Last updated on Oct 24, 2015

Get the free Computer Security Incident Handling Form
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

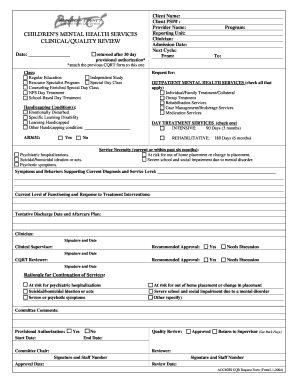
What is Incident Handling Form
The Computer Security Incident Handling Form is a business document used by IT professionals to document and manage computer security incidents.
pdfFiller scores top ratings on review platforms




Who needs Incident Handling Form?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Incident Handling Form
What is the Computer Security Incident Handling Form?
The Computer Security Incident Handling Form is a critical tool for documenting and managing security incidents. This form plays a vital role in ensuring a structured response to security breaches by capturing essential information. It is designed to help organizations track incidents effectively and improve their overall incident management processes.
By utilizing the incident handling form template, teams can streamline documentation and facilitate a quicker response to potential threats. This contributes to a more efficient security posture and better risk management practices.
Purpose and Benefits of Using the Computer Security Incident Handling Form
The primary goal of the Computer Security Incident Handling Form is to ensure thorough documentation of security incidents. This aids in improving incident response times and enhances preparedness for future incidents. By maintaining accurate records, organizations can identify trends and areas needing improvement.
Benefits of using the form include enhanced security preparedness, compliance with legal and regulatory requirements, and better communication during incidents. Utilizing a structured approach to security breach documentation ultimately leads to a more resilient organizational framework.
Key Features of the Computer Security Incident Handling Form
This form includes several key elements that enhance its usability and effectiveness in incident management. Significant features include:
-
Blank fields for capturing crucial information such as the date, time, and details of the incident.
-
Checkboxes for quick assessment of the affected systems and severity.
-
Sections designed to gather detailed information about the incident, including impacted systems and measures taken.
-
Space for documenting follow-up actions and findings post-incident.
These features enable users to collect essential data efficiently and comprehensively, facilitating better analysis and response strategies.
Who Needs the Computer Security Incident Handling Form?
The Computer Security Incident Handling Form is essential for various professionals, including IT specialists, security incident handlers, and business owners. Organizations of all sizes—from small businesses to large enterprises—will benefit from implementing this form in their security protocols.
By understanding the types of professionals who utilize this form, companies can ensure that their teams are prepared to handle security breaches effectively and responsibly.
How to Fill Out the Computer Security Incident Handling Form Online (Step-by-Step)
Completing the Computer Security Incident Handling Form online is a straightforward process designed to be user-friendly. To help guide users, follow these steps:
-
Access the form through pdfFiller’s online platform.
-
Fill in relevant fields, starting with the location(s) of affected systems.
-
Specify the date and time when incident handlers arrived at the site.
-
Indicate whether the affected system is connected to a network by checking the appropriate box.
-
Review your data for accuracy before submitting the form.
This step-by-step approach helps ensure that all necessary information is captured effectively.
Common Errors and How to Avoid Them When Submitting the Computer Security Incident Handling Form
When submitting the Computer Security Incident Handling Form, several common mistakes can occur. To minimize errors, consider the following tips:
-
Ensure all required fields are completed before submission.
-
Double-check for accuracy in the information provided.
-
Be mindful of deadlines associated with incident reporting.
-
Consult team members if unsure about specific details to enhance accuracy.
By following these guidelines, users can improve the quality of their submissions and minimize follow-up queries.
Security and Compliance Considerations for the Computer Security Incident Handling Form
Handling forms securely is critical in ensuring the protection of sensitive information. The Computer Security Incident Handling Form must be managed with strict adherence to security protocols. pdfFiller employs 256-bit encryption and is compliant with regulations such as HIPAA and GDPR, which reassures users about the confidentiality of their data.
It is essential to understand the importance of compliance in security breach documentation to avoid potential legal ramifications and to ensure that all incidents are recorded and handled appropriately.
How to Save, Download, and Share the Completed Computer Security Incident Handling Form
After completing the Computer Security Incident Handling Form, users have several options for managing their document. PdfFiller provides functionalities to:
-
Save the completed form directly to your cloud storage.
-
Download it in PDF format for offline access or archival purposes.
-
Share the document securely with team members or stakeholders through email or other secure channels.
This flexibility enhances collaboration and ensures that all necessary parties have access to the incident details.
What Happens After You Submit the Computer Security Incident Handling Form?
Once the Computer Security Incident Handling Form is submitted, the subsequent steps typically include acknowledgment of receipt and processing of the information. Users should expect possible follow-up communication or requests for additional details if necessary.
It is crucial to keep track of submission status and engage with relevant stakeholders to ensure that incidents are managed and resolved effectively. This tracking helps reinforce an organization's commitment to security and incident management.
Discover the Advantages of Using pdfFiller for the Computer Security Incident Handling Form
pdfFiller offers numerous advantages for completing and managing the Computer Security Incident Handling Form. The cloud-based capabilities of pdfFiller empower users to work from any device without the need for downloads. This eases the form completion process and enhances access for all team members.
The platform’s features, like editing, eSigning, and securing documents, ensure that users can manage their forms confidently and efficiently. Emphasizing the usability of pdfFiller supports a smoother experience when dealing with incident management documentation.
How to fill out the Incident Handling Form
-
1.Access the Computer Security Incident Handling Form on pdfFiller by searching its name in the search bar or navigating via your documents.
-
2.Open the form and familiarize yourself with the layout and fields that need to be filled. Ensure you have the necessary information at hand to facilitate a smooth completion.
-
3.Gather essential information about the incident beforehand, including details on the affected systems like hardware manufacturer, serial number, and network address.
-
4.Begin completing the form by clicking on the blank fields and entering data using your keyboard. Utilize checkboxes where applicable, ensuring accurate documentation of the event.
-
5.Pay careful attention to the sections requiring specifics, such as the date and time personnel arrived at the incident site and if the affected system is connected to a network.
-
6.Once you’ve filled in all necessary fields, review the form for accuracy. Double-check all entries to avoid common mistakes, ensuring all data is correctly recorded.
-
7.After completing your review, you can finalize the form. Save your work by clicking on the save button or download it to your device for records.
-
8.If needed, submit the form electronically through pdfFiller by following the prompts to send it to the intended recipient or keep it for your records.

