Last updated on Mar 30, 2026
Get the free Key Management Standard Template
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.
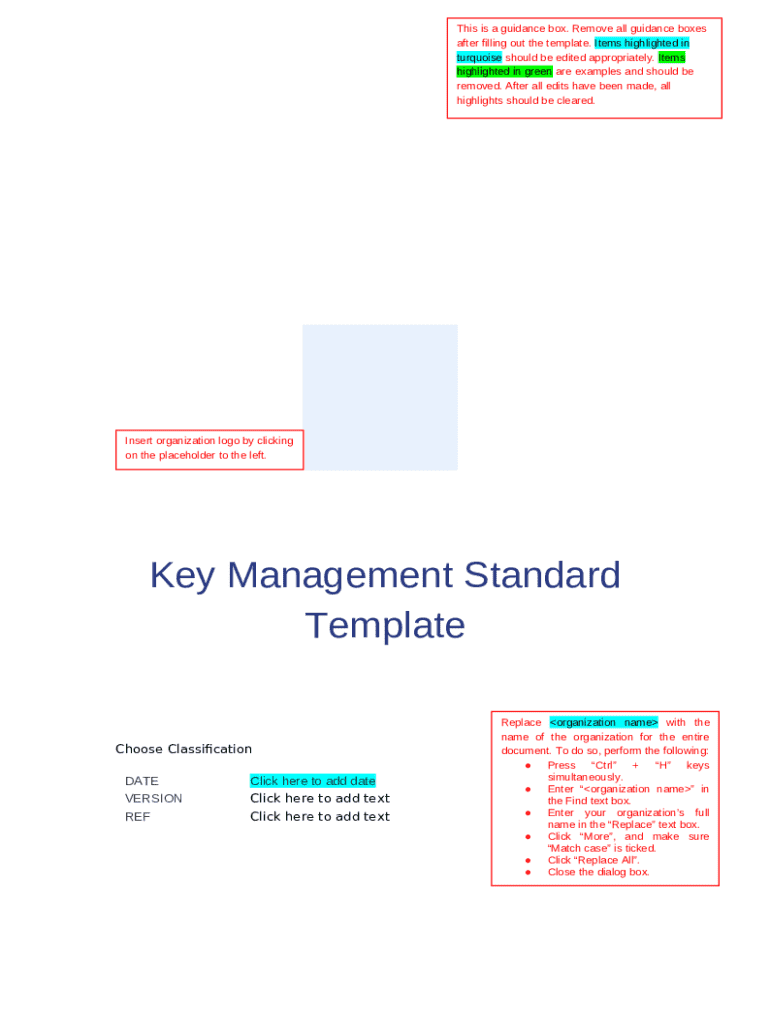
What is key management standard template
The Key Management Standard Template is a business document used by organizations to outline cybersecurity requirements related to key management processes.
pdfFiller scores top ratings on review platforms




Who needs key management standard template?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to key management standard template
What is the Key Management Standard Template?
The Key Management Standard Template serves a critical role in enhancing cybersecurity measures within organizations. It outlines essential key management requirements that facilitate the secure handling of sensitive information.
This document is significant as it establishes a clear framework for cybersecurity key management, ensuring organizations can effectively manage and protect cryptographic keys. Customization is crucial, as organizations must tailor the template to meet their specific operational needs and compliance standards.
Purpose and Benefits of the Key Management Standard Template
The primary purpose of using the Key Management Standard Template is to streamline the key management processes within an organization. By implementing this template, organizations can clearly define key management protocols, which significantly benefits overall security and compliance efforts.
-
Establishes clear key management processes and protocols.
-
Enhances compliance with regulatory requirements.
-
Improves security by detailing key responsibilities.
Key Features of the Key Management Standard Template
This template offers various features designed to make key management efficient and organized. The essential components ensure that all necessary information is captured and managed appropriately.
-
Sections for document approval, version control, and a table of contents.
-
Fillable fields for organization name, date, and individual's name.
-
Instructions for specific customization aligned with organizational needs.
Who Needs the Key Management Standard Template?
The Key Management Standard Template is essential for a diverse range of users within an organization. Identifying the right audiences ensures effective utilization of the template in promoting cybersecurity efforts.
-
Organizations looking to enhance their key management protocols.
-
Cybersecurity professionals tasked with compliance and security initiatives.
-
Companies needing a formalized procedure for managing cryptographic keys.
How to Fill Out the Key Management Standard Template Online
Filling out the Key Management Standard Template online involves specific steps to ensure comprehensive completion. Following these guidelines will facilitate the process and minimize errors.
