Last updated on Apr 16, 2026

Get the free Michigan NexSys Security Access Form
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is michigan nexsys security access
The Michigan NexSys Security Access form is a document used by authorized personnel to access security features within the NexSys system, facilitating secure operations and data management.
pdfFiller scores top ratings on review platforms




Who needs michigan nexsys security access?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to michigan nexsys security access
What is the Michigan Nexsys Security Access?
The Michigan Nexsys Security Access form serves a critical function in securing sensitive information within the state's document management system. This form is essential for individuals and professionals who require access to various documents that are integral to their work in Michigan.
Understanding the Michigan Nexsys Security Access is vital for users to navigate the process efficiently. It is commonly utilized in contexts where safeguarding sensitive data is paramount, reflecting the overall importance of security access in Michigan's digital infrastructure.
Purpose and Benefits of the Michigan Nexsys Security Access
The Michigan Nexsys Security Access provides several key advantages for users managing documents within the system. Utilizing this access ensures users have the necessary tools for secure document transactions.
-
Improves efficiency in document management processes.
-
Enhances security measures during transactions.
-
Supports compliance with state regulations, minimizing legal risks.
Key Features of the Michigan Nexsys Security Access
Several features make the Michigan Nexsys Security Access form user-friendly and secure. These elements are designed to enhance security while facilitating access for authorized users.
-
Innovative digital capabilities for secure data management.
-
Compliance with regulatory standards, ensuring user safety.
-
User-friendly functionalities, leveraging platforms like pdfFiller for enhanced experience.
Who Needs the Michigan Nexsys Security Access?
Various professionals and individuals may require the Michigan Nexsys Security Access form. It is crucial to identify the target audience to ensure proper usage of the form.
-
Healthcare providers who manage patient documentation.
-
Legal professionals needing access to sensitive legal files.
-
Government employees responsible for document handling.
Failure to secure this access can lead to significant implications, including delays in crucial document processing and compliance issues.
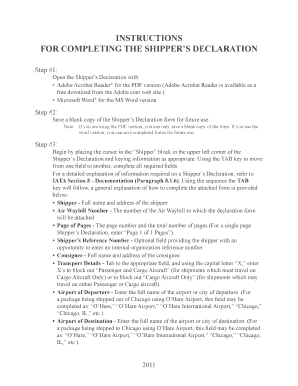
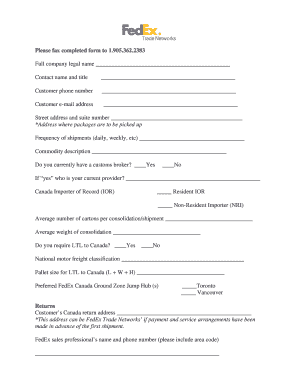
How to Fill Out the Michigan Nexsys Security Access Online (Step-by-Step)
Completing the Michigan Nexsys Security Access form online through pdfFiller is straightforward. Follow the detailed steps below to ensure accurate completion of the form.
-
Access the Michigan Nexsys Security Access form on pdfFiller.
-
Fill out all required fields thoroughly, paying special attention to details.
-
Review your entries to ensure accuracy and completeness before submission.
Tips for using pdfFiller can include familiarizing yourself with the platform for a smoother process and noting any specific fields that demand detailed input.
Common Errors and How to Avoid Them
When filling out the Michigan Nexsys Security Access form, users often encounter common mistakes. Being aware of these pitfalls can facilitate a smoother completion process.
-
Submitting the form with incomplete information.
-
Providing inaccurate details that can lead to rejection.
To minimize errors, it is crucial to double-check all entries and ensure that the information aligns with the requirements before clicking submit.
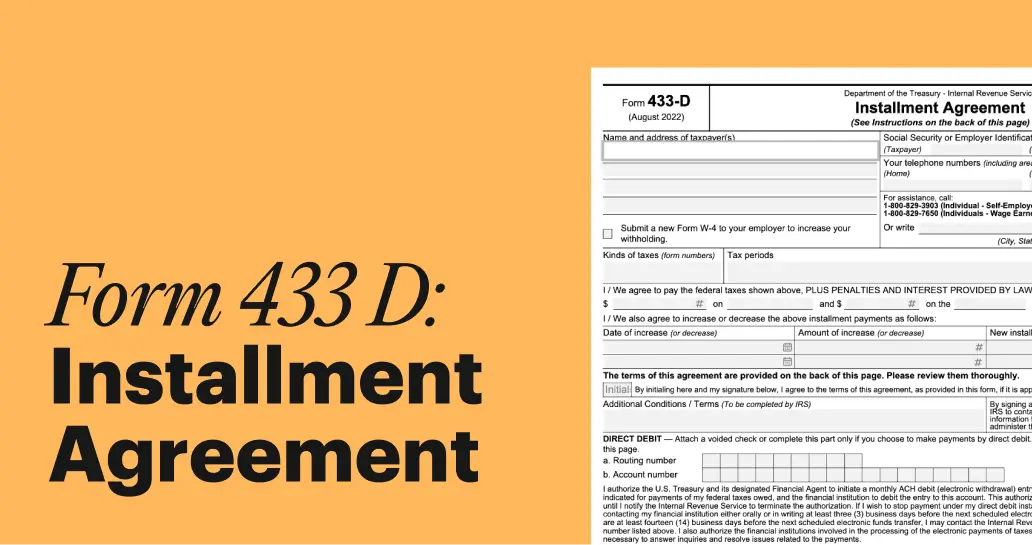
How to Submit the Michigan Nexsys Security Access and Delivery Methods
Understanding the submission methods for the Michigan Nexsys Security Access form will help users ensure timely processing. The following options are available for submission:
-
Online submission through pdfFiller.
-
Mailing physical copies to designated offices.
Be aware of any associated fees and deadlines related to submission to avoid unnecessary delays. Tracking the status of your submission is also recommended to stay informed.
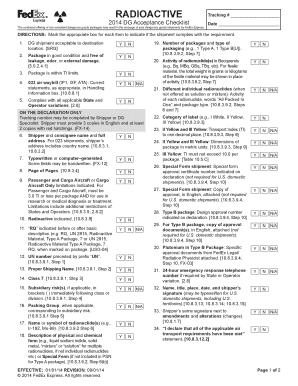
Security and Compliance for the Michigan Nexsys Security Access
