Last updated on Nov 9, 2015

Get the free Information Security Incident Reporting Form
We are not affiliated with any brand or entity on this form
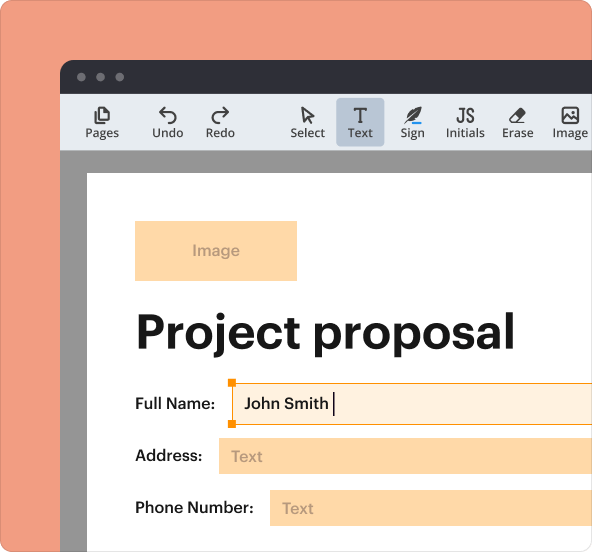
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

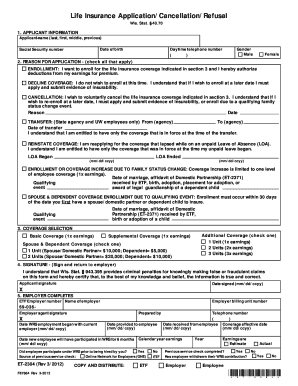
What is Incident Report Form
The Information Security Incident Reporting Form is a legal document used by organizations in the United States to report cybersecurity incidents and request assistance.
pdfFiller scores top ratings on review platforms




