Last updated on Mar 12, 2026
Get the free cyber risk assessment form
Show details
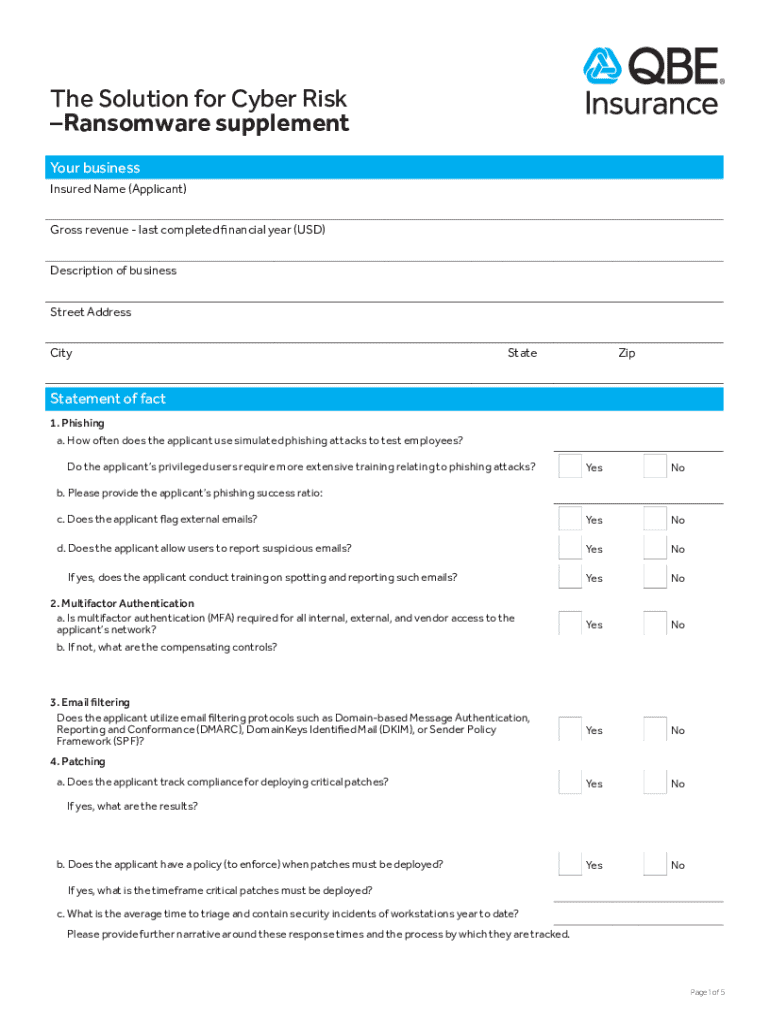
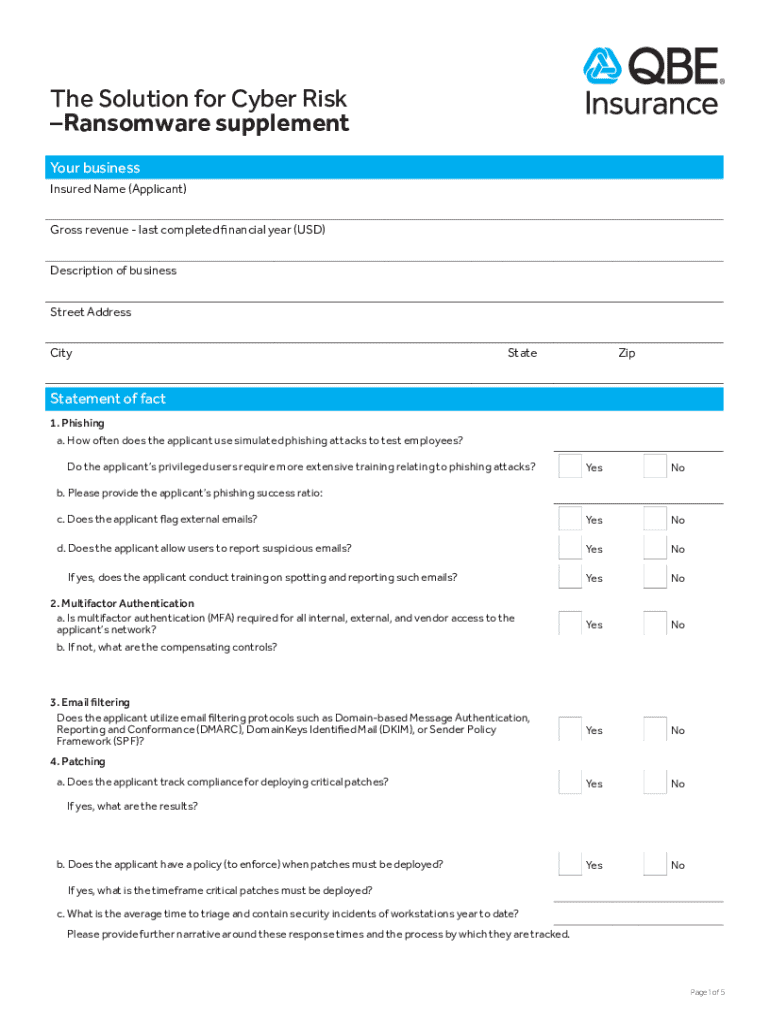
The Solution for Cyber Risk Ransomware supplement Your business Insured Name (Applicant) Gross revenuelast completed financial year (USD) Description of business Street Address CityStateZipStatement
We are not affiliated with any brand or entity on this form
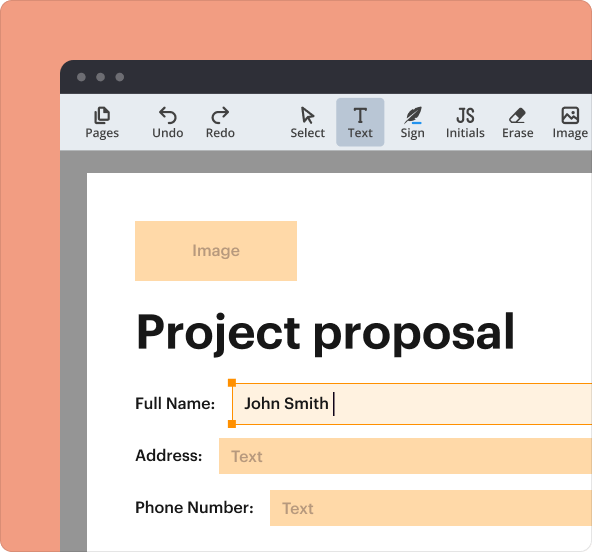
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.
What is cyber risk assessment form
The Cyber Risk Assessment Form is a business document used by organizations to evaluate and enhance their cybersecurity measures.
pdfFiller scores top ratings on review platforms




Who needs cyber risk assessment form?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to cyber risk assessment form
Understanding the Cyber Risk Assessment Form: What Is It?
The Cyber Risk Assessment Form serves a critical role in business operations by providing a structured approach to evaluating cybersecurity practices. It encompasses various sections that cover essential elements such as phishing, multifactor authentication, and encryption. By utilizing this business cybersecurity form, companies can systematically assess their vulnerabilities and identify areas where improvements are needed.
The form includes key sections that require businesses to provide information on their current security protocols. This includes an appraisal of phishing risks, the implementation of multifactor authentication, and the adequacy of encryption measures in place to protect sensitive data.
Why Businesses Need a Cyber Risk Assessment Form
Evaluating cybersecurity measures is paramount for businesses aiming to protect sensitive information from breaches. The cyber risk assessment form enables companies to systematically review their cybersecurity protocols, thereby enhancing their defense against potential cyber threats. Completing this assessment is not merely a formality; it offers significant benefits in risk management and compliance.
Organizations can benefit from identifying vulnerabilities, potentially lowering insurance premiums and ensuring adherence to regulatory requirements by conducting this cyber risk evaluation. This proactive measure reinforces the business's commitment to safeguarding client information and maintaining operational integrity.
Key Features of the Cyber Risk Assessment Form
