Last updated on Oct 22, 2015

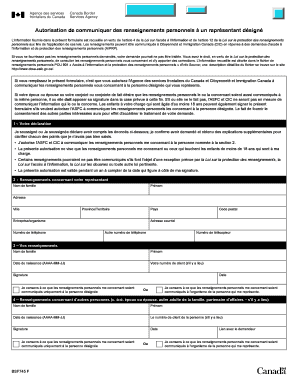
Get the free System Access Request Form
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is Access Request
The System Access Request Form is a business document used by employees to request access to systems or applications, ensuring proper approval and management of user access.
pdfFiller scores top ratings on review platforms




Who needs Access Request?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Access Request
What is the System Access Request Form?
The System Access Request Form serves a crucial purpose in IT environments by facilitating requests for user access or updates to existing access for various IT systems. This form is traditionally filled out by employees who seek new access or by managers who need to modify or revoke access rights for their team members. Its significance lies in its role as a formal request mechanism, which helps maintain organized access management within an organization.
Purpose and Benefits of the System Access Request Form
The primary purpose of the System Access Request Form is to uphold security and order within IT systems. By utilizing this form, organizations can streamline their access management process, ensuring that each request is documented clearly and comprehensively. One of the key benefits includes the confirmation of accountability, as it requires necessary signatures to endorse the legitimacy of the request. Clear documentation aids in audits and compliance checks, making it an essential tool in any organization’s access control framework.
Who Needs the System Access Request Form?
This form is relevant for various stakeholders involved in the access request process. Key roles include users requesting access, authorizing managers who approve those requests, and ICT administrators tasked with implementing access changes. Specific situations that require filling out the form include onboarding new employees or when existing staff members undergo role changes that necessitate different access levels.
Information You'll Need to Gather
To complete the System Access Request Form accurately, it is important to gather the necessary information beforehand. This checklist includes the following details:
-
Personal details of the requester
-
Job title and department
-
Contact information
-
Specific access needs
How to Fill Out the System Access Request Form Online (Step-by-Step)
Filling out the System Access Request Form online is a straightforward process. Follow these steps to ensure proper completion:
-
Navigate to the form link provided by your organization.
-
Enter the required personal details and access needs in the respective fields.
-
Review the information for accuracy.
-
Save any changes you've made.
Common Errors and How to Avoid Them
When completing the System Access Request Form, users often make common errors that can delay the approval process. To avoid these pitfalls, consider the following tips:
-
Double-check that all required fields are filled out completely.
-
Ensure your provided information is accurate and up-to-date.
-
Verify that all necessary signatures are obtained before submission.
How to Sign the System Access Request Form
Signing the System Access Request Form is a critical step in the process. Depending on your organization's policies, you may need to use digital signatures or, in some cases, wet signatures. It is essential to confirm that the signature verification process is followed for security and compliance purposes, ensuring that modifications in access are authorized and legitimate.
Submission Methods and Delivery
After completing the System Access Request Form, users have several submission options available. These methods typically include submitting via email or through an online portal set up by the organization. After submission, users should expect a confirmation to ensure their request has been received and is being processed.
Security and Compliance for the System Access Request Form
Handling sensitive access data requires strict security measures. The System Access Request Form adheres to robust security protocols, including pdfFiller's 256-bit encryption, ensuring compliance with industry standards. Protecting user information throughout the access request process is paramount, as it maintains the integrity of the organization’s IT security framework.
Simplify Your Access Requests with pdfFiller
pdfFiller facilitates the filling, signing, and management of the System Access Request Form, allowing users to streamline their document handling processes. By utilizing pdfFiller’s cloud-based tools, users can create, edit, and securely share their forms with ease. This solution not only simplifies document management but also enhances overall efficiency in handling access requests.
How to fill out the Access Request
-
1.To access the System Access Request Form on pdfFiller, visit the site and log in to your account or create one if necessary.
-
2.Once logged in, use the search bar to locate the 'System Access Request Form' and click to open it.
-
3.Review the form’s instructions carefully to understand what information is required for completion before you start filling it out.
-
4.Begin by entering the user’s personal details in the designated fields. This includes name, job title, department, and contact information.
-
5.Next, specify the system or application access needed, along with the specific functions the user requires access to. Use checkboxes where appropriate.
-
6.Ensure every required field is completed accurately to avoid delays in processing. Double-check for any missing information as you go.
-
7.As you complete the form, gather any necessary documents or details that support the access request by coordinating with the user or their supervisor.
-
8.Before finalizing the form, review all entered information for accuracy and completeness, making adjustments as necessary.
-
9.After reviewing, you may sign the form electronically. Include the signatures of both the user and the authorizing manager before submitting.
-
10.Once all signatures are obtained, save the completed form by clicking the save button in pdfFiller. You have the option to download it to your device or submit it directly through the platform.

Who is eligible to fill out the System Access Request Form?
The form can be filled out by any employee seeking access to a system or application. Typically, this includes new hires, existing users requiring additional access, or those requesting to modify their current access.
What is the submission process for the System Access Request Form?
Once the form is completed and signed, it can be submitted electronically via pdfFiller or printed and submitted to the appropriate ICT department. Ensure all signatures are present before submitting.
What supporting documents are needed for the access request?
In most cases, supporting documents include an employee's identification and a supervisor's approval. Consult with your manager to determine any additional documentation required.
What are common mistakes to avoid when filling out this form?
Common mistakes include leaving required fields blank, entering incorrect user information, and forgetting to obtain necessary signatures from managers or IT administrators.
How long does it take to process access requests?
Processing times can vary based on the complexity of the request and departmental workflows. Generally, requests are processed within several business days, but it’s advisable to allow extra time during peak periods.
Can I make changes to the form after submission?
Once the System Access Request Form is submitted, changes can usually only be made by resubmitting a revised form. Contact your ICT department for guidance on making corrections.
Is notarization required for the System Access Request Form?
No, notarization is not required for the System Access Request Form as per the current guidelines provided in the form metadata.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.