Last updated on Apr 11, 2026
Get the free Connector Cyber Liability Application
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.
What is connector cyber liability application
The connector cyber liability application is a document used by businesses to apply for cyber liability insurance coverage, protecting against data breaches and cyber threats.
pdfFiller scores top ratings on review platforms




Who needs connector cyber liability application?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to connector cyber liability application
What is the Connector Cyber Liability Application
The Connector Cyber Liability Application is a vital tool for businesses seeking protection against cyber threats. This application serves as a means to obtain cybersecurity insurance, which provides businesses with essential support in case of data breaches or cyber incidents. Understanding the importance of this application can help organizations mitigate risks and reinforce their commitment to data security.
Cybersecurity insurance offers several benefits, including financial recovery options and risk management strategies tailored to various industries. The Connector Cyber Liability Application addresses potential coverage areas such as data protection, customer information security, and loss of income due to cyber events.
Purpose and Benefits of the Connector Cyber Liability Application
Completing the Connector Cyber Liability Application is essential for businesses aiming to safeguard their operations from cyber threats. This application not only provides crucial protection but also offers financial support to aid recovery in the unfortunate event of a cyber incident.
-
Protection against potential cyber threats and data breaches.
-
Financial support and recovery mechanisms in case of a cyber incident.
-
Building client trust through robust security measures.
Eligibility Criteria for the Connector Cyber Liability Application
Determining eligibility for the Connector Cyber Liability Application involves understanding the types of businesses that typically require cyber liability insurance. Various industry standards and regulations inform the prerequisites for application.
-
Types of businesses needing cyber liability insurance include those handling sensitive customer data.
-
Eligibility often depends on industry regulations such as HIPAA or PCI DSS.
-
General eligibility factors include the size of the business and the type of data handled.
How to Fill Out the Connector Cyber Liability Application Online
Filling out the Connector Cyber Liability Application online is a straightforward process. Users can leverage the pdfFiller platform to complete the application efficiently.
-
Access the application form on the pdfFiller website.
-
Fill in the essential information required accurately, including business details and cyber security practices.
-
Review the form for any mistakes to ensure a smooth submission process.
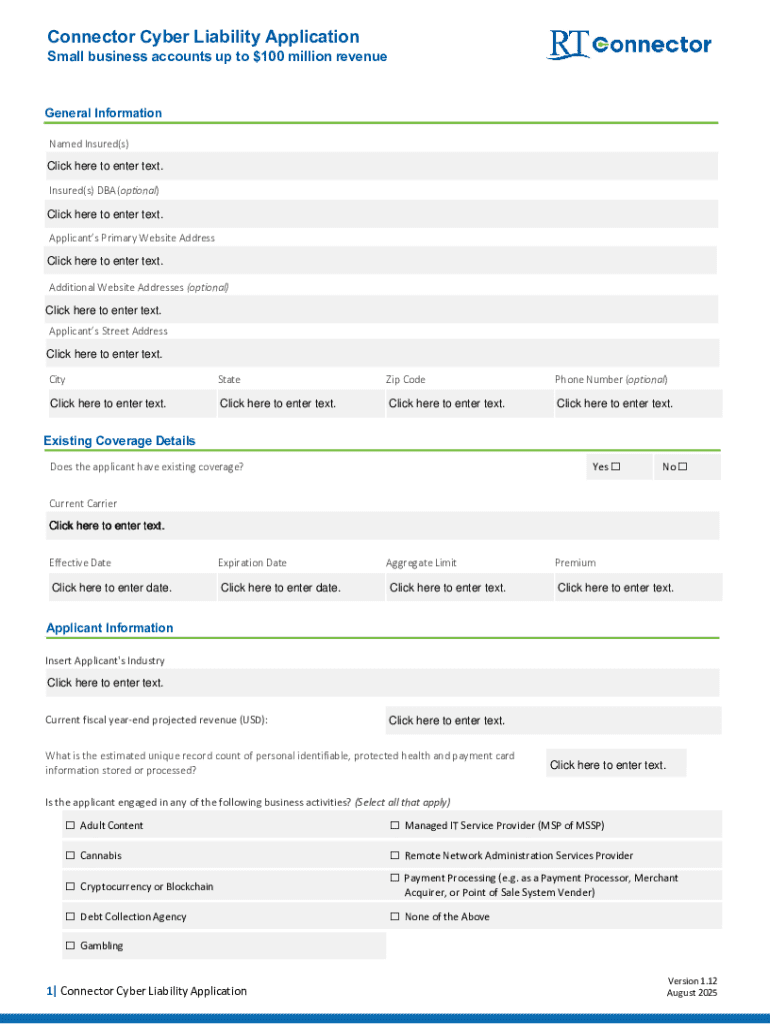
Field-by-Field Instructions for the Connector Cyber Liability Application
Each section of the Connector Cyber Liability Application requires careful attention to detail. Accurate input of information in each field is crucial to avoid application rejection.