The Cyber Risk Assessment Form is designed with multiple features to facilitate ease of use and thoroughness. Key features include:
-
Fillable fields that allow for easy input of necessary data.
-
Checkboxes to simplify responses to yes/no questions.
-
Detailed instructions guiding the completion of each section.
Additionally, it is essential for the form to be validated by an authorized representative’s signature, which substantiates the accuracy of the information provided.
Who Should Complete the Cyber Risk Assessment Form?
The appropriate audience for this form includes business owners and authorized representatives from various states in the U.S. This group is responsible for ensuring that the cybersecurity measures comply with industry standards and regulatory frameworks. It is crucial to understand the eligibility requirements that dictate who should be involved in this assessment process.
Business stakeholders can ensure that all necessary perspectives are considered, leading to a comprehensive risk evaluation. By engaging authorized representatives, companies can promote accountability and thoroughness in completing the assessment.
Filling Out the Cyber Risk Assessment Form: Step-by-Step Guide
Completing the Cyber Risk Assessment Form requires careful attention to each section. The process can be simplified with a step-by-step guide that outlines what information is needed:
-
Begin with the basic details, including the name of the insured and the gross revenue for the last completed financial year.
-
Proceed to evaluate cybersecurity measures by answering specific questions related to phishing threats and multifactor authentication.
-
Provide detailed information regarding encryption practices and other relevant security protocols.
-
Review all provided information, ensuring the accuracy of responses, before moving to the final step.
-
Sign the document using an authorized representative’s signature to validate the submission.
Common Mistakes to Avoid When Submitting the Cyber Risk Assessment Form
When completing the Cyber Risk Assessment Form, several common errors frequently arise. To facilitate a successful submission, be mindful of the following mistakes:
-
Leaving sections incomplete or filled out ambiguously can lead to invalid assessments.
-
Failing to sign the form properly can result in rejection.
To minimize errors, having a review checklist can be invaluable. Verifying each entry before submission ensures that all necessary fields are completed and accurate.
