Last updated on Nov 2, 2015

Get the free IT Essentials 5.0 Lab - Troubleshooting Access Security in Windows 7
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

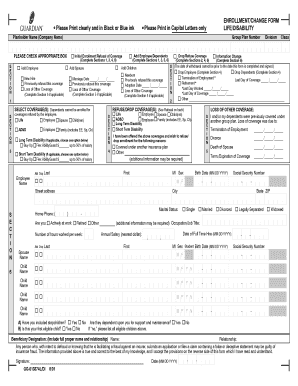
What is Access Security Lab
The IT Essentials 5.0 Lab - Troubleshooting Access Security in Windows 7 is a lab exercise used by students to diagnose and solve access security issues within a Windows 7 environment.
pdfFiller scores top ratings on review platforms




Who needs Access Security Lab?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Access Security Lab
What is the IT Essentials 5.0 Lab - Troubleshooting Access Security in Windows 7?
The IT Essentials 5.0 Lab is an educational exercise aimed at helping students effectively diagnose and solve access security issues within a Windows 7 environment. This lab emphasizes the significance of responding to security breaches, which is crucial for maintaining the integrity of any system. Predefined user accounts and group permissions play essential roles in this process, as they provide a structured way to manage user access and security settings.
Purpose and Benefits of the IT Essentials 5.0 Lab
This lab enables students to practically diagnose and solve Windows 7 access problems, providing an interactive framework to learn critical troubleshooting skills. Through this hands-on experience, participants will develop a deeper understanding of security breaches and how user permissions affect system access.
By engaging with this lab, students not only enhance their technical proficiencies but also gain valuable insights into safeguarding systems against unauthorized access.
Key Features of the IT Essentials 5.0 Lab
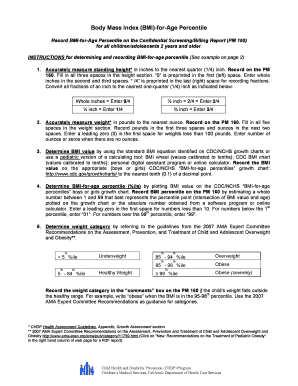
The structure of the IT Essentials 5.0 Lab incorporates various user accounts, including standard users and administrators, facilitating comprehensive practice scenarios. The lab also utilizes tables and documentation that aid in the troubleshooting process.
-
Step-by-step instructions guide users through the troubleshooting exercise.
-
Documentation aids in effectively recognizing and resolving issues.
Who Needs the IT Essentials 5.0 Lab?
Target audiences for the IT Essentials 5.0 Lab include students seeking expertise in Windows 7 security training and IT professionals aiming to refine their troubleshooting skills. Understanding access security is crucial for these groups, as it lays the foundation for successful careers in IT and cybersecurity.
Mastering troubleshooting skills not only enhances technical proficiency but also opens avenues for career advancement in the rapidly evolving tech landscape.
How to Fill Out the IT Essentials 5.0 Lab - Step-by-Step Guide
To successfully complete the IT Essentials 5.0 Lab, follow these steps:
-
Log into the Windows 7 environment using predefined user accounts.
-
Identify and document access issues as they arise.
-
Fill out the provided tables accurately, detailing your findings.
This guided approach ensures a thorough understanding of troubleshooting access security and promotes effective documentation practices.
Common Errors and How to Avoid Them in the Lab
Students often make several common mistakes when completing the IT Essentials 5.0 Lab. These include:
-
Overlooking specific user permissions during troubleshooting.
-
Inadequate documentation of findings and solutions.
To prevent these errors, students should adopt a meticulous approach during the troubleshooting process and ensure thorough documentation of all steps taken.
How pdfFiller Can Simplify Your IT Essentials 5.0 Lab Experience
pdfFiller offers a range of capabilities that enhance the IT Essentials 5.0 Lab experience. It allows users to easily edit and fill out forms necessary for lab documentation.
-
Security features protect sensitive documents from unauthorized access.
-
eSigning options streamline the process for submitting completed lab exercises.
Submission Methods and Delivery for Your Lab Exercise
Once the lab exercise is complete, students can save, print, and submit it through designated methods. Specific digital submission requirements may apply based on institutional guidelines.
Using pdfFiller for submission enhances efficiency and ensures compliance with all submission protocols.
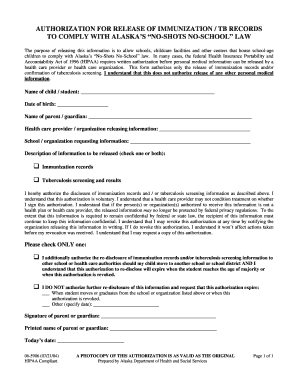
Security and Compliance When Completing the IT Essentials 5.0 Lab
Maintaining document security and compliance is vital when completing the IT Essentials 5.0 Lab. Sensitive documents must be kept secure to prevent data breaches.
pdfFiller adheres to compliance standards and implements robust security measures, ensuring that confidential information remains protected throughout the lab process.
Your Next Steps with the IT Essentials 5.0 Lab Exercise
Get started with the IT Essentials 5.0 Lab exercise using pdfFiller to access an efficient online form completion experience. Explore the platform's features to facilitate the documentation and submission of your lab.
Additionally, consider utilizing other resources and services from pdfFiller for further assistance as you enhance your troubleshooting skills.
How to fill out the Access Security Lab
-
1.Access the IT Essentials 5.0 Lab - Troubleshooting Access Security in Windows 7 form by visiting pdfFiller's website and logging into your account or creating a new one.
-
2.Navigate through the pdfFiller interface to locate your lab exercise. Use the search bar or browse through the education forms category to find the specific lab exercise.
-
3.Before filling out the form, gather necessary information about each user's account, including usernames and specific security access scenarios relevant to the Windows 7 environment.
-
4.Once the form is opened, click on each field to fill in details as instructed, referring to the tables and guidelines provided in the lab exercise. Use the tab key to move between fields easily.
-
5.After completing all entries, review the information carefully to ensure accuracy and completeness. Make any necessary edits by clicking on the specific areas you would like to adjust.
-
6.When satisfied with your completed form, use pdfFiller's save function to store your document. You can also choose to download it to your device or submit it directly through the platform if required.

Who can participate in the IT Essentials 5.0 Lab exercise?
The lab exercise is designed for students enrolled in IT education programs and instructors teaching IT security courses, providing valuable hands-on experience.
What is the deadline for completing the lab exercise?
The deadline for this lab exercise is typically set by your instructor or educational institution. Check with your course syllabus for specific due dates.
How do I submit the completed form?
To submit your completed lab exercise, download the document from pdfFiller and follow your instructor's submission guidelines, which may include email or online portal submissions.
What information do I need to complete the form?
Before starting, ensure you have access to user account details including roles and permissions for Brooks, Shawna, Devon, and the administrator in the Windows 7 environment.
What are common mistakes to avoid when filling out the lab?
Avoid leaving fields blank or misrepresenting user roles. Ensure to follow the specified troubleshooting steps to accurately document your findings.
How long does it take to process my submission?
Processing time varies based on your instructor's review and feedback cycle. Typically, allow several days to a week for evaluation.
Is there a fee to access this lab exercise?
Accessing the IT Essentials 5.0 Lab through pdfFiller usually does not incur a fee, but check with your educational institution for any potential costs associated.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.