Last updated on Jan 2, 2016
Get the free Risk Assessment Checklist - Acquire and Implement
We are not affiliated with any brand or entity on this form
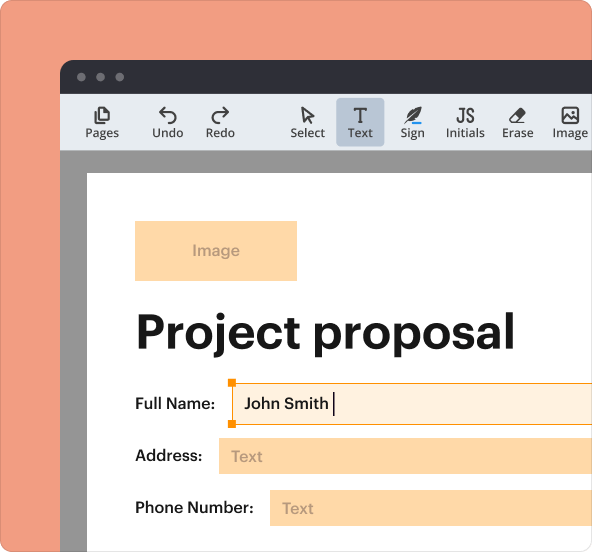
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.
What is Risk Assessment Checklist
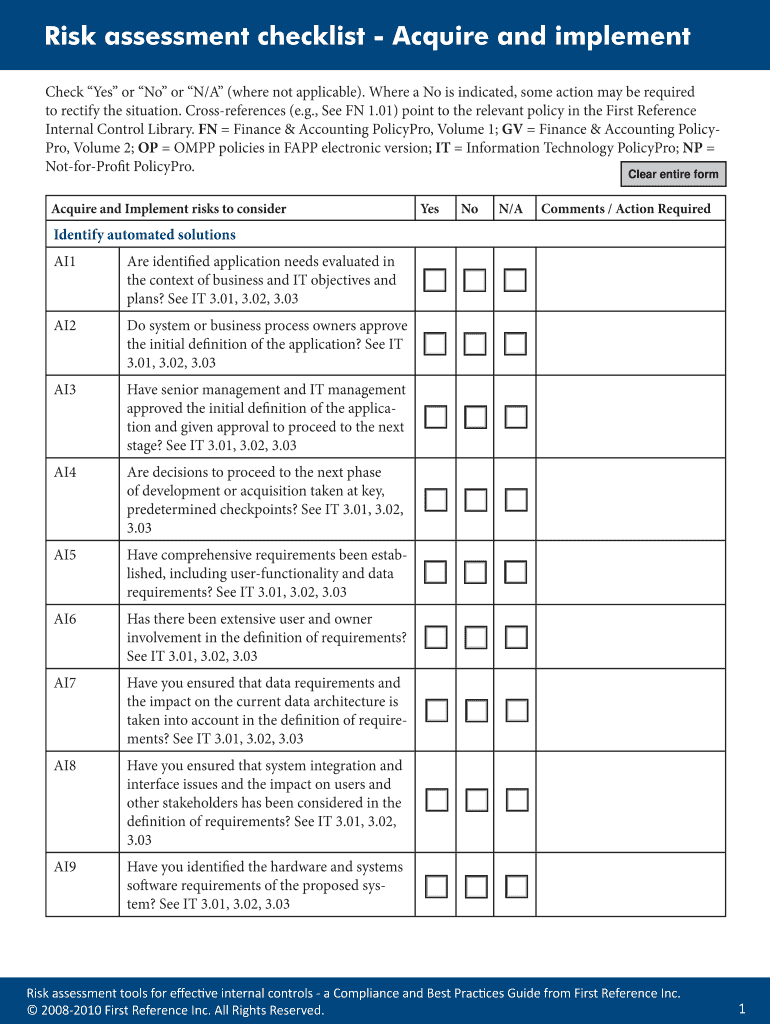
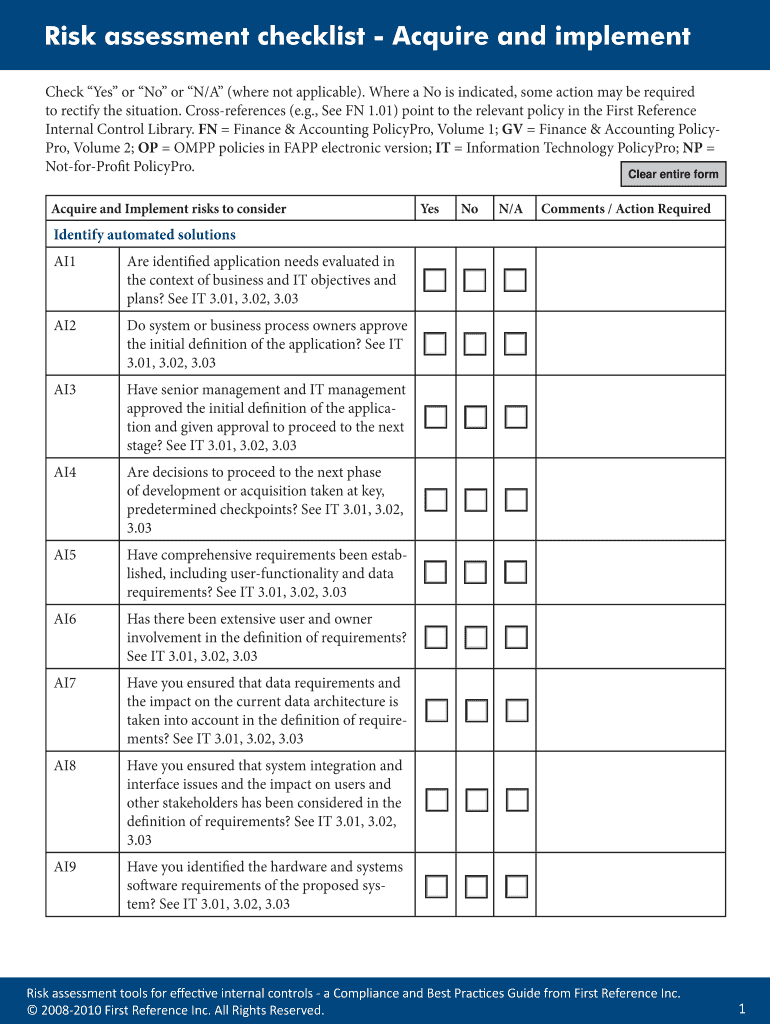
The Risk Assessment Checklist - Acquire and Implement is a risk management form used by organizations to evaluate and manage risks associated with system acquisitions and implementations.
pdfFiller scores top ratings on review platforms




Who needs Risk Assessment Checklist?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Risk Assessment Checklist
What is the Risk Assessment Checklist - Acquire and Implement?
The Risk Assessment Checklist is a crucial tool designed for assessing risks associated with system acquisition and implementation. Its main objective is to aid businesses in evaluating potential risks during the acquisition process, thereby fostering informed decision-making. By identifying risks early, organizations can put internal controls in place, enhancing their overall risk management efforts.
This checklist serves as an internal controls guide, helping to ensure that risks are systematically identified and addressed. Its structured approach promotes thorough evaluations, contributing to the reduction of unforeseen issues during system implementations.
Purpose and Benefits of the Risk Assessment Checklist
The significance of the Risk Assessment Checklist lies in its ability to guide organizations through compliance and best practices. It aids in the identification, assessment, and mitigation of various risks that may emerge during system acquisition. Utilizing this checklist ultimately supports effective IT risk management, fostering a secure and compliant operational environment.
