Last updated on Oct 23, 2015

Get the free NISPOM Chapter 8 Security Checklist
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is NISPOM Checklist
The NISPOM Chapter 8 Security Checklist is a security checklist used by contractors to evaluate their compliance with National Industrial Security Program Operating Manual requirements.
pdfFiller scores top ratings on review platforms




Who needs NISPOM Checklist?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to NISPOM Checklist
What is the NISPOM Chapter 8 Security Checklist?
The NISPOM Chapter 8 Security Checklist is a vital tool used by contractors to evaluate their compliance with the National Industrial Security Program Operating Manual (NISPOM) Chapter 8 requirements. This checklist is essential for assessing adherence to security standards for classified information. It encompasses relevant clauses that are critical for maintaining information security and ensuring responsible management of sensitive data.
By implementing this checklist, organizations can systematically verify their compliance, thereby enhancing their capability to protect classified information effectively. It serves as a foundational element in the broader landscape of regulatory requirements guided by the NISPOM.
Purpose and Benefits of the NISPOM Chapter 8 Security Checklist
The NISPOM Chapter 8 Security Checklist is instrumental in helping contractors maintain compliance with security protocols. By regularly using this checklist, organizations can facilitate security evaluations and audits, minimizing risks associated with mishandling classified information.
Among the primary benefits is the enhancement of readiness in safeguarding vital data. This checklist not only aids in the systematic approach to compliance but also ensures that contractors are better prepared for any security assessments. Thus, the NISPOM compliance form stands as a pillar for professionalism in the realm of classified information security.
Key Features of the NISPOM Chapter 8 Security Checklist
This checklist consists of several components that are crucial for accurate compliance assessment. Key fields such as 'Assessor Name', 'Assessment Date', and targeted compliance questions play a significant role in this process. Additionally, it includes sections dedicated to certification and accreditation, which are essential for validating compliance efforts.
-
'Assessor Name' and 'Assessment Date' fields help document accountability.
-
Compliance questions provide straightforward metrics for evaluation.
-
The certification sections detail necessary approvals for security measures.
-
Protection measures are clearly highlighted to ensure compliance with NISPOM guidelines.
Who Needs the NISPOM Chapter 8 Security Checklist?
The NISPOM Chapter 8 Security Checklist is intended for a variety of contractors and organizations involved in processing classified information. This includes defense contractors, government agencies, and other entities that are required to comply with DoD regulations. Key roles that often necessitate the use of this checklist include security managers, compliance officers, and auditors.
Adhering to the compliance requirements set forth by the Department of Defense is essential for these organizations, ensuring that they consistently uphold the standards for handling sensitive information.
How to Fill Out the NISPOM Chapter 8 Security Checklist Online
Filling out the NISPOM Chapter 8 Security Checklist online involves several essential steps that ensure accuracy and completeness. To start, collect the necessary information required for the various fields in the checklist.
-
Gather key details like the assessor's name and the date of assessment.
-
Carefully read through compliance questions, marking responses accurately.
-
Double-check each section for completeness before submission.
Be mindful of common errors, such as incorrect data entry or missing signatures, to avoid processing delays. This preparation underlines the importance of detail in maintaining compliance.
Digital Signature and Submission of the NISPOM Chapter 8 Security Checklist
When it comes to submitting the NISPOM Chapter 8 Security Checklist, understanding the digital signature requirements is essential. Digital signatures must meet specific criteria comparable to traditional wet signatures, ensuring authenticity and integrity.
Submission methods vary and can include online uploads, email deliveries, or physical submissions depending on organizational policies. It’s also crucial to be aware of any deadlines associated with submissions, along with tracking processes that facilitate accountability.
