Last updated on Oct 23, 2015

Get the free HIPAA Security Checklist
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is HIPAA Checklist
The HIPAA Security Checklist is a healthcare form used by health departments to ensure compliance with HIPAA security rules and protect electronic health information.
pdfFiller scores top ratings on review platforms




Who needs HIPAA Checklist?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to HIPAA Checklist
What is the HIPAA Security Checklist?
The HIPAA Security Checklist plays a crucial role in ensuring compliance with the Health Insurance Portability and Accountability Act (HIPAA). This act is essential for the protection of patient information and mandates strict guidelines for safeguarding electronic protected health information (EPHI). The HIPAA Security Checklist serves as a comprehensive tool for healthcare organizations to evaluate their compliance with HIPAA security rules and to implement necessary security measures.
By utilizing this checklist, organizations can systematically assess their practices and policies regarding the security of patient information. The checklist not only assists in evaluating current security measures but also emphasizes the importance of ongoing compliance and data protection.
Purpose and Benefits of Using the HIPAA Security Checklist
Health departments and organizations must utilize the HIPAA Security Checklist for several reasons. First, administrative safeguards and risk management are vital for effective healthcare operations, ensuring that sensitive patient data is secured appropriately. Regularly reviewing security policies enhances operational integrity and fosters a culture of compliance.
Some significant benefits of using the HIPAA Security Checklist include:
-
Systematic reviews of security policies and procedures.
-
Prevention of data breaches that could lead to severe penalties.
-
Assurance of compliance with government regulations and standards.
Key Features of the HIPAA Security Checklist
The HIPAA Security Checklist includes several essential components designed to facilitate compliance evaluation. Key features encompass risk assessments and specific workforce security procedures that are tailored to an organization’s needs. Users can also expect fields that collect relevant information, such as the name of the HIPAA Security Officer, ensuring accountability within the organization.
Moreover, compliance tracking ensures that all documentation is thorough and up to date. The integration of fillable form elements helps streamline the evaluation process, making it easier for organizations to meet their compliance obligations.
Who Needs the HIPAA Security Checklist?
Various entities must adhere to HIPAA compliance, making the HIPAA Security Checklist essential for a wide range of healthcare stakeholders. Entities such as healthcare providers, health departments, and insurance companies are all required to ensure compliance with HIPAA regulations.
This checklist aids in addressing the compliance needs of different service environments, including:
-
Hospitals
-
Clinics
-
Private practices
How to Fill Out the HIPAA Security Checklist Online (Step-by-Step Guide)
Completing the HIPAA Security Checklist online can streamline the process significantly. The use of pdfFiller enhances accessibility and user experience. Here are the steps to complete the checklist:
-
Access the HIPAA Security Checklist in your browser using pdfFiller.
-
Fill out the key fields, including the Risk Assessment Tool.
-
Ensure that all mandatory fields are completed accurately.
-
Use digital signing options where applicable.
For the best results, take your time to review all entries thoroughly to maintain accuracy and compliance.
Review and Validation Checklist for the HIPAA Security Checklist
Before submitting the HIPAA Security Checklist, it is crucial to validate that the form is completed accurately. Common errors can lead to compliance issues, so attention to detail is necessary. Users should follow these validation steps:
-
Check all required fields to ensure they are complete.
-
Review for any common errors, such as missing signatures.
-
Utilize a final checklist to confirm that all submission requirements are met.
Submission Methods and Delivery of the HIPAA Security Checklist
When it comes to submitting the completed HIPAA Security Checklist, multiple methods are available for users' convenience. Options to consider include:
-
Online submission through pdfFiller.
-
Mailing the form to the appropriate office.
-
In-person submission, if applicable.
It's essential to include any necessary attachments and follow up to confirm receipt and tracking of the submission.
Security and Compliance with the HIPAA Security Checklist
Security is paramount when handling sensitive documents like the HIPAA Security Checklist. pdfFiller offers numerous security features, including 256-bit encryption and compliance with HIPAA and GDPR regulations. Maintaining patient confidentiality during the submission process is critical to uphold the integrity of sensitive information.
Organizations are encouraged to establish guidelines for record retention and privacy protection related to the checklist, ensuring that all data handling is secure and compliant with regulations.
Real-world Implications of Incomplete HIPAA Security Checklists
Neglecting to complete the HIPAA Security Checklist can have serious consequences for healthcare organizations. Risks associated with failing to file or late filing can include hefty penalties and fines. There are real-life scenarios where improper compliance led to data breaches, emphasizing the necessity of diligence and timely reviews.
To avoid these risks, organizations must prioritize reviews and updates to maintain their compliance status consistently.
Get Your HIPAA Security Checklist Ready with pdfFiller
Utilizing pdfFiller for your HIPAA Security Checklist needs simplifies the entire process. Users can easily access features like document sharing and secure storage, enhancing their compliance efforts substantially. The platform's user-friendly interface empowers organizations to fill out the checklist confidently and efficiently.
How to fill out the HIPAA Checklist
-
1.To access the HIPAA Security Checklist on pdfFiller, visit the pdfFiller website and log in to your account or create a new account if you don't already have one.
-
2.Once logged in, use the search bar to find 'HIPAA Security Checklist' and select the correct form from the search results to open it.
-
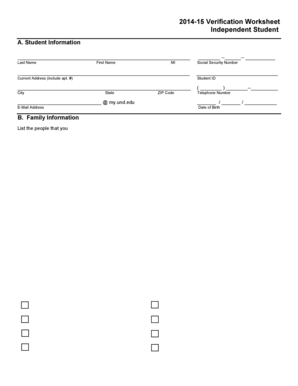
3.Familiarize yourself with the form's layout. The HIPAA Security Checklist consists of multiple sections with fields, checkboxes, and spaces for writing.
-
4.Before filling out the form, gather relevant information such as your organization's current HIPAA compliance status, details of your risk assessment, and security policies that are already in place.
-
5.Begin filling in the fields as prompted. Enter the name of the HIPAA Security Officer in the specified section and check the boxes for all applicable security measures your organization has implemented.
-
6.Continue to complete each section, ensuring you accurately detail your risk management practices and any assessments conducted regarding electronic protected health information (EPHI).
-
7.Regularly save your progress on pdfFiller to prevent data loss. Use the save button often as you complete various sections of the form.
-
8.Once all fields are completed, carefully review the form for accuracy and completeness. Ensure that all necessary information has been provided and is clearly written.
-
9.To finalize the form, utilize the 'Finish' option on pdfFiller, which will prompt you to either download the form, save it to your account, or submit it electronically if required.
-
10.Choose the most suitable option for your needs. If submitting electronically, make sure you follow any additional steps pdfFiller provides for form submission.

