Last updated on Feb 27, 2026
Get the free network security scorecard
Show details
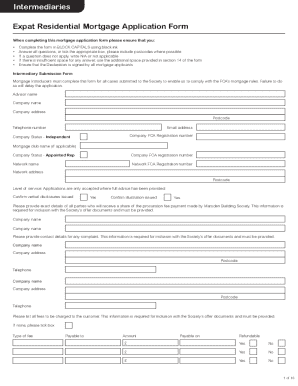
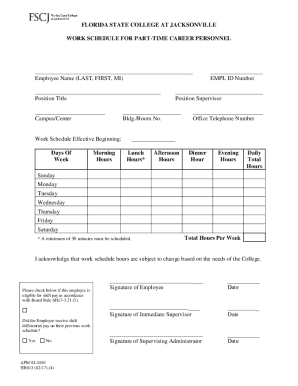
The Network Security SCORECARD Name: ___ Title: ___ Company: ___ ___ Email: ___ Phone: ___ ___Indicate the degree to which you agree or disagree with the statement below. Once you are finished, total
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.
What is network security scorecard
The Network Security Scorecard is a form used by organizations to evaluate their network security protocols and strategies.
pdfFiller scores top ratings on review platforms




Who needs network security scorecard?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to network security scorecard
What is the Network Security Scorecard?
The Network Security Scorecard is a critical tool that helps organizations evaluate their network security protocols. By providing a structured assessment framework, it emphasizes the importance of robust cybersecurity strategies. This scorecard enables organizations to manage risks effectively and evaluate their network security stance systematically.
Utilizing a cybersecurity assessment form, companies can gain insights into their current security measures and identify areas that require attention. A comprehensive approach to assessing these protocols is essential for maintaining data integrity and compliance.
Purpose and Benefits of the Network Security Scorecard
The Network Security Scorecard serves multiple functions that are valuable for organizations looking to enhance their security framework. First, it helps identify specific areas where security measures can be improved, ensuring that organizations are proactive in their risk management efforts.
Additionally, the scorecard supports the alignment of business objectives with security strategies, promoting a cohesive approach to cybersecurity. This alignment is crucial for meeting regulatory requirements and avoiding potential penalties, making the scorecard a vital tool for compliance.
Key Features of the Network Security Scorecard
The Network Security Scorecard offers several key features designed to enhance usability and effectiveness. Users will find fillable fields that allow for scoring on a scale from one to ten, addressing various aspects of network security.
-
Covers diverse security areas, including cloud utilization, vulnerability assessments, and identity management.
-
Clear instructions guide users on how to complete the form accurately.
Who Should Use the Network Security Scorecard?
This scorecard is applicable to a wide range of users. Organizations of all sizes can benefit from its structured assessment to gauge their network security. Specifically, IT professionals and security teams tasked with managing cybersecurity will find the scorecard invaluable in evaluating existing measures.
External auditors and consultants conducting security evaluations will also see this tool as an essential part of their assessment processes, facilitating a thorough analysis of network security protocols.
How to Fill Out the Network Security Scorecard Online
Filling out the Network Security Scorecard online is straightforward. First, familiarize yourself with each section of the scorecard. Each area is designed to address different aspects of network security, making it easier to provide relevant scores.
-
Review the instructions provided for scoring and interpreting prompts.
-
Score each section based on your organization's practices and protocols.
-
Ensure accuracy and completeness by cross-referencing against existing documentation.
Common Errors and How to Avoid Them in the Network Security Scorecard
When using the Network Security Scorecard, users often fall into common traps that can skew results. One significant error is misunderstanding the scoring criteria, which can lead to inaccurate or inconsistent responses.
Maintaining consistency in responses across sections is crucial for accurate evaluations. Additionally, validation tips include double-checking that all fields are filled correctly, which ensures a comprehensive assessment of network security.
Security and Compliance Considerations When Using the Network Security Scorecard
Organizations must ensure they adhere to stringent security measures when handling sensitive information in the scorecard. Using secure platforms, such as pdfFiller, significantly mitigates risk during the evaluation process.
Compliance with relevant standards is essential when conducting cybersecurity assessments. Organizations should prioritize secure document management and storage to maintain data integrity and confidentiality.
