Last updated on Dec 6, 2015

Get the free Information Security Risk Assessment Manual
We are not affiliated with any brand or entity on this form
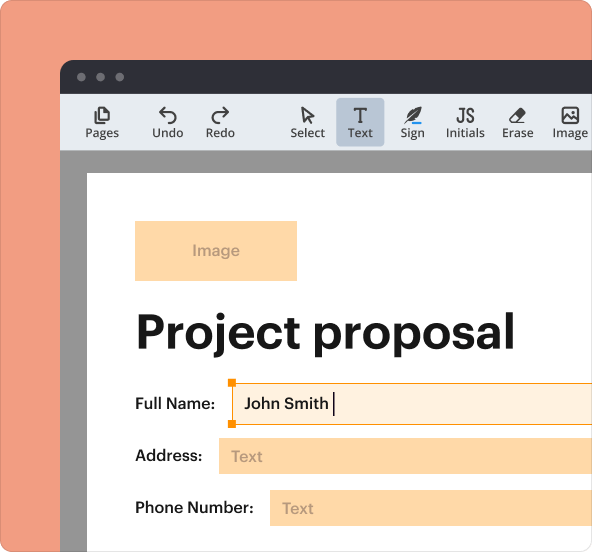
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

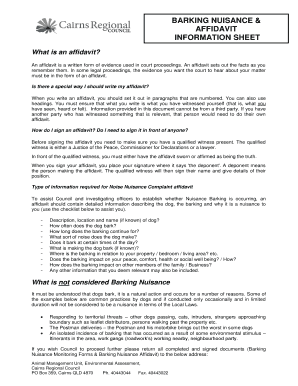
What is Security Risk Assessment
The Information Security Risk Assessment Manual is a business form used by organizations to identify and rectify weaknesses in information security compliance.
pdfFiller scores top ratings on review platforms