By implementing this checklist, organizations can standardize their approaches to risk management, promoting consistency and reliability through documented evaluations and action plans.
Key Features of the Risk Assessment Checklist - Acquire and Implement
The structure of the Risk Assessment Checklist includes a series of questions that require responses in the form of "Yes," "No," or "N/A." This format allows for efficient evaluations that can be easily interpreted. Additionally, the checklist features dedicated sections for comments and action requirements, which are essential for proper risk management documentation.
Notably, this form is designed to be fillable, enhancing its usability through platforms such as pdfFiller. This accessibility ensures that users can complete the checklist with ease, facilitating effective risk assessments.
Who Needs the Risk Assessment Checklist - Acquire and Implement?
The Risk Assessment Checklist is beneficial for various roles and departments within an organization, particularly those involved in systems implementation, compliance, and risk management. Key stakeholders, such as IT managers, compliance officers, and project teams, can leverage this checklist during the acquisition and implementation phases of new systems.
Specific scenarios, like new system implementations or major upgrades, make this checklist essential for ensuring that all potential risks are appropriately evaluated and documented.
How to Fill Out the Risk Assessment Checklist - Acquire and Implement Online
To complete the Risk Assessment Checklist through pdfFiller, follow these field-by-field instructions:
-
Open the checklist in pdfFiller.
-
Review each question and select "Yes," "No," or "N/A" based on the specific context.
-
Add comments or action items where necessary to detail any follow-up requirements.
