Last updated on Jan 5, 2016

Get the free Computer Usage Log
We are not affiliated with any brand or entity on this form
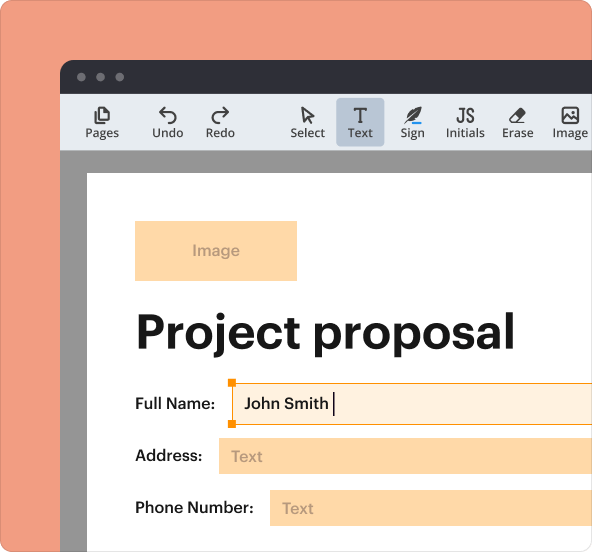
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is Computer Usage Log
The Computer Usage Log is an educational form used by schools to track student computer usage and monitor device allocation.
pdfFiller scores top ratings on review platforms




Who needs Computer Usage Log?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to Computer Usage Log
What is the Computer Usage Log?
The Computer Usage Log is an essential form used in educational settings to track the use of technology by students. Its primary function is to record pertinent information about each instance of computer use, ensuring effective classroom management. Schools and educators benefit significantly from tracking computer usage, facilitating better oversight and support for students.
This log plays a crucial role in helping teachers monitor student engagement with digital resources, thereby enhancing the learning experience. By documenting who is using what resources and why, educators can streamline the management of classroom technology more efficiently.
Purpose and Benefits of Using the Computer Usage Log
The Computer Usage Log serves multiple purposes that are vital for both students and educators alike. Primarily, it aids in monitoring individual student usage patterns, providing insights that help tailor educational strategies. Additionally, it assists in identifying potential issues concerning computer access and utilization, ensuring that all students have equitable resources.
This log also plays a role in compliance with school policies regarding computer usage, making it easier to uphold standards and guidelines within educational environments. Utilizing this log can significantly enhance classroom management and improve student accountability.
Key Features of the Computer Usage Log Form
The form includes several essential components that facilitate its usage. Key fields that must be completed include:
-
LOCATION
-
TEACHER
-
STUDENT NAME
-
DATE
-
TIME ON
-
TIME OFF
In addition to these fields, checkboxes are provided for the REASON FOR USE, allowing for clear documentation of each student's activity. The form also features a section for additional notes or comments to provide context about computer usage.
Who Needs to Use the Computer Usage Log?
The Computer Usage Log is designed for a varied audience within the educational context. Primarily, teachers and educators who manage classroom technology will find this log invaluable for tracking student interactions with computers. Additionally, school administrators can utilize the log to monitor overall computer access across the institution.
Students may also require this log for documentation of their computer usage, particularly for reports and assignments where verification of activity is necessary. This widespread utility makes the log an integral tool in schools.
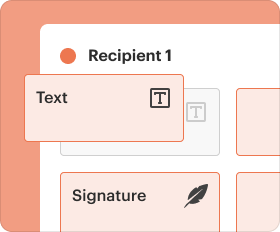
How to Fill Out the Computer Usage Log Online
Completing the Computer Usage Log online can be straightforward when following these steps:
-
Access the Computer Usage Log on pdfFiller.
-
Fill in the required fields with accurate information, including LOCATION, TEACHER, and STUDENT NAME.
-
Select the appropriate reason for use from the checkboxes provided.
-
Review your entries carefully to ensure completeness.
-
Save your progress and submit the completed log per your school's guidelines.
Common Errors and How to Avoid Them
Users often encounter pitfalls when filling out the Computer Usage Log. Common mistakes include overlooking required fields and providing unclear reasons for use. To avoid these issues, it is vital to review the completed log prior to submission to ensure that all necessary information is included.