Who needs Security Risk Assessment?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Security Risk Assessment
What is the Information Security Risk Assessment Manual?
The Information Security Risk Assessment Manual is a comprehensive guide designed to assist organizations in identifying and rectifying weaknesses in their information security landscape. The primary purpose of this manual is to ensure that organizations effectively conduct security risk assessments tailored to their specific needs.
Conducting a security risk assessment is crucial for protecting sensitive information and ensuring compliance with relevant laws and regulations. Prominent regulations like HIPAA underscore the importance of this manual, as it serves as a reliable resource for organizations navigating the complexities of information security.
Purpose and Benefits of the Information Security Risk Assessment Manual
This manual serves not only as a tool for identifying vulnerabilities but also as a foundation for fostering compliance across federal and state regulations regarding sensitive data management. By utilizing this manual, organizations can enhance their security posture and reinforce their organizational security policies.
-
Identifies weaknesses in information security systems.
-
Ensures compliance with applicable laws related to sensitive data.
-
Strengthens organizational security practices and policies.
Key Features of the Information Security Risk Assessment Manual
The features of the Information Security Risk Assessment Manual provide invaluable assistance in conducting thorough risk assessments effectively. These distinctive traits make it a practical tool for organizations aiming to safeguard sensitive information.
-
Includes detailed checklists that streamline the risk assessment process.
-
Contains sections prompting user input, such as 'Organization Name' and 'Name of Individual Completing Risk Assessment.'
-
Utilizes a template format conducive to easy modifications and updates.
Who Needs the Information Security Risk Assessment Manual?
This manual is particularly beneficial for various sectors, including healthcare providers, financial institutions, and any organizations handling confidential information. It plays a vital role in ensuring compliance and facilitating effective risk management strategies within these enterprises.
-
Target audiences include healthcare providers and financial organizations.
-
Essential for maintaining compliance and risk management practices.
-
Applicable in various scenarios where sensitive data is managed.
How to Fill Out the Information Security Risk Assessment Manual Online (Step-by-Step)
Completing the Information Security Risk Assessment Manual involves a structured approach to ensure thorough and accurate documentation. Following these steps will guide users in effectively filling out the manual.
-
Gather all necessary information related to your organization and its security measures.
-
Begin filling out each section of the manual as prompted.
-
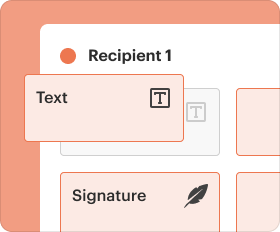
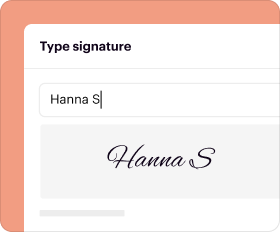
Utilize pdfFiller’s online tools for convenient editing and signing of the document.
Common Errors and How to Avoid Them When Filling Out the Manual
When completing the Information Security Risk Assessment Manual, users may encounter several common pitfalls. Being aware of these potential errors can significantly enhance the accuracy and effectiveness of the submission.
-
Inputting incorrect information in specified fields.
-
Misunderstanding the intent of different sections of the manual.
-
Failing to review the completed manual to ensure compliance with guidelines.
How to Submit the Information Security Risk Assessment Manual
Submitting the completed Information Security Risk Assessment Manual is crucial for operational compliance. This section outlines the processes to follow for an efficient submission.
-
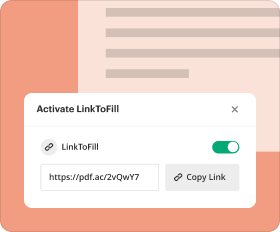
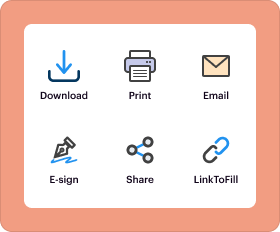
Identify suitable submission methods, whether digital platforms or physical formats.
-
Prepare any necessary documents that accompany the completed manual.
-
Track the status of your submission as per the method used.
Benefits of Using pdfFiller for the Information Security Risk Assessment Manual
Utilizing pdfFiller for editing and managing the Information Security Risk Assessment Manual offers numerous advantages. The platform enhances the user experience while ensuring robust security for sensitive information.
-
Facilitates editing, eSigning, and secure storage of your manual.
-
Employs 256-bit encryption, adhering to HIPAA and GDPR compliance standards.
-
Features user-friendly tools that simplify the completion and management of forms.
Privacy and Data Protection with the Information Security Risk Assessment Manual
Maintaining privacy and adhering to data protection regulations are paramount when handling sensitive information. This manual supports organizations in achieving compliance while reinforcing best data protection practices.
-
Guides organizations in ensuring compliance with data protection laws.
-
Recommends strategies for protecting sensitive data during assessments.
-
Emphasizes the necessity of staff training on handling confidential information.
Embrace Your Responsibility with the Information Security Risk Assessment Manual Today
Organizations are encouraged to actively engage with the Information Security Risk Assessment Manual to enhance their security measures. Securing sensitive information and complying with pertinent regulations are essential steps for effective risk management.
-
Fill out the Information Security Risk Assessment Manual using tools available via pdfFiller.
-
Recognize the critical nature of securing sensitive information.
-
Understand the overall benefits of being proactive in risk management and information security.
How to fill out the Security Risk Assessment
-
1.Access the Information Security Risk Assessment Manual on pdfFiller by searching for its title in the platform's search bar.
-
2.Open the document once it appears in the search results to begin completing your assessment.
-
3.Before filling out the form, gather necessary information, including your organization's name, the individual responsible for the assessment, and relevant security policies.
-
4.Use the navigation tools in pdfFiller to scroll through the checklist and fill in any blank fields promptly.
-
5.For each checkbox, specify whether the corresponding security measure is in place or not by clicking on the checkbox within the pdfFiller interface.
-
6.Once all fields are completed, review the form carefully to ensure all information is accurate and that you have addressed each checklist item.
-
7.Finalize the form by selecting the 'Save' option in pdfFiller to store your progress or choose 'Download' to save a copy to your device.
-
8.If needed, you can also submit the completed form directly from pdfFiller using any available submit options.
Who should use the Information Security Risk Assessment Manual?
Any organization that manages sensitive or confidential information such as healthcare providers, financial institutions, and educational entities should consider using the Information Security Risk Assessment Manual.
Is the Information Security Risk Assessment Manual compliant with HIPAA?
Yes, the Information Security Risk Assessment Manual is designed to help ensure compliance with HIPAA alongside other federal and state regulations relevant to information security.
What information is required to complete the form?
You'll need to provide your organization's name, relevant security policies, and the name of the person completing the risk assessment to fill out the Information Security Risk Assessment Manual accurately.
How can I submit the completed form?
Once you finalize the form within pdfFiller, you can save it to your device or submit it directly using the submission features available on the platform.
Are there common mistakes to avoid when filling out this manual?
Ensure that you thoroughly address all checklist items and input accurate data. Missing fields or unchecked checkboxes can lead to compliance issues.
What is the processing time for reviewing the completed manual?
The processing time depends on your organization’s internal review procedures, but ensure you allow sufficient time for any necessary adjustments and approvals.
Can I edit the form after downloading it?
Yes, once you download the completed Information Security Risk Assessment Manual, you can use PDF editing software to make any necessary changes or additions.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.