Last updated on Oct 30, 2015
Get the free Cybersecurity Checklist and Action Plan
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.
What is Cybersecurity Checklist
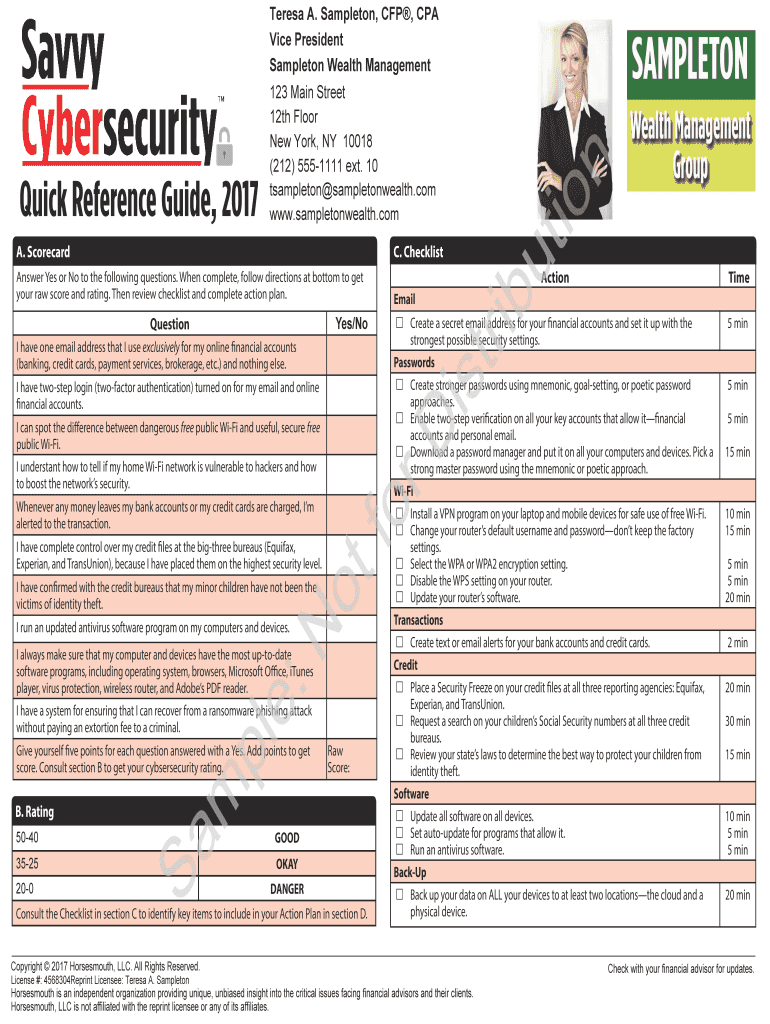
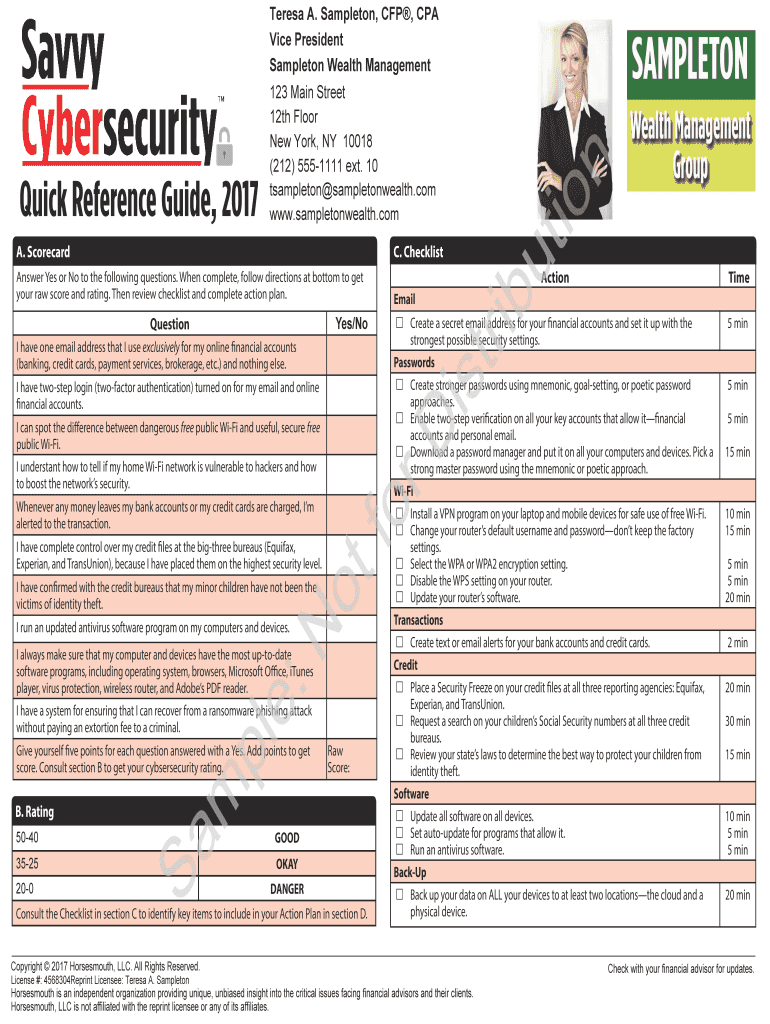
The Cybersecurity Checklist and Action Plan is a checklist template used by individuals to assess and improve their online security practices.
pdfFiller scores top ratings on review platforms




Who needs Cybersecurity Checklist?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Cybersecurity Checklist
What is the Cybersecurity Checklist and Action Plan?