Additionally, cross-checking the completed log with teachers or administrators can help clarify any uncertainties and ensure that the information recorded is accurate and comprehensive.
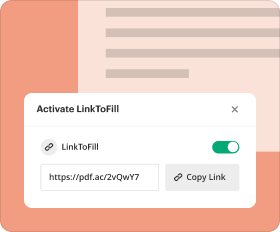
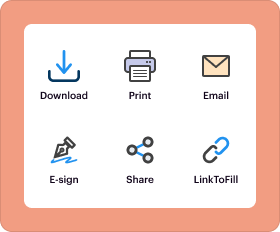
Submission Methods for the Computer Usage Log
Once the Computer Usage Log is filled out, users have several options for submission. The primary method is digital submission through pdfFiller, which allows for convenient online processing. In cases where paper submission is permitted, ensure to follow your school’s specific guidelines.
For further assistance or clarification on submission methods, users can contact school administrators, who can provide additional guidance and support.
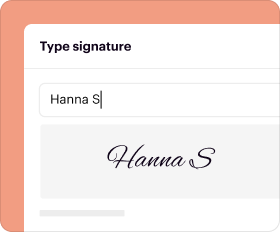
Why Choose pdfFiller for Completing the Computer Usage Log?
pdfFiller offers a user-friendly platform that simplifies the process of filling out the Computer Usage Log. With a secure interface that utilizes 256-bit encryption and adheres to HIPAA compliance, users can trust that their information is protected. Additionally, pdfFiller provides features like electronic signatures and advanced document management, making it a robust solution for educational log forms.
Next Steps After Completing the Computer Usage Log
After filling out the Computer Usage Log, it is essential to confirm receipt of the log by the appropriate school personnel. Users should be informed about how to track the school's response or any subsequent analysis of the computer usage recorded.
Maintaining accurate records of the Computer Usage Log for future reference is also advisable, ensuring that all documentation remains organized and accessible.
How to fill out the Computer Usage Log
-
1.Access pdfFiller and navigate to the search bar to find 'Computer Usage Log'.
-
2.Open the form by clicking on the result, which will load the document in the editing interface.
-
3.Before you start filling out the form, gather necessary information such as the location of the computer, teacher's name, student details, and the reason for use.
-
4.Begin by filling in the 'LOCATION' field with where the computer is located.
-
5.Next, input the 'TEACHER' name in the corresponding section.
-
6.Provide the 'STUDENT NAME' in the designated field for accurate tracking.
-
7.Enter the 'DATE' when the usage occurred, ensuring it aligns with the purpose for recording.
-
8.Log the 'TIME ON' and 'TIME OFF' to capture the duration of computer usage.
-
9.Select the appropriate options for 'REASON FOR USE' by checking the relevant boxes available in the form.
-
10.After entering all information, review the form for accuracy to ensure all fields are appropriately filled.
-
11.Finalize the form by checking for any missed entries and correcting errors before saving.
-
12.Once satisfied with the completed document, utilize the 'Save' feature to store the form, or use the 'Download' option to create a local copy.
-
13.If required, submit the form electronically or print it for manual submission to the appropriate authority.
Who is eligible to use the Computer Usage Log?
The Computer Usage Log is intended for use by students, teachers, and school administrators within educational institutions to document computer usage effectively.
Are there deadlines for submitting the Computer Usage Log?
Generally, the Computer Usage Log should be submitted promptly after each computer session. Check with your school for specific timelines.
How do I submit the completed Computer Usage Log?
Once filled out, you can submit the Computer Usage Log electronically via email or through your school's designated submission portal, or print and hand it in physically.
What information is required to fill out the Computer Usage Log?
Essential information includes the student’s name, location of the computer, teacher’s name, date of use, time used, and the reason for using the computer.
What are common mistakes to avoid when filling out this form?
Avoid leaving fields blank, especially the date and times. Ensure all sections are filled accurately to prevent confusion or processing delays.
How long does it take to process the Computer Usage Log?
Processing times can vary based on school policies, but typically logs are reviewed within a week. Follow up with your administrator for specific timing.
Can I modify the Computer Usage Log after submission?
If you need to change any information after submission, contact your administrator to discuss the possibility of making amendments to the log.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.