Last updated on Mar 29, 2026
Get the free Cloud Computing Cybersecurity Policy Template
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.
What is cloud computing cybersecurity policy
The Cloud Computing Cybersecurity Policy Template is a policy document used by organizations to establish cybersecurity requirements for cloud computing services.
pdfFiller scores top ratings on review platforms




Who needs cloud computing cybersecurity policy?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to cloud computing cybersecurity policy
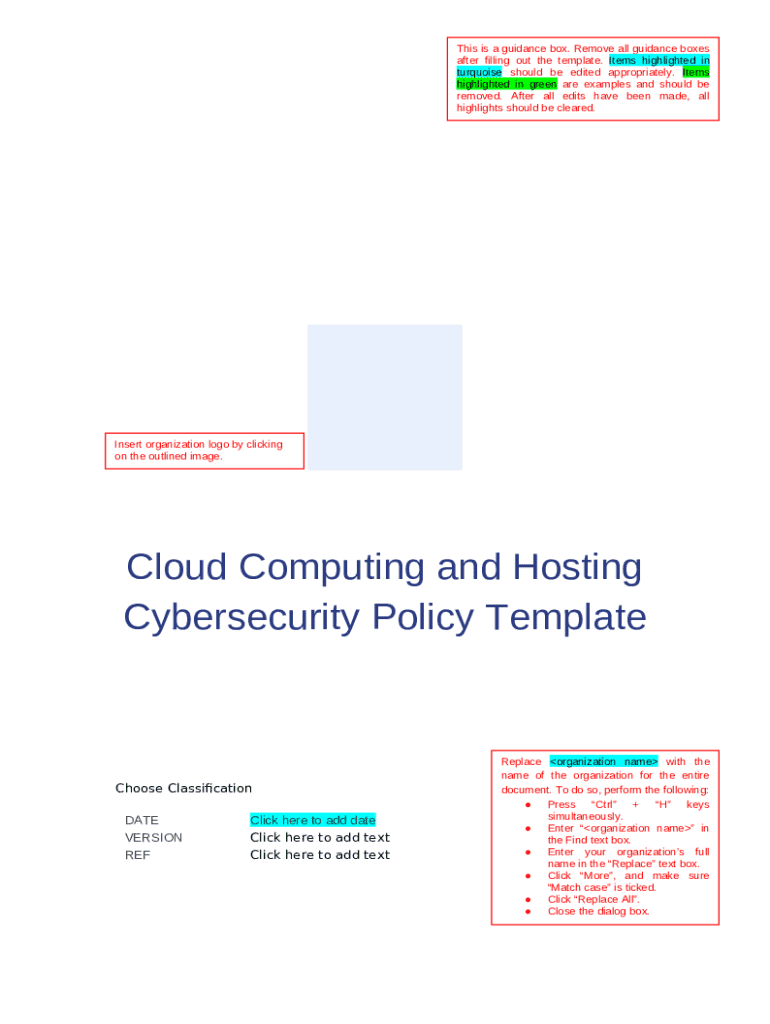
What is the Cloud Computing Cybersecurity Policy Template?
The Cloud Computing Cybersecurity Policy Template is a vital document designed for organizations to establish clear cybersecurity protocols that govern the use of cloud services. This template defines the specific cybersecurity requirements necessary for protecting organizational information and technology assets within cloud environments. By utilizing this template, organizations can align their cybersecurity efforts with established best practices and compliance requirements.
Customizing the template to fit specific organizational needs is crucial for its effectiveness. Tailoring the contents ensures that the policy reflects the unique security requirements and operational processes of the organization, thus enhancing its relevance and applicability.
Purpose and Benefits of the Cloud Computing Cybersecurity Policy Template
Organizations require a cybersecurity policy template to ensure the security of their cloud computing resources. A well-defined policy serves as a foundation for establishing consistent security practices that protect sensitive data across cloud platforms. Implementing such a policy not only facilitates improved compliance with industry regulations but also enhances overall security posture.
-
Promotes clarity of roles and responsibilities among staff.
-
Addresses the essential need for effective risk management.
-
Supports the organization in adhering to regulatory standards.
Key Features of the Cloud Computing Cybersecurity Policy Template
The Cloud Computing Cybersecurity Policy Template includes several crucial sections, such as purpose, policy statements, and compliance requirements. Each section is thoughtfully designed to provide comprehensive guidance on policy content, ensuring that users have all necessary information at their fingertips.
-
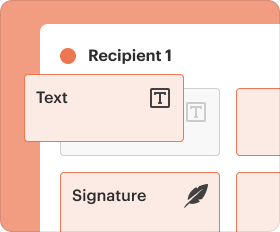
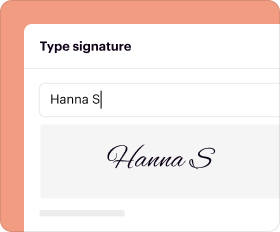
Customizable fields allowing for the integration of company-specific details, including logos and signatures.
-
Instructions for completion that guide users through each section effectively.
-
Checkboxes that simplify the selection of applicable policies and practices.
Who Needs the Cloud Computing Cybersecurity Policy Template?
Various roles within an organization benefit from utilizing the Cloud Computing Cybersecurity Policy Template. Key stakeholders, such as the Authorizing Official and Head of Organization, must review and sign off on the completed policy document to ensure proper oversight.