The Cybersecurity Checklist and Action Plan serves as a comprehensive guide aimed at improving online security. This document outlines the checklist, which includes specific questions to evaluate current security practices, and the action plan component that summarizes strategies for enhancements. By utilizing the checklist, users can assess their existing security measures effectively.
Moreover, the action plan is significant as it provides detailed steps to address any identified security vulnerabilities. This structured approach empowers users to take actionable steps towards boosting their online safety.
Purpose and Benefits of the Cybersecurity Checklist and Action Plan
Evaluating current cybersecurity practices is crucial for maintaining robust online defenses. The checklist enriches users' understanding of their security status and the potential risks they face. Following the recommended action plan aids in implementing necessary security measures, thus enhancing overall protection.
Additionally, this document includes resources designed to assist users further, making it a valuable online security guide tailored for diverse needs.
Key Features of the Cybersecurity Checklist and Action Plan
The Cybersecurity Checklist boasts several standout features designed to facilitate user engagement. It includes a format with checkboxes and a rating system, allowing for systematic evaluation of security measures.
Another notable aspect is the signature line that signifies user commitment to improving their cybersecurity. Furthermore, the checklist recommends resources and tools, such as password managers, two-factor authentication methods, and antivirus software, to bolster security practices.
Who Should Use the Cybersecurity Checklist and Action Plan?
This checklist is beneficial for various users, including individuals seeking to enhance their online security. It specifically caters to those concerned about phishing protection and data vulnerabilities. Whether tech-savvy or a beginner, anyone can access and utilize this checklist effectively.
How to Complete the Cybersecurity Checklist and Action Plan Online
Completing the Cybersecurity Checklist online is straightforward. Here are the steps to effectively use the checklist:
-
Open the checklist document and familiarize yourself with each section.
-
Fill out the fields, evaluating your security practices as indicated.
-
Utilize the rating system to score your current cybersecurity measures honestly.
Beware of common mistakes such as overlooking sections or misinterpreting ratings, as these can lead to an inaccurate assessment of your online security.
Submission Methods for the Cybersecurity Checklist and Action Plan
After completing the checklist, users should save and print their responses for record-keeping. Various submission methods are available through pdfFiller, ensuring a seamless process. Users should be aware of potential fees or timelines associated with these submission methods to plan accordingly.
Security and Compliance When Using the Cybersecurity Checklist and Action Plan
When utilizing the Cybersecurity Checklist and Action Plan, the management of personal data is of utmost importance. pdfFiller implements robust security measures, including 256-bit encryption that aligns with compliance standards. This ensures sensitive data is handled securely, and users can trust that their privacy and data protection remain a priority.
Sample Completed Cybersecurity Checklist and Action Plan
To better understand the checklist, users can refer to a sample filled-out version. This visual reference highlights how to engage with each section effectively. Additionally, setting realistic security goals based on one’s evaluations can motivate users to take necessary actions to enhance their online safety.
Final Steps and Commitment to Cybersecurity
Completing the Cybersecurity Checklist and creating a solid action plan summarizes a commitment to online security. Encourage yourself to adopt the recommended strategies outlined in the action plan. Utilizing pdfFiller can further enhance your experience when filling out, saving, and managing your cybersecurity checklist.
How to fill out the Cybersecurity Checklist
-
1.Access pdfFiller and use the search bar to find the Cybersecurity Checklist and Action Plan form.
-
2.Click on the form title to open it in the editor.
-
3.Review the checklist questions, which will help evaluate your current online security measures.
-
4.Use the included rating system to gauge your level of security for each question.
-
5.Gather necessary information like your existing security practices, passwords, and any security software you are using before filling out the form.
-
6.Start filling out the checklist by checking the boxes for practices you currently implement.
-
7.For the areas needing improvement, refer to the action plan recommendations provided in the document.
-
8.Once you have completed the checklist, ensure all fields are filled and that you have a clear understanding of the recommended actions.
-
9.Before finalizing, review the form for any errors or incomplete sections.
-
10.Finish by adding your signature in the designated line to indicate your commitment to enhancing your cybersecurity.
-
11.To save your completed form, find the save option in pdfFiller, and choose the desired format for download or submission.

Who can use the Cybersecurity Checklist and Action Plan?
The Cybersecurity Checklist and Action Plan is designed for individuals and families seeking to improve their online security. It's beneficial for small business owners, parents, students, and professionals handling sensitive information.
Are there any deadlines for completing this checklist?
There are no specific deadlines for completing the Cybersecurity Checklist and Action Plan. However, it is advisable to review and update your cybersecurity practices regularly to stay protected.
What should I do if I need assistance while using the form?
If you require assistance while filling out the form, pdfFiller provides customer support and resources, or you can consider consulting cybersecurity professionals for more personalized help.
What common mistakes should I avoid when completing the checklist?
Common mistakes include overlooking questions that require attention, not gathering necessary information beforehand, or neglecting to review the checklist for completeness before finalization.
Is there a fee associated with using this form?
Using the Cybersecurity Checklist and Action Plan on pdfFiller may involve subscription fees for accessing premium features, but the checklist itself does not have a cost associated with it.
Can I edit the form after I save it?
Yes, once saved, you can return to the Cybersecurity Checklist and Action Plan on pdfFiller and make edits as needed, helping you keep your security measures current.
Do I need to notarize the completed form?
No, notarization is not required for the Cybersecurity Checklist and Action Plan. The form serves as a personal commitment document, making it simple to complete without a notary.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.