How to Sign the Cyber Risk Assessment Form
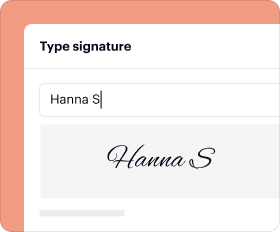
Understanding the requirements for signing the Cyber Risk Assessment Form is essential for validation. There are two primary options for signature:
-
A digital signature, which can be completed using platforms such as pdfFiller.
-
A wet signature, where a handwritten signature is required on a printed copy of the form.
The electronic signing process on pdfFiller streamlines this step, allowing users to sign documents securely and efficiently.
Submission Guidelines for the Cyber Risk Assessment Form
Businesses have various options for submitting the Cyber Risk Assessment Form. Submission methods include both online and offline channels. It’s also crucial to be aware of any applicable fees or submission deadlines associated with these methods.
Tracking the submission process can provide reassurance, confirming that the form is received for processing. Companies should always ensure they are aware of the timeline for a response or confirmation from the decision-making authority.
Post-Submission: What Comes Next?
After submitting the Cyber Risk Assessment Form, businesses should be prepared for potential follow-up actions. If there is a need to amend the form, understanding how to proceed is vital:
-
Make necessary corrections as soon as possible to avoid unnecessary delays.
-
Be familiar with common rejection reasons, such as incomplete information or lack of a signature.
Addressing these issues promptly will streamline the process and help in resubmission when necessary.
Why Use pdfFiller for Your Cyber Risk Assessment Form
Utilizing pdfFiller for managing the Cyber Risk Assessment Form provides significant advantages. This platform allows users to efficiently fill out, sign, and manage their forms with ease. Most importantly, pdfFiller ensures the security of sensitive information with robust security protocols, including 256-bit encryption and compliance with HIPAA and GDPR.
The features offered by pdfFiller enhance user experience, making the process of creating and managing business forms streamlined and secure.
How to fill out the cyber risk assessment form
-
1.Access pdfFiller and log in to your account.
-
2.Locate the Cyber Risk Assessment Form by searching in the template library or using the search bar.
-
3.Open the form by clicking on it to bring up the editing interface.
-
4.Begin by filling out the 'Insured Name (Applicant)' field. Ensure that the provided name matches the legal entity.
-
5.Gather financial information such as gross revenue from the last completed financial year in USD. This will help in accurately filling out the form.
-
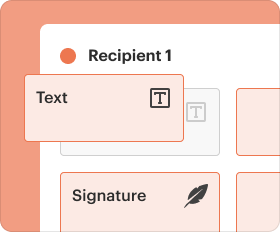
6.Navigate through the various sections of the form including phishing, multifactor authentication, email filtering, and more, by scrolling down through the fields.
-
7.Utilize pdfFiller’s fillable fields and checkboxes to indicate compliance or non-compliance on each section. Take your time to read each prompt carefully.
-
8.Double check all filled information for accuracy and completeness. Ensure that any necessary documentation is attached as supporting evidence where required.
-
9.Once all fields are completed, review the entire form. Pay attention to any notification bars indicating missing information.
-
10.After final review, save your progress using the 'Save' button to avoid losing any data.
-
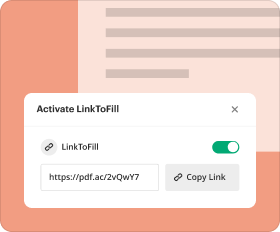
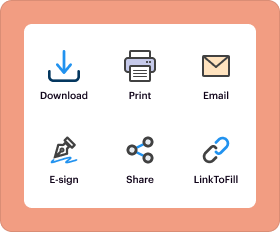
11.Lastly, download the completed form as a pdf or submit it directly through pdfFiller's submission options if applicable.
Who is eligible to fill out the Cyber Risk Assessment Form?
The form is intended for organizations and businesses looking to assess their cybersecurity measures. Authorized representatives such as owners, partners, or IT managers should complete it.
Are there any deadlines for submitting the Cyber Risk Assessment Form?
While the form itself may not have a strict deadline, it is advisable to complete it as part of your regular risk assessment cycle, especially before audits or compliance checks.
What methods can I use to submit the form?
You can submit the form through pdfFiller by directly emailing it to the required parties or downloading and sending it manually as a pdf file.
Is there any supporting documentation required with this form?
Typically, supporting documentation may include previous assessments, cybersecurity policies, or financial statements. It's best to consult relevant guidelines for specifics.
What common mistakes should I avoid when filling out the form?
Ensure all fields are completed and double-check for accuracy. Common errors include missing signatures, incorrect financial data, or skipped checkboxes.
How long does it take to process the Cyber Risk Assessment Form?
Processing time can vary depending on internal reviews. Generally, allow at least 1-2 weeks for comprehensive assessments to be reviewed and finalized.
What concerns should I be aware of when completing this form?
Be cautious of providing inaccurate data, as this may affect your cybersecurity evaluation. Ensure all answers are truthful and reflective of your current practices.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.