Last updated on Dec 7, 2015

Get the free IT Security Access Request Form
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

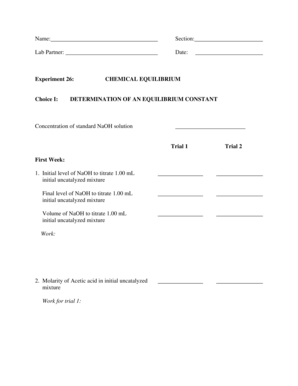
What is IT Access Request
The IT Security Access Request Form is a service agreement used by employees to request access to various IT resources and systems.
pdfFiller scores top ratings on review platforms




Who needs IT Access Request?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to IT Access Request
What is the IT Security Access Request Form?
The IT Security Access Request Form is a vital document used by employees to formally request access to various IT resources and systems. This form ensures that there is a structured process for requesting access and highlights the necessity for approvals. Employees must submit this request because access to sensitive IT systems is restricted and must be carefully tracked to maintain security protocols.
A key aspect of this process is the requirement for manager approval, which provides an additional layer of oversight and accountability, thereby helping to mitigate the risk of unauthorized access to critical data.
Purpose and Benefits of the IT Security Access Request Form
The IT Security Access Request Form streamlines the access request process, making it easier for employees to gain the necessary permissions. By documenting all access requests, the form enhances security and accountability within the organization. This documentation reduces the risk of unauthorized access to sensitive IT resources, which is crucial for maintaining data integrity and compliance.
Furthermore, having a standardized form helps in ensuring that all requests for network access are treated consistently, fostering a secure IT environment.
Key Features of the IT Security Access Request Form
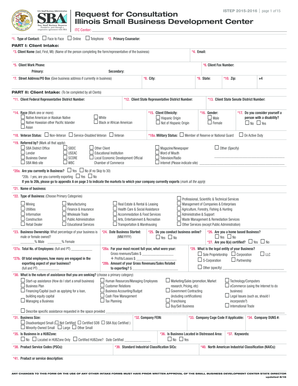
The IT Security Access Request Form includes several essential components that facilitate its use:
-
Personal information such as name, department, and contact details.
-
Employment details including role, start date, and justification for access.
-
Access type, specifying what resources the employee is requesting access to.
Additionally, the form contains blank fields for user input, checkboxes for selection, and a designated signature section for managers to confirm their approval. The design of the form has been carefully constructed to enhance user experience, aiming for clarity and ease of use.
Who Needs to Use the IT Security Access Request Form?
This form is primarily utilized by employees who need to request IT access including both new hires and existing employees undergoing transitions in their roles. Managers play a crucial role by approving the access requests, while IT administrators are responsible for overseeing the access process to ensure compliance with organizational policies.
By delineating the roles involved, the form helps clarify responsibilities and streamline the access approval workflow.
How to Fill Out the IT Security Access Request Form Online (Step-by-Step)
Following these steps will help ensure that the IT Security Access Request Form is filled out accurately:
-
Gather necessary information about your employment role and the specific type of access required.
-
Complete required fields, ensuring personal and employment details are accurate.
-
Select the appropriate access type through the checkboxes provided.
-
Obtain the necessary manager approval before submission.
Being thorough and accurate while filling out the form is essential, as this minimizes the chances of common errors that could delay processing.
Review and Validation Checklist for Your IT Security Access Request Form
Before you submit the IT Security Access Request Form, it is vital to perform a final review:
-
Verify that all essential information is complete and correct.
-
Check for common mistakes, particularly in personal and employment information.
-
Ensure that the manager's signature is included as it is required for final approval.
Having a strong review process in place ensures that requests are submitted without unnecessary delays.
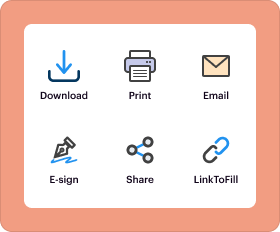
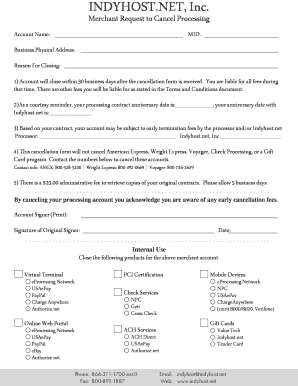
How to Submit the IT Security Access Request Form
There are several methods available for submitting the IT Security Access Request Form:
-
Online submission through the designated internal portal.
-
Email submission to the IT department, with the completed form attached.
-
In-person submission at the IT office for immediate processing.
After submission, employees can expect a processing time that may vary based on department workloads. It’s also helpful to inquire about confirmation of submission and tracking for ongoing access requests.