-
Access the template through the designated online platform.
-
Edit each fillable field as needed, providing necessary information.
-
Follow the customization instructions meticulously to ensure alignment with organizational needs.
Review and Validation Checklist for the Key Management Standard Template
Conducting a thorough review of the Key Management Standard Template is vital to ensure its correctness and completeness. Implementation of a validation checklist can help identify any discrepancies or errors before submission.
-
Verify that all essential elements are included and accurate.
-
Avoid common pitfalls by reviewing frequently overlooked areas.
-
Adopt best practices for a comprehensive review before finalization.
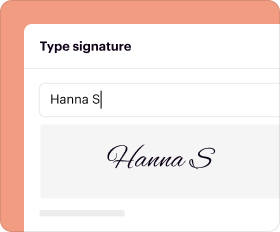
How to Sign the Key Management Standard Template
Understanding the signature requirements for the Key Management Standard Template is crucial for compliance and legal acknowledgment. The signing process can vary based on organizational policies.
-
Digital signatures are preferred for convenience, while wet signatures may be required in specific situations.
-
Follow signature requirements established by the organization.
-
Utilize pdfFiller for seamless eSigning of the template.
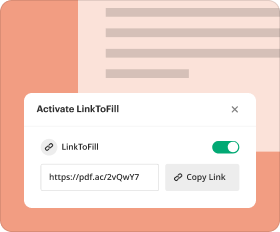
Where to Submit the Key Management Standard Template
Once completed, knowing the right submission channels for the Key Management Standard Template ensures its acceptance and processing. Different methods may be appropriate depending on the organization's compliance needs.
-
Common submission methods include online platforms and traditional mail.
-
Understand the submission channels related to cybersecurity compliance.
-
Be aware of any deadlines or anticipated processing timeframes.
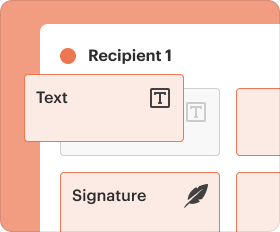
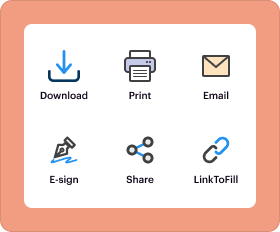
Using pdfFiller to Complete Your Key Management Standard Template
pdfFiller provides robust support for completing the Key Management Standard Template efficiently. Its features enhance document handling and improve overall user experience.
-
Utilize pdfFiller's editing and form-filling capabilities for streamlined management.
-
Take advantage of security features that ensure data safety and compliance.
-
Leverage pdfFiller for a practical and user-friendly template completion experience.
How to fill out the key management standard template
-
1.Access pdfFiller and log in or create an account if you don't have one.
-
2.Locate the Key Management Standard Template by entering its name in the search bar or browsing through the Business Forms category.
-
3.Open the document and familiarize yourself with its structure, noting the fillable fields such as 'Insert organization name' and 'Click here to add date'.
-
4.Before filling in the fields, gather necessary information, including your organization’s name, relevant dates, and names of individuals who need to approve the document.
-
5.Begin completing the form by clicking on each fillable field and entering the required information. Follow the provided instructions carefully to ensure accuracy.
-
6.Make sure to replace placeholders, such as <organization name>, with the specific details pertaining to your organization throughout the document.
-
7.Review each section for completeness and verify that all required signatures and approvals are present before finalizing the form.
-
8.Once you have completed all fields and double-checked for accuracy, save your progress.
-
9.To finalize your submission, download the filled form or submit it directly through pdfFiller, ensuring it meets your organization’s procedures.
Who needs to sign the Key Management Standard Template?
The Key Management Standard Template must be signed by the head of the organization or their delegate to validate the document and ensure its implementation.
Can I edit the Key Management Standard Template?
Yes, the Key Management Standard Template is designed to be customized. You can edit it to align with your organization's specific needs and legislative requirements.
What categories of professionals use this template?
This template is primarily used by cybersecurity managers, compliance officers, IT professionals, and senior executives within organizations managing key oversight.
What should be done before starting to fill out the template?
Before filling out the template, gather essential organizational information, including the organization’s name and any relevant dates or approvals that will be needed.
How do I ensure the document is completed correctly?
To ensure accuracy, thoroughly review each section, confirm all placeholders are appropriately filled, and verify that required signatures are included before finalizing the document.
Is notarization required for this form?
No, the Key Management Standard Template does not require notarization, but it must still be signed by the appropriate authority within the organization.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.