-
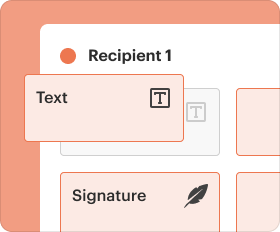
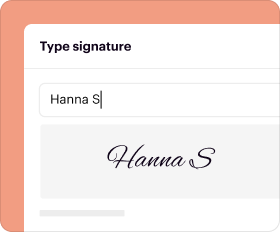
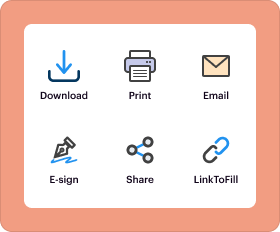
Utilize digital tools within pdfFiller to enhance the form preparation, such as auto-fill options or eSignature capabilities.
Submission Methods for the Risk Assessment Checklist - Acquire and Implement
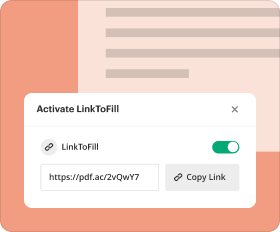
Once the checklist is completed, users can submit it through various methods. Submission options include online uploads via pdfFiller and traditional offline methods such as fax or mail. It is essential to check for any associated fees, deadlines, and required supporting documents, ensuring compliance with submission guidelines.
Understanding processing times for each submission method is also critical to meet organizational deadlines effectively.
Security and Compliance When Using the Risk Assessment Checklist
When utilizing the Risk Assessment Checklist, the security of sensitive documents and compliance with relevant regulations are paramount. pdfFiller employs robust security features, including 256-bit encryption, to protect user data during the form-filling process.
This checklist not only assists in identifying risks but also plays a critical role in helping businesses maintain compliance with established risk management standards, enhancing overall operational security and accountability.
Sample Completed Risk Assessment Checklist for Reference
To aid users in understanding the application of the Risk Assessment Checklist, an annotated sample is available for reference. This example illustrates key sections of the form and provides insight into how to properly respond to questions.
Furthermore, tips on interpreting the completed checklist can help users leverage the information for informed decision-making, ensuring alignment with organizational risk management strategies.
Why Choose pdfFiller for Your Risk Assessment Checklist Needs?
Choosing pdfFiller for your Risk Assessment Checklist needs offers several advantages, especially regarding ease of use and expansive capabilities. Users can benefits from essential functionalities, such as editing, eSigning, and form customization, which streamline the entire process.
Additionally, pdfFiller provides dedicated customer support and a range of resources to assist users in effectively managing their checklists. This comprehensive support translates into practical outcomes and significant time savings for organizations.
How to fill out the Risk Assessment Checklist
-
1.Access the Risk Assessment Checklist - Acquire and Implement on pdfFiller by visiting their website and using the search function.
-
2.Once you're on the form page, click on 'Edit' to open the fillable version of the checklist.
-
3.Familiarize yourself with each section of the form and gather all necessary information related to the new system acquisition.
-
4.Carefully read each question in the checklist, which requires responses of 'Yes', 'No', or 'N/A'.
-
5.Use pdfFiller's text fields to input your answers and ensure that you provide comments where necessary, especially in the 'Comments / Action Required' sections.
-
6.Review the completed form for any missing information or errors to ensure accuracy before finalizing.
-
7.Once satisfied with your entries, save your work regularly using the save option on pdfFiller.
-
8.Download a copy of the completed form or submit it electronically as required by your organization’s protocols.
-
9.Follow any additional instructions for submission as indicated by your organization, ensuring you comply with any associated deadlines.
Who is eligible to use the Risk Assessment Checklist?
Any individual or team involved in the acquisition and implementation of new systems within an organization is eligible to use this checklist. This typically includes project managers, compliance officers, and IT managers.
What are the key deadlines associated with this form?
The checklist should be completed before initiating the acquisition of a new system to ensure all risks are evaluated. Check with your organization for any specific deadline requirements.
How do I submit the completed checklist?
You can submit the completed Risk Assessment Checklist by downloading it from pdfFiller and then emailing it to the designated recipient or uploading it to your organization's compliance system.
What supporting documents do I need to attach?
Supporting documents can include previous risk assessment reports, project plans, or any related compliance documents necessary for evaluating the risks associated with the new system.
What common mistakes should I avoid when filling out this form?
Common mistakes include leaving questions unanswered, misinterpreting the 'Yes', 'No', or 'N/A' options, and failing to provide thorough comments in the relevant sections.
How long does it take to process this form after submission?
Processing times can vary depending on the organization's internal procedures; typically, expect a confirmation or response within a few business days after submission.
What if I have questions while filling out the form?
If you have questions while completing the Risk Assessment Checklist, consult with your project manager or compliance officer for guidance on specific areas of concern.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.