Who needs Incident Report Form?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Incident Report Form
What is the Information Security Incident Reporting Form?
The Information Security Incident Reporting Form (OIT-0142) serves as a crucial tool for reporting cybersecurity incidents. It empowers organizations to systematically document and report information security breaches, ensuring that incidents are managed effectively. By utilizing this form, users can seek immediate assistance and support from relevant authorities.
Purpose and Benefits of the Information Security Incident Reporting Form
Organizations in the U.S. can significantly benefit from using the Information Security Incident Reporting Form. The form aids in proper documentation during investigations and remains compliant with legal requirements surrounding cybersecurity. Additionally, it enables organizations to capture essential details for thorough analysis.
Who Needs to Use the Information Security Incident Reporting Form?
The Information Security Incident Reporting Form is designed for various users, including governmental entities and private organizations. Industries such as healthcare, finance, and information technology may frequently utilize the form. Specific roles, like compliance officers and cybersecurity professionals, are essential for its effective use.
Information You'll Need to Complete the Form
-
Incident description and timeline
-
Affected systems and data
-
Details of individuals involved
-
Contact information for follow-up
-
Any preliminary actions taken
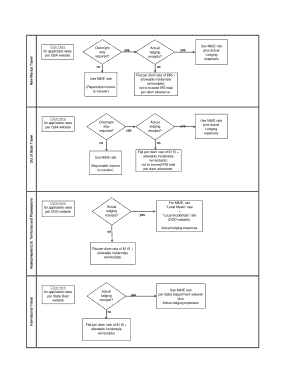
Step-by-Step Guide: How to Fill Out the Information Security Incident Reporting Form
Completing the Information Security Incident Reporting Form online is straightforward. Begin by accessing the designated platform and follow these steps:
-
Enter your organization's name and contact details.
-
Provide a detailed incident description, including what occurred.
-
List all systems and data that may have been affected.
-
Document any actions that have already been taken.
-
Review your information for accuracy before submission.
How to Submit the Information Security Incident Reporting Form
After completing the form, you must submit it through the appropriate channels. Submission methods may vary by jurisdiction, and timely filing is crucial to avoid potential penalties. Be aware of any associated timelines or fees that may apply to ensure compliance.
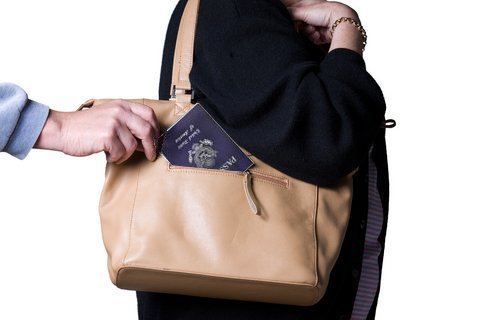
Security and Compliance Considerations for the Information Security Incident Reporting Form
When filling out the Information Security Incident Reporting Form, security measures are paramount. pdfFiller employs 256-bit encryption to protect sensitive data and ensures compliance with HIPAA and GDPR. These precautions help maintain confidentiality and integrity throughout the submission process.
Reviewing Your Submission: What Happens After Filing?
Once you submit the form, it undergoes a review process. Users can track their submissions through designated channels. Be mindful of common rejection reasons, such as incomplete information, and know how to amend your form if necessary.
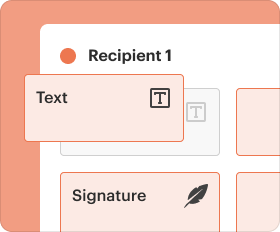
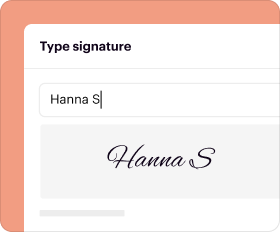
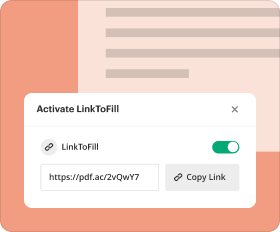
Utilizing pdfFiller for Your Information Security Incident Reporting Form
pdfFiller provides a seamless experience for completing the Information Security Incident Reporting Form. Users can easily fill out, edit, and submit the form with features like eSigning and cloud storage. The platform ensures that your documents are accessible and secure.
Examples of Completed Information Security Incident Reporting Form
For guidance, refer to examples of completed Information Security Incident Reporting Forms. These samples highlight correct field usage and commonly accepted formats, allowing users to understand how to best fill out their forms.
How to fill out the Incident Report Form
-
1.To access the Information Security Incident Reporting Form on pdfFiller, navigate to the pdfFiller website and search for 'Information Security Incident Reporting Form' or use a direct link if available.
-
2.Once you have opened the form, familiarize yourself with the layout, including fillable fields, checkboxes, and instructions that assist you in completing the form accurately.
-
3.Before beginning, gather all necessary information, including details about the incident, affected systems, and your contact information, as this will ensure you can complete the form without delays.
-
4.Click on each field to enter your information. Use pdfFiller's intuitive interface, which allows easy navigation between sections. If you need to make changes, simply click on the relevant field and update as needed.
-
5.Once you have filled in all required fields and provided detailed descriptions where necessary, review the information carefully to ensure accuracy and completeness.
-
6.After finalizing the form, save your work. pdfFiller allows you to download the completed document as a PDF or save it directly to your account for submission.
-
7.To submit the form, follow the instructions provided on pdfFiller. You may have the option to print it out for manual submission or submit electronically, depending on your specific needs.
What are the eligibility requirements for using the Information Security Incident Reporting Form?
Any organization in the United States facing cybersecurity incidents is eligible to use the Information Security Incident Reporting Form to report their incident and seek assistance.
Is there a deadline for submitting the information security incident report?
It is advisable to submit the Information Security Incident Reporting Form as soon as possible after discovering a cybersecurity incident to ensure timely assistance and investigation.
How do I submit the Information Security Incident Reporting Form?
You can submit the Information Security Incident Reporting Form by downloading it from pdfFiller after completion and either mailing it to the appropriate agency or submitting it electronically, if allowed.
What supporting documents are required with the cybersecurity incident report?
Typically, you may need to provide documentation related to the incident, including logs, evidence of the breach, and organizational contact information to enhance the report's validity.
What are common mistakes to avoid when filling out the form?
Common mistakes include missing required fields, providing incomplete information about the incident, and failing to review the form before submission, which could delay processing.
How long does it take to process the Information Security Incident Reporting Form?
Processing times can vary based on the agency and the specifics of the incident. Typically, you should expect a response within a few weeks, but check with the relevant agency for their specific timeline.
What should I do if I have concerns after submitting the form?
If you have any concerns post-submission, directly contact the agency to which you submitted the Information Security Incident Reporting Form to inquire about its status and address any issues.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.