Security and Compliance Considerations for the NISPOM Chapter 8 Security Checklist
Implementing robust security and compliance measures is critical when dealing with the NISPOM Chapter 8 Security Checklist. Organizations should ensure confidentiality while handling classified information through secure processing methods and data protection regulations.
Record retention requirements for submitted checklists need to be adhered to, along with compliance with relevant regulations such as HIPAA and GDPR. This vigilance underscores an organization’s commitment to privacy and security during the procedural phase.
Using pdfFiller to Complete the NISPOM Chapter 8 Security Checklist
Leveraging pdfFiller to manage and complete the NISPOM Chapter 8 Security Checklist enhances efficiency and user experience. The platform supports document management and eSigning, streamlining the entire process from preparation to submission.
-
pdfFiller offers user-friendly features like customizable templates for document creation.
-
Security features safeguard sensitive information during completion.
-
Editing, filling out, and submitting the checklist becomes a straightforward task with this platform.
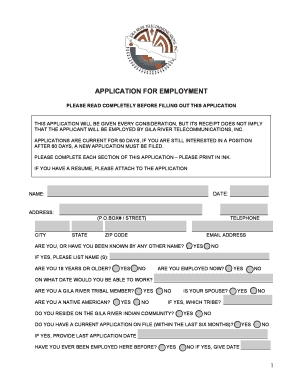
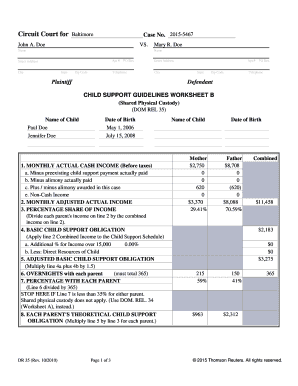
Sample NISPOM Chapter 8 Security Checklist
For users completing the form, a visual reference can be incredibly beneficial. A completed sample of the NISPOM Chapter 8 Security Checklist, with annotations on each section, can guide users in understanding how to accurately fill out their own forms.
By interpreting these examples, individuals can follow structured approaches that enhance their chances of successfully completing the checklist without errors. The sample serves as a practical tool for ensuring compliance and effectiveness in security evaluations.
How to fill out the NISPOM Checklist
-
1.To access the NISPOM Chapter 8 Security Checklist, visit pdfFiller and log in or create a free account.
-
2.Once logged in, use the search bar and enter 'NISPOM Chapter 8 Security Checklist' to locate the form.
-
3.Once you find the form, click on it to open it in the pdfFiller editor.
-
4.Before you start filling out the form, gather necessary information such as the assessor's name, assessment date, and data required for compliance questions.
-
5.Carefully review each section of the checklist, ensuring you understand each question. Use the provided fields to input relevant information or select 'Y' for Yes or 'N' for No.
-
6.Utilize pdfFiller's tools to add text, check boxes, and make any necessary annotations as you complete the form.
-
7.After completing all required fields, take a moment to review your inputs for accuracy and completeness.
-
8.Once satisfied, you can save the completed form for records or download it by selecting the download option.
-
9.If required, you can also submit the checklist directly through pdfFiller by following the prompts to email it to the designated recipient.

Who is eligible to use the NISPOM Chapter 8 Security Checklist?
The NISPOM Chapter 8 Security Checklist is designed for contractors handling classified information, as well as security personnel and compliance officers within government and defense contracting environments.
Is there a deadline for submitting the completed checklist?
While there are no specific submission deadlines related to the checklist itself, contractors must adhere to their project timelines and compliance schedules, ensuring timely evaluations of security protocols.
What is the process for submitting the checklist once completed?
After filling in the NISPOM Chapter 8 Security Checklist on pdfFiller, you can save it for your records or submit it directly via email through the platform to the intended recipient.
Are there any supporting documents required with the checklist?
Typically, the checklist does not require supporting documents. However, it may be beneficial to include any existing security protocols or previous evaluations to provide context.
What common mistakes should I avoid when filling out the checklist?
Common mistakes to avoid include leaving fields blank, misinterpreting compliance questions, and not reviewing the form for accuracy before submission.
How long does it take to process the completed checklist?
Processing times may vary depending on the organization's internal review procedures. Ensure to follow up with the relevant security office for specific inquiries.
Can I edit the checklist once it's been completed?
Yes, in pdfFiller, you can easily edit your completed checklist at any time before final submission or download. Just reopen the document to make necessary changes.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.