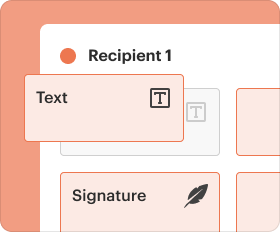
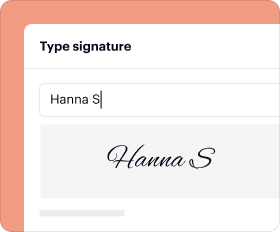
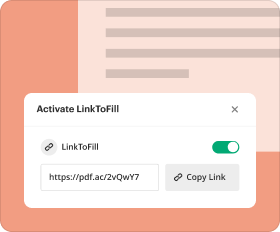
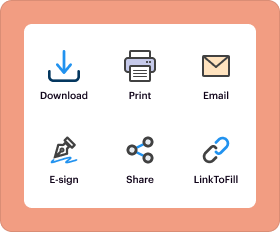
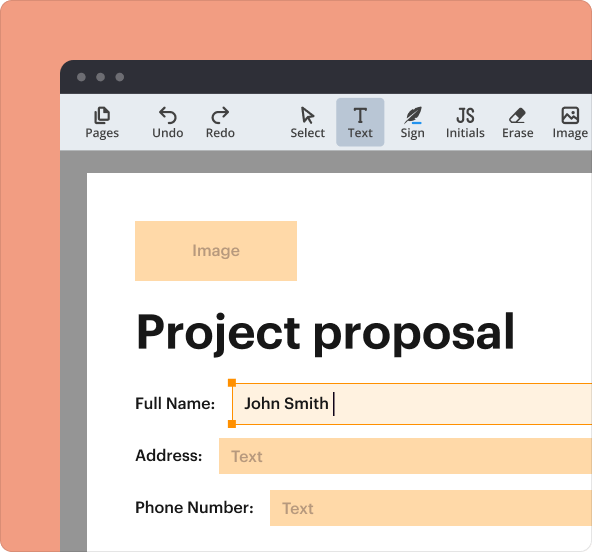
How to Use pdfFiller for the Network Security Scorecard
pdfFiller enhances the process of completing the Network Security Scorecard with its robust features. Users can easily fill, edit, and securely manage their forms via a cloud-based platform, ensuring accessibility and convenience.
-
Utilize eSigning options for secure approvals.
-
Take advantage of document sharing capabilities for collaboration within teams.
Maximizing Your Network Security Evaluation: Strategies and Recommendations
To maximize the benefits of the Network Security Scorecard, organizations should adopt best practices based on their assessment results. Identifying and prioritizing areas for security improvements is key to enhancing overall network safety.
Additionally, ongoing security training and evaluations should be emphasized to adapt to evolving threats. This proactive approach will reinforce the organization's commitment to maintaining a secure environment.
Get Started with Your Network Security Scorecard Today!
Accessing and using the Network Security Scorecard on pdfFiller is an easy process. Organizations can benefit from a seamless experience while ensuring data security throughout completion. Join millions of users who trust pdfFiller for their form-filling needs.
How to fill out the network security scorecard
-
1.To begin, access pdfFiller and search for the Network Security Scorecard form in the template library.
-
2.Once located, open the form by clicking on it to load it into the editor.
-
3.Before filling out the form, gather all necessary information regarding your current network security measures, policies, and risk management strategies.
-
4.Navigate through the form fields using your mouse or keyboard. Click on each fillable field to enter your ratings based on the prescribed scale.
-
5.Make sure to review the instructions within the form for specific guidance on how to score each aspect of your network security.
-
6.After completing all sections, take a moment to review your entries for accuracy and completeness.
-
7.To finalize the form, check for any highlighted errors or warnings that may need attention.
-
8.Once satisfied with your form, choose to save it, download it as a PDF, or submit it directly through pdfFiller, depending on your requirements and preferences.
Who should complete the Network Security Scorecard?
The Network Security Scorecard should be completed by individuals in roles related to information technology, risk management, compliance, or cybersecurity, including CTOs, CIOs, and IT managers.
Are there any deadlines for submitting the form?
The Network Security Scorecard does not have universal deadlines, but organizations should aim to complete it regularly to ensure up-to-date risk assessments and security evaluations.
How can I submit the completed Network Security Scorecard?
Once you fill in the Network Security Scorecard on pdfFiller, you can submit it electronically through the platform or choose to download it for manual submission as needed.
What supporting documents are required with the form?
Generally, no supporting documents are required with the Network Security Scorecard, but having detailed previous assessments or security policies can be beneficial for accurate evaluations.
What are common mistakes to avoid while filling out the form?
Common mistakes include misinterpreting rating scales or failing to review entries for accuracy, which can lead to incorrect assessments and poor security strategy evaluations.
How long does it take to process the Network Security Scorecard?
The processing time for the Network Security Scorecard is immediate if submitted through pdfFiller, as evaluations largely depend on internal organizational reviews post-submission.
Can the form be edited after submission?
Once the Network Security Scorecard is submitted, you may need to create a new version for additional changes. Keep the original for your records and re-evaluate as necessary.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.