Security is paramount when handling the Michigan Nexsys Security Access form. Proper measures must be in place to protect sensitive data from unauthorized access.
-
pdfFiller employs 256-bit encryption for data protection.
-
Compliance with HIPAA and GDPR standards ensures user information is safeguarded.
Prioritizing data protection is essential in the context of document submissions, reinforcing trust in the handling of sensitive material.
Example of a Completed Michigan Nexsys Security Access
Providing a reference example of a filled-out Michigan Nexsys Security Access form can assist users in understanding the completion process better. Consider the following tips when reviewing the example:
-
Analyze the rationale behind specific entries to inform your own completion.
-
Customize the example as needed to fit your unique requirements.
Effortlessly Handle Your Michigan Nexsys Security Access with pdfFiller
pdfFiller provides a user-friendly solution for filling out the Michigan Nexsys Security Access form. The platform streamlines the process, making it easier for users to manage their forms efficiently.
Utilizing pdfFiller not only simplifies the form-filling experience but also reassures users with robust security features and compliance support. Access additional resources on pdfFiller to make the most of your document management needs.
How to fill out the michigan nexsys security access
-
1.Visit pdfFiller's website and log in to your account. If you don’t have an account, create one and log in.
-
2.In the search bar, enter 'Michigan NexSys Security Access' to find the form. Click on the form to open it.
-
3.Familiarize yourself with the layout of the form on pdfFiller. Use the navigation tools to scroll through the document.
-
4.Before filling out the form, gather all necessary information, including authorized personnel details and security preferences.
-
5.Begin completing the form by clicking on the fields where information is required. Type in the relevant data as prompted.
-
6.Use the text features to adjust formatting if necessary. Be sure all information is accurate and complete.
-
7.Once you've filled out all fields, review the entire form carefully to ensure all information is correct.
-
8.Check for any instructions or guidelines that may require additional documentation or signatures.
-
9.After confirming that everything is correct, take advantage of the 'Preview' option to see the completed form.
-
10.Save your work regularly to avoid losing any information. When ready, download a copy for your records.
-
11.Submit the form directly through pdfFiller if submitting electronically, or follow the provided instructions for mailing.

Who is eligible to use the Michigan NexSys Security Access form?
Eligibility typically includes state employees, IT professionals, and approved contractors who need access to security features. Ensure you belong to an authorized group before proceeding.
Is there a deadline for submitting the Michigan NexSys Security Access form?
Deadlines may vary based on specific access requirements. It's advisable to check with your department for any time-sensitive conditions regarding submissions.
What methods can I use to submit the Michigan NexSys Security Access form?
The form can typically be submitted electronically through pdfFiller or printed and mailed to the relevant department. Ensure you follow the submission guidelines provided.
What supporting documents are required when submitting this form?
While the metadata does not specify exact documents, common requirements may include proof of identity or employment. Always verify with the issuer for specific submission needs.
What are common mistakes to avoid when filling out this form?
Ensure all required fields are completed, double-check names and addresses, and review any specific instructions. Skipping steps may delay processing.
What is the typical processing time for the Michigan NexSys Security Access form?
Processing times can vary based on volume and complexity. Generally, allow several weeks for review and approval; check for specific timeframe updates from your department.
Are there any fees associated with the Michigan NexSys Security Access form?
The metadata does not indicate any fees. However, it is prudent to confirm with the relevant department regarding any potential fees that may apply.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.