IT departments, compliance officers, and management personnel also play critical roles in shaping and executing cybersecurity strategies. This template is particularly relevant for a wide array of industries that utilize cloud services, ensuring that all necessary stakeholders understand and uphold security protocols.
How to Fill Out the Cloud Computing Cybersecurity Policy Template Online
Filling out the Cloud Computing Cybersecurity Policy Template online requires careful preparation. Begin by gathering all necessary information, including organizational details, security requirements, and team roles.
-
Collect required information about your organization's cloud services.
-
Follow the instructions provided in the template for each section.
-
Pay attention to any specific fields that require detailed responses.
-
Avoid common errors such as omitting signatures or failing to customize key sections.
Signing and Submitting the Cloud Computing Cybersecurity Policy Template
Properly signing and submitting the completed template is crucial for validation. Organizations must distinguish between digital signatures and wet signatures, choosing the appropriate method based on their internal policies.
Submission methods can vary, including digital uploads or sending physical copies. Additionally, it is important to adhere to deadlines and attach any necessary accompanying documents to ensure that the process is seamless.
Security and Compliance for the Cloud Computing Cybersecurity Policy Template
Maintaining security while filling out and managing the Cloud Computing Cybersecurity Policy Template is paramount. Organizations must be aware of data protection policies and comply with regulations such as HIPAA and GDPR.
Utilizing platforms like pdfFiller ensures that user documents are handled securely, employing 256-bit encryption and compliance with necessary security standards. It is also essential to understand record retention requirements and prepare for potential compliance audits.
Sample or Example of a Completed Cloud Computing Cybersecurity Policy Template
Providing users with an example of a completed Cloud Computing Cybersecurity Policy Template can enhance understanding. This visual aid illustrates the effective application of the template's components and demonstrates how to tailor policies to meet organizational needs.
Additionally, industry-specific examples may be available to further inform users on customization strategies and best practices.
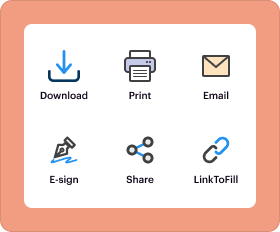
Explore pdfFiller to Customize and Download Your Template
pdfFiller offers users an excellent platform for customizing and managing their Cloud Computing Cybersecurity Policy Template. With its intuitive interface, users can easily modify templates, ensuring that their documents are both functional and secure.
With over 100 million users, pdfFiller is a trusted resource for creating, editing, and signing documents online. Organizations can rely on pdfFiller's commitment to compliance and security for all document handling needs.
How to fill out the cloud computing cybersecurity policy
-
1.Begin by accessing the pdfFiller website and sign in to your account or create a new account if you do not have one.
-
2.Use the search function to locate the Cloud Computing Cybersecurity Policy Template by entering the template name in the search bar.
-
3.Open the template and familiarize yourself with its layout, including sections for purpose, scope, roles, and compliance.
-
4.Before filling out the form, gather required information such as your organization's name, logo, and specific cybersecurity policies that need to be included.
-
5.Start filling in the fields by clicking on each blank space and entering the relevant information, ensuring you personalize it for your organization.
-
6.Use the checkboxes where applicable according to your organization's requirements, and add comments or notes if necessary.
-
7.Be mindful to verify that all placeholders are replaced with your organization's specific details, including the name and date.
-
8.Once you have completed all sections of the template, review the document to check for any errors or missing information.
-
9.After finalizing the content, save your progress. You can choose to download the document in PDF format or keep it stored on pdfFiller.
-
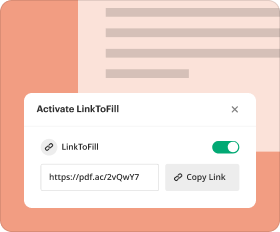
10.If needed, submit the document directly through pdfFiller or share it with other stakeholders for their signatures before final approval.
Who is eligible to use the Cloud Computing Cybersecurity Policy Template?
The Cloud Computing Cybersecurity Policy Template is designed for organizations of all sizes that utilize cloud computing services. It is particularly useful for IT leaders, compliance officers, and business owners.
What information do I need before filling out this template?
Before you start filling out the template, gather your organization's name, logo, cybersecurity policies, and any specific practices related to cloud computing. This ensures accuracy and relevance.
Are there any submission deadlines for this policy template?
While the template does not have inherent deadlines, it is advisable to complete and formalize your organization's cybersecurity policy as soon as possible, particularly in response to regulatory requirements or audits.
Can I submit the completed document online?
Yes, you can submit the completed Cloud Computing Cybersecurity Policy Template online through pdfFiller. This allows for easy sharing with stakeholders for their approval.
What common mistakes should I avoid while completing this template?
Common mistakes include failing to replace placeholders, overlooking required sections, and not obtaining necessary signatures. Always double-check for completeness before finalizing the document.
What is the processing time for reviewing this type of policy document?
Processing times may vary based on your organization's internal review procedures. However, once submitted, expect a few days for proper review and feedback from stakeholders.
Is notarization required for this policy document?
No, notarization is not required for the Cloud Computing Cybersecurity Policy Template. It can be approved by authorized officials within your organization without the need for notarization.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.