Last updated on Nov 1, 2015

Get the free Network Security Indication Application
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is Network Security Application
The Network Security Indication Application is a business form used by companies to apply for network security insurance coverage.
pdfFiller scores top ratings on review platforms




Who needs Network Security Application?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Network Security Application
What is the Network Security Indication Application?
The Network Security Indication Application serves a vital role in helping businesses secure network security insurance. This application is significant for organizations as it establishes their commitment to safeguarding data through comprehensive security controls. Importantly, submission requires a signature from a high-ranking officer, ensuring accountability in the application process.
Purpose and Benefits of the Network Security Indication Application
The primary purpose of this application is to provide businesses with access to network security insurance coverage. Applying for this insurance is crucial as it offers multifaceted protection against potential threats. Key benefits include:
-
Protection against data breaches
-
Minimization of financial loss
-
Enhanced organizational resilience
-
Peace of mind from being insured
Who Needs the Network Security Indication Application?
Understanding who needs the Network Security Indication Application is essential for compliance and risk management. Various businesses and organizations should consider applying, including:
-
Small and medium-sized enterprises
-
Healthcare organizations
-
Financial institutions
-
Marketing agencies with client data management
Moreover, it is critical to adhere to state regulations to ensure eligibility for coverage.
Key Features of the Network Security Indication Application
This application includes several functional features designed to ease the application process. Key components of the form consist of:
-
Fillable fields such as 'Name of Applicant' and 'Street Address'
-
State-specific notices and instructions for accuracy
-
Checkboxes for specific security measures
These features help guide applicants through completing the form accurately.
How to Fill Out the Network Security Indication Application Online
Completing the Network Security Indication Application online can be streamlined through a step-by-step process. Here’s how to fill out the form using pdfFiller:
-
Access the form via pdfFiller’s interface.
-
Navigate through the fillable fields to enter necessary information.
-
Utilize checkboxes for security controls as applicable.
-
Review entries for accuracy before submission.
This process enhances the efficiency of filling out the insurance underwriting form.
Common Errors and How to Avoid Them
To ensure a smooth application process, it's crucial to be aware of common errors that lead to rejections or delays. Common pitfalls include:
-
Inaccurate or incomplete fields
-
Missing signatures from required officers
-
Omitting necessary documentation
To avoid these mistakes, double-check and validate all completed information before submitting your data security application.
How to Submit the Network Security Indication Application
Submission of the completed application involves several methods and requirements. Users can submit the form through:
-
Direct electronic submission via pdfFiller
-
Mailing to the specified insurance carrier address
Additionally, tracking the application status post-submission is crucial for staying informed about approval and any required follow-ups.
Security and Compliance when Filling out the Network Security Indication Application
Users can rest assured regarding the security of their sensitive information during the application process. pdfFiller implements strict security measures, including:
-
256-bit encryption for data protection
-
Compliance with HIPAA and GDPR regulations
-
Soc 2 Type II certification ensuring data integrity
Maintaining privacy while filling out this application is paramount.
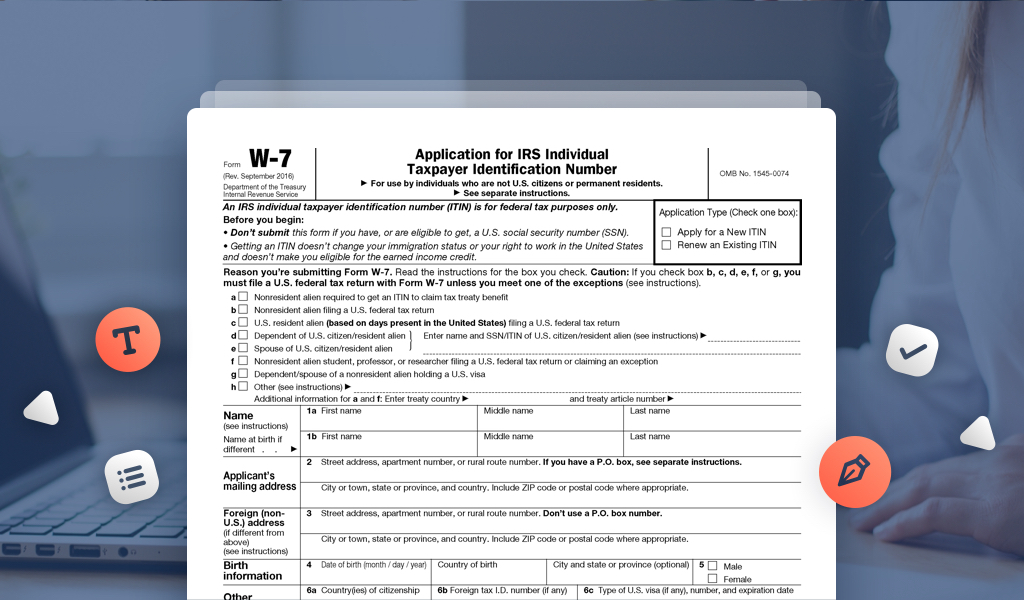
Sample of a Completed Network Security Indication Application
To assist users better, a visual example of a completed application can provide clarity on its format. This sample includes:
-
A breakdown of each section of the application
-
Tips on what information to include
Having a sample facilitates a smoother understanding of the document, thereby streamlining the application process.
Get Started with the Network Security Indication Application through pdfFiller
Utilizing pdfFiller for the Network Security Indication Application simplifies the form-filling experience. The platform allows users to:
-
Quickly fill out the form with relevant features
-
Enjoy additional document management capabilities
With a focus on secure handling of sensitive documents, pdfFiller remains a trusted platform for businesses.
How to fill out the Network Security Application
-
1.Start by accessing the Network Security Indication Application on pdfFiller. Use the search function or enter the URL directly to locate the form.
-
2.Once the form is opened, navigate through the document using the provided toolbar. You can scroll through or use the side panel to jump between sections.
-
3.Before filling out the form, gather necessary details such as your company's data handling practices, security measures in place, and any relevant loss experience.
-
4.Fill in the required fields, including 'Name of Applicant', 'Street Address', 'Website Address', and other pertinent information. Ensure all entries are accurate and complete.
-
5.Utilize pdfFiller’s tools to add checkmarks in checkbox fields where applicable and ensure to follow any specific instructions provided in the form.
-
6.After completing the required fields, review all entries for accuracy. Ensure the form reflects current business practices and information.
-
7.Once satisfied, save your work frequently to avoid losing any information. You can download the completed form as a PDF or submit it directly through pdfFiller.