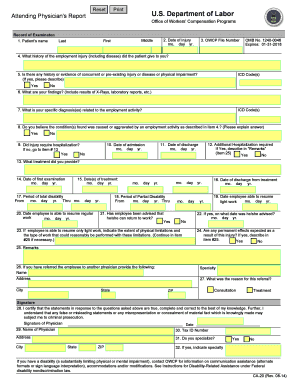
Security and Compliance for the IT Security Access Request Form
Security concerns regarding the IT Security Access Request Form must be addressed thoughtfully:
-
Encryption and data protection measures are crucial for safeguarding sensitive employee information.
-
The form must comply with relevant regulations such as HIPAA and GDPR to ensure that personal data is handled appropriately.
-
Best practices should be adopted for the secure handling and storage of completed forms.
By implementing these measures, organizations can maintain compliance while protecting sensitive information effectively.
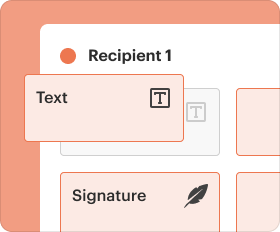
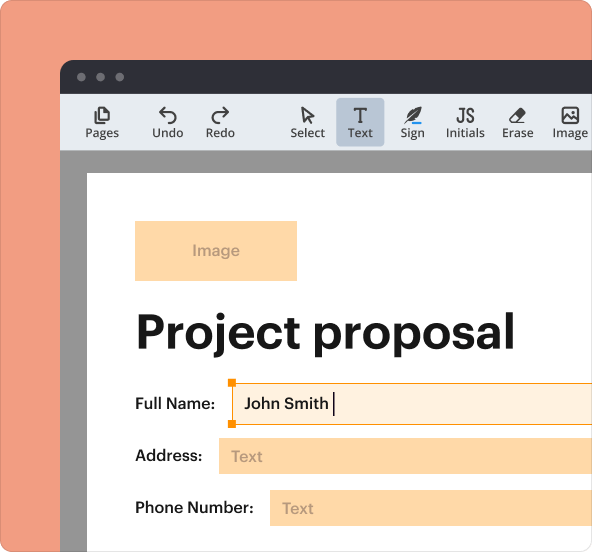
Using pdfFiller to Complete Your IT Security Access Request Form
pdfFiller provides robust features that enhance the process of completing the IT Security Access Request Form:
-
Editing capabilities allow for modifications to personal details directly on the form.
-
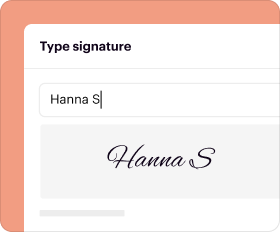
eSigning functionality ensures signatures can be added securely without printing.
-
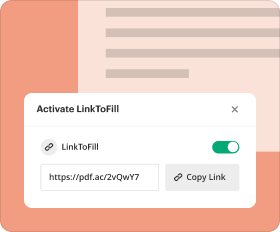
Secure sharing options make it easy to send the completed form to the necessary parties.
Utilizing pdfFiller helps streamline the completion process, providing a user-friendly and secure experience for employees.
How to fill out the IT Access Request
-
1.To begin, access pdfFiller and log into your account. Use the search bar to find the IT Security Access Request Form by entering its name.
-
2.Open the form by clicking on it to load it in the pdfFiller interface. Familiarize yourself with the available tools on the side menu.
-
3.Before filling out the form, gather all necessary information, including your employee ID, the specific IT resources you are requesting access to, and your manager's contact details for approval.
-
4.Navigate through the form by clicking on each field that needs to be completed. Enter your personal and employment details accurately, as these are crucial for processing your request.
-
5.For the 'Type of Access Needed' section, select the appropriate options from the checkboxes provided. Make sure to provide detailed information where necessary for clarity.
-
6.After providing all the required information, refer to the instructions on the form to ensure you have filled everything out correctly, especially the signature section for manager approval.
-
7.Once you are satisfied with the completed form, utilize the 'Save' option to store your progress. You can also download the form as a PDF by clicking on the download icon.
-
8.Finally, submit the form through your company's designated submission method, which may include emailing your completed form to the IT department or uploading it to an internal portal.
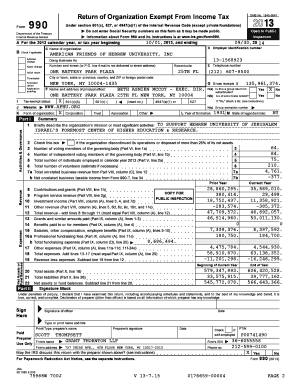
Who is eligible to use the IT Security Access Request Form?
The IT Security Access Request Form is designed for employees needing access to IT resources and systems. Employees must have a valid reason for access, which will require manager approval.
What is the deadline for submitting this form?
While specific deadlines may vary, it is recommended to submit the IT Security Access Request Form as soon as the need for access arises to avoid delays in processing your request.
How should I submit the completed form?
Once completed, the IT Security Access Request Form can typically be submitted via email to the IT department or through your organization’s internal management system, depending on company policy.
Are there any supporting documents required?
Generally, the IT Security Access Request Form does not require additional supporting documents. However, it's advisable to check with your IT department if any specific documentation is needed.
What are common mistakes to avoid when filling out this form?
Ensure that all fields are filled out completely and accurately. Common mistakes include missing signatures, incorrect employee details, and failing to specify the type of access needed.
How long does it take to process the access request?
Processing times can vary, but you should typically expect a response within a few business days after submission, depending on the workload of the IT department.
Is this form still valid if it was last revised in 2012?
While the IT Security Access Request Form has not been updated since 2012, it is still important to complete it as required by your organization’s current IT security policies.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.