Who is eligible to use the HIPAA Security Checklist?
The HIPAA Security Checklist is designed for healthcare organizations, health departments, compliance officers, and risk management teams dealing with HIPAA regulations. Any entity responsible for protecting electronic health information may find this checklist useful.
Are there deadlines for completing the HIPAA Security Checklist?
While there are no specific deadlines for this form, it is advised that organizations regularly review and update their compliance measures to adhere to HIPAA requirements. Conducting security assessments annually is a recommended best practice.
What are the submission methods for the HIPAA Security Checklist?
The completed HIPAA Security Checklist can be saved and downloaded for internal records or submitted to relevant health oversight bodies electronically if required. Refer to your organization's policies for submission guidelines.
What supporting documents are needed with the HIPAA Security Checklist?
Typically, no additional documents are required with this checklist. However, having copies of existing security policies, previous risk assessments, and training records can be helpful for reference while completing the form.
What common mistakes should I avoid when completing the checklist?
Avoid skipping sections, as each part of the checklist is crucial for comprehensive assessment. Ensure that all information is accurate and reflective of your practices. Double-check for readability and completeness before submitting.
How long does it take to process the HIPAA Security Checklist?
Processing times may vary based on your organization's review protocols. Once submitted, allow a reasonable time for compliance officers or health departments to assess and respond to the checklist.
What specific concerns should I consider when using this form?
When using the HIPAA Security Checklist, pay special attention to details regarding risk assessments and the implemented security measures. Ensuring thoroughness in these areas helps mitigate potential compliance issues.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.