-
Breakdown of each field includes specifying business type, size, and data handling practices.
-
Common issues often arise from incomplete fields or ambiguous information.
-
Accuracy is essential to prevent delays or rejections during the review process.
Security and Compliance for the Connector Cyber Liability Application
When handling the Connector Cyber Liability Application, security and compliance must be prioritized. Utilizing the pdfFiller platform ensures that sensitive data is protected during the application process.
-
Security features include 256-bit encryption, ensuring data remains confidential.
-
Compliance with major regulations such as HIPAA and GDPR minimizes legal risks.
-
Data protection is emphasized throughout the application, fostering user trust.
Submission Methods and Delivery for the Connector Cyber Liability Application
Understanding the submission methods and delivery options for the Connector Cyber Liability Application is crucial for a smooth process. Users have several options for submitting their completed applications.
-
Applications can be submitted online via pdfFiller or sent through traditional mail.
-
Tracking submission status is facilitated through the pdfFiller platform.
-
Processing times may vary, so applicants should be aware of realistic timelines for responses.
What Happens After You Submit the Connector Cyber Liability Application
After submitting the Connector Cyber Liability Application, applicants can expect a systematic review process. Understanding what occurs next can alleviate concerns about application status.
-
The review process involves insurers evaluating the provided information.
-
Applicants should anticipate a typical response time based on industry standards.
-
In case adjustments are required, clear next steps will be communicated.
Common Rejection Reasons and Solutions for the Connector Cyber Liability Application
Being aware of common rejection reasons associated with the Connector Cyber Liability Application can help applicants avoid pitfalls. Addressing potential issues before submission is advisable.
-
Common errors include incomplete fields and incorrect data entries.
-
Strategies for correction involve reviewing each section carefully to ensure accuracy.
-
Resources for further assistance are readily available through pdfFiller's support channels.
Experience the Ease of Using pdfFiller for Your Connector Cyber Liability Application
Utilizing the pdfFiller platform enhances the experience of managing your Connector Cyber Liability Application. The user-friendly features make tasks like editing and filling forms more straightforward.
-
Highlight pdfFiller's capabilities for secure form management and completion.
-
The platform's compliance advantages further simplify the application process.
-
Starting the application process is made easy with pdfFiller’s accessible tools.
How to fill out the connector cyber liability application
-
1.To begin, visit pdfFiller and search for 'connector cyber liability application' in the available forms section or use the direct link provided on the landing page.
-
2.Once the form is open, familiarize yourself with the interface. You will see editable fields and areas where specific information is required.
-
3.Before filling out the form, gather necessary information such as your business details, previous insurance coverage data, and any cybersecurity protocols that are currently in place.
-
4.Start filling out the form by clicking on the first field. Enter your business name, address, and contact information accurately.
-
5.Continue to the next sections where you will be prompted to provide information about your business’s cybersecurity measures and any prior claims related to data breaches.
-
6.Make sure that you review each field for completeness and accuracy, ensuring that all required information is filled out before moving on to the next section.
-
7.After completing the form, make use of pdfFiller’s built-in tools to double-check for any missing information or errors that need correction.
-
8.Once you are satisfied with the information provided, you can save the completed form for your records or download it directly to your computer.
-
9.If you are ready to submit, look for the option to send the application through pdfFiller’s submission facilities to your insurance provider.

Who is eligible to apply for the connector cyber liability application?
Eligibility typically includes businesses of various sizes that handle data and require protection against cyber threats. Startups and established firms looking for security coverage are encouraged to apply.
What documents do I need to gather before filling out the application?
Before beginning the application, collect necessary documents such as your business’s legal information, previous insurance policies, recent financial statements, and any cybersecurity certifications your business holds.
How can I submit the completed connector cyber liability application?
Once the application is completed on pdfFiller, you can submit it electronically through the platform, or download it and send it via email or postal service to your insurance provider.
Are there deadlines for submitting this application?
While specific deadlines may vary by insurer, it is recommended to submit your application as soon as possible, especially if you are seeking coverage for a specific upcoming event or renewal.
What are common mistakes to avoid when filling out this application?
Common mistakes include leaving fields blank, providing incorrect information, and failing to review all sections for accuracy. Ensure you double-check all entries before finalizing.
How long does it take to process the application?
Processing times can vary based on the insurer’s workload; however, most applications are reviewed within a few business days. It’s best to inquire with your provider for specific timelines.
What happens if I need to make changes after submitting the application?
If you need to make changes after submission, contact your insurance provider directly to discuss the required adjustments or submit a revised application if necessary.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.