Who is eligible to use the Computer Security Incident Handling Form?
The Computer Security Incident Handling Form is intended for IT professionals, including incident handlers, cybersecurity teams, and organizational risk management professionals who need to document security incidents.
What is the deadline for completing the incident handling form?
While specific deadlines may vary based on organizational policies, it’s advisable to complete the Computer Security Incident Handling Form as soon as possible after an incident to ensure accurate data collection.
How can I submit the completed form?
You can submit the completed Computer Security Incident Handling Form electronically through pdfFiller. After finalizing your document, use the submit feature to send it to designated recipients or save it for your records.
Are there any supporting documents required when submitting this form?
Typically, additional supporting documents may not be required for the Computer Security Incident Handling Form. However, evidence related to the incident, if available, should be referenced or attached as necessary.
What common mistakes should I avoid when filling out this form?
Avoid leaving fields blank unless instructed. Ensure that all relevant incident details are accurately recorded, specifically the affected systems and network connections, to prevent misinformation.
What is the processing time for reviewing the submitted incident form?
Processing time can vary depending on organizational procedures. Generally, submitted incident forms are reviewed shortly after submission to expedite incident response activities.
Can I edit the form after it has been completed?
Yes, after you've completed the Computer Security Incident Handling Form on pdfFiller, you can make edits as needed before finalizing, saving, or submitting the document.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.