Who needs to sign the Network Security Indication Application?
The form must be signed by a high-ranking officer of the company, typically someone in an executive role such as a CEO, CFO, or a similar position within the business.
What states are eligible for the Network Security Indication Application?
The application is available for businesses in Arkansas, Colorado, District of Columbia, Florida, Iowa, Kentucky, Maine, New Mexico, New Jersey, New York, Ohio, Oklahoma, Pennsylvania, Tennessee, and Washington.
Are there any notarization requirements for this form?
No, the Network Security Indication Application does not require notarization. However, it must be signed by a qualified officer of the applicant company.
What are common mistakes to avoid when filling out this form?
Common mistakes include providing incomplete information, entering inaccurate data, and failing to sign the form before submission. Double-check all entries to ensure accuracy and completeness.
How do I submit the completed Network Security Indication Application?
You can submit the completed application through pdfFiller via email directly from the platform, or by downloading and sending it to the relevant insurance provider as per their submission guidelines.
Is there a deadline for submitting the Network Security Indication Application?
Deadlines typically depend on your insurance provider's specific criteria. It’s advisable to check with your provider for any time-sensitive requirements related to coverage.
What additional documentation might be required with this application?
While the application itself is comprehensive, you may also need to provide recent loss history reports, security policy documentation, and possibly proof of existing security controls.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.