Last updated on Oct 24, 2015

Get the free Computer Security Incident Handling Form
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

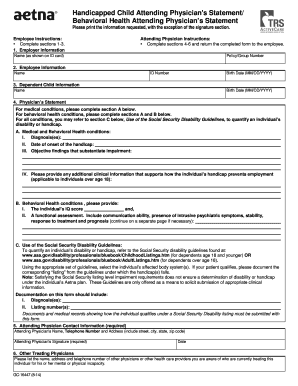
What is Incident Handling Form
The Computer Security Incident Handling Form is a business document used by organizations to manage and document contact information related to computer security incidents.
pdfFiller scores top ratings on review platforms




Who needs Incident Handling Form?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Incident Handling Form
What is the Computer Security Incident Handling Form?
The Computer Security Incident Handling Form serves to document key contact information essential for managing computer security incidents. This form is crucial for ensuring organizations can promptly address security breaches and restore normal operations. It is particularly important for businesses, as it helps streamline incident response and mitigates risks associated with security lapses.
Its relevance stretches across various sectors, underscoring the need for an effective security incident response form tailored to organizational needs. Using a well-structured form allows for clear communication during critical times.
Purpose and Benefits of the Computer Security Incident Handling Form
This form enhances communication by providing a clear protocol to follow during security incidents. By maintaining an updated incident contact list, organizations can ensure swift and efficient responses, which can significantly reduce the impact of an incident.
Having the Computer Security Incident Handling Form readily available promotes preparedness, enabling teams to act decisively when issues arise. This is a vital component of effective security incident management.
Key Features of the Computer Security Incident Handling Form
The form includes several critical sections that facilitate comprehensive incident response. Key components encompass fields such as corporate officers' contact details, local law enforcement information, and vital communications for IT and security teams.
-
Contact details for corporate officers
-
Local law enforcement contact information
-
Dedicated sections for IT department contacts
Each field is designed to capture essential details like names, titles, phone numbers, and email addresses. Regular updates to this form are necessary to maintain accuracy and effectiveness in incident management.
Who Needs the Computer Security Incident Handling Form?
Multiple stakeholders within an organization should complete and maintain the form. Key roles involved include security officers, legal representatives, and members of the IT department, all of whom play pivotal roles in managing incidents effectively.
-
Security officers responsible for incident response
-
Legal representatives for compliance and regulatory guidance
-
IT departments to facilitate technical resolutions
-
External contacts like ISPs and law enforcement agencies
The collaborative nature of the form ensures that all relevant parties are coordinated during incidents, enabling a unified approach to incident management.
How to Fill Out the Computer Security Incident Handling Form Online
Filling out the form online via pdfFiller can be done easily by following these steps:
-
Access the form through pdfFiller’s platform.
-
Enter the required contact details in the specified fields.
-
Review all entered information for accuracy.
-
Save your changes to ensure proper documentation.
It's important to pay close attention to the accuracy of the contact information to facilitate effective incident response. Each field serves a specific purpose in ensuring an organized response protocol.
Common Errors to Avoid When Completing the Form
When filling out the Computer Security Incident Handling Form, users often encounter several common mistakes. These may include entering outdated contact information or leaving mandatory fields blank, which can hinder effective incident response.
-
Failure to update contact information regularly
-
Inaccurate phone numbers or email addresses
-
Not reviewing the completed form for accuracy before submission
To avoid errors, users should utilize a review and validation checklist, ensuring that all provided information is current and correct. If errors are discovered post-submission, users should reach out immediately to rectify the information.
How to Securely Manage the Computer Security Incident Handling Form
When handling the Computer Security Incident Handling Form, it's crucial to prioritize security. pdfFiller offers robust security features that protect sensitive documents, including 256-bit encryption and compliance with regulations like HIPAA and GDPR.
Organizations should also implement strategies to safeguard shared copies of the form, such as restricting access and using secure sharing protocols. Ensuring data security is vital in maintaining confidentiality during incident responses.
How to Save and Share the Computer Security Incident Handling Form
To efficiently download, save, and share the Computer Security Incident Handling Form, users can follow these instructions:
-
Download the form directly from the pdfFiller platform.
-
Save the form in a secure location on your device.
-
Share the document using secure sharing methods provided by pdfFiller.
PdfFiller also offers collaboration features that allow teams to work together effectively on this form, enhancing overall incident management processes.
What Happens After You Submit the Computer Security Incident Handling Form?
Once the Computer Security Incident Handling Form is submitted, users should expect a verification process. This may include receiving confirmation from the relevant departments acknowledging receipt of the submitted form.
Organizations often implement follow-up actions based on the submitted information, and users should be aware of how to track the status of their submitted forms if applicable. Maintaining communication is essential for effective incident management.
Maximize Your Efficiency with pdfFiller for the Computer Security Incident Handling Form
Utilizing pdfFiller for managing the Computer Security Incident Handling Form can greatly enhance your form administration capabilities. Key features include eSigning, document annotations, and seamless conversion of documents across various formats.
Regular updates and maintenance of the form are essential to ensure your organization is prepared to respond effectively to any security incidents that may arise. Leveraging pdfFiller will optimize your incident response strategy.
How to fill out the Incident Handling Form
-
1.Start by accessing pdfFiller and locate the Computer Security Incident Handling Form within their library of templates.
-
2.Open the form by clicking on it, which will display the document in pdfFiller's editing interface.
-
3.Before completing the form, gather all necessary contact information including names, titles, phone numbers, and email addresses relevant to the incident response team.
-
4.Begin filling in the blank fields marked for each role such as corporate security officers and legal affairs officers, ensuring accuracy and clarity.
-
5.Use pdfFiller’s tools to add text easily into each designated field; click on the area where you want to enter information and type directly.
-
6.After completing all required fields, review the form thoroughly for any errors or missing information, ensuring all roles are accurately represented.
-
7.Finalize the form by saving your changes. You can keep a digital copy within pdfFiller or download it as a PDF to your device.
-
8.If required, submit the form directly through pdfFiller's options, or print it for physical submission to the relevant parties.

Who should fill out the Computer Security Incident Handling Form?
This form should be filled out by individuals responsible for managing computer security incidents, including corporate security officers, legal affairs officers, and IT security personnel.
Is there a deadline for completing the Computer Security Incident Handling Form?
There is no specific deadline mentioned for this form. However, it's best to update it regularly to ensure accurate contact information during a security incident.
What information is required to complete the form?
You will need to gather contact details for various roles involved in incident response, including names, titles, phone numbers, and email addresses of corporate security officers and local law enforcement.
Can I submit the form electronically?
Yes, the Computer Security Incident Handling Form can be submitted electronically through pdfFiller, or you can print it for physical submission depending on your organization's requirements.
What are common mistakes to avoid when filling out the form?
Common mistakes include failing to include all relevant contacts, not updating outdated information, and not reviewing the form for accuracy before submission.
How often should the form be updated?
It’s recommended to update the form regularly, particularly when there are changes in personnel or contact information related to security incident management roles.
Is notarization required for this form?
No, notarization is not required for the Computer Security Incident Handling Form, simplifying the process of documentation.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.