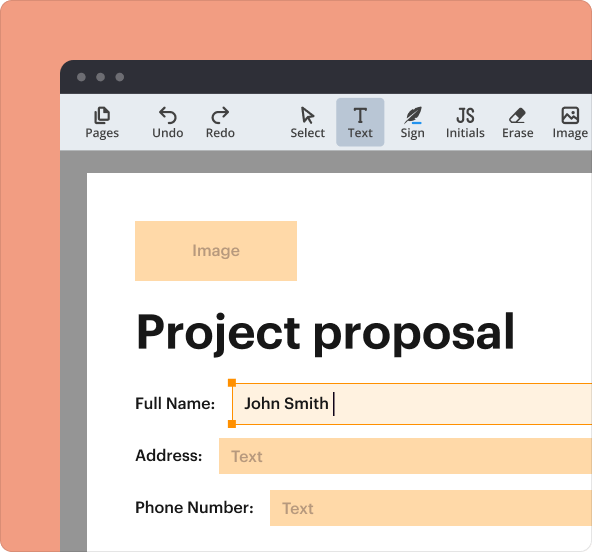
Creating a data confidentiality and security form not only formalizes the protection of sensitive information but also provides necessary guidelines for usage. With tools like pdfFiller, this process is simplified.
-
Step-by-step instructions for filling out the form ensure users understand what information is required for compliance.
-
Using pdfFiller facilitates easy editing, signing, and managing documents entirely online, enhancing user experience.
-
The platform supports a streamlined approach to document management, allowing users to focus on their projects without the hassle of paperwork.
What are the best practices and compliance considerations?
Aligning form content with institutional guidelines is essential for compliance and effectiveness. Regular evaluation of policies is just as important.
-
Ensure that the content of your data confidentiality form is tailored to meet the specific guidelines set by your institution.
-
Regularly review existing policies to confirm they remain compatible with your organization's data confidentiality and security measures.
-
When incompatibilities are found, take proactive action, such as revising the form or consulting legal advisors to maintain compliance.
How to fill out the data confidentiality and security
-
1.Open the PDF document intended for data confidentiality and security.
-
2.Examine the sections that require user input carefully.
-
3.Begin by filling out the personal information fields such as name, title, and organization.
-
4.Proceed to the data types section, specifying what kinds of data will be protected.
-
5.Fill in the security measures you currently have in place, like encryption and access controls.
-
6.Include any relevant compliance standards your organization adheres to, such as GDPR or HIPAA.
-
7.Review the document for completeness, ensuring all applicable areas are addressed.
-
8.Once satisfied, save the document and share it with relevant stakeholders for feedback if necessary.
-
9.After final approvals, ensure to securely store the finalized document and review it periodically.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.