Last updated on Jan 12, 2016

Get the free Corporate Account Takeover Data Security Self-Assessment
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
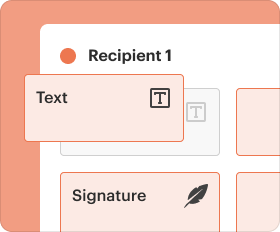
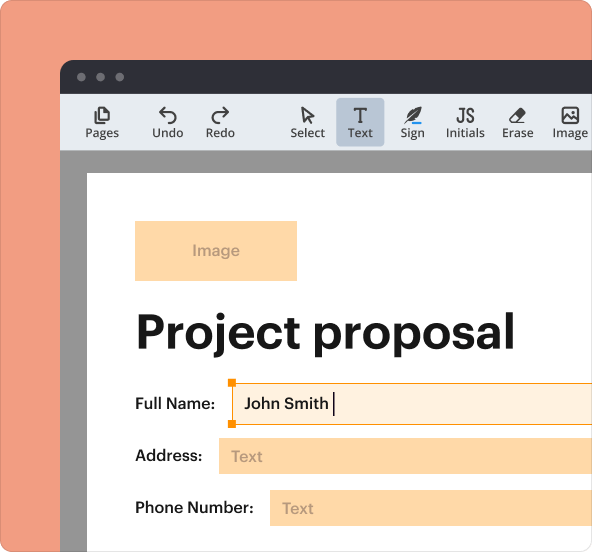
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is CATO Security Assessment
The Corporate Account Takeover Data Security Self-Assessment is a form used by businesses to evaluate their data security measures.
pdfFiller scores top ratings on review platforms




Who needs CATO Security Assessment?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to CATO Security Assessment
What is the Corporate Account Takeover Data Security Self-Assessment?
The Corporate Account Takeover Data Security Self-Assessment is an essential form for businesses to evaluate their data security measures. The purpose of this self-assessment is to thoroughly assess various types of sensitive data, including customer information, financial records, and transactional data.
Conducting this self-assessment is crucial to understanding current security protocols and identifying areas that require improvement. Companies adopting a corporate account takeover security assessment can better protect their assets and client data through improved practices.
Purpose and Benefits of the Corporate Account Takeover Data Security Self-Assessment
This self-assessment offers numerous benefits for businesses, primarily focusing on enhancing overall data security. By conducting a thorough evaluation, companies can identify vulnerabilities that may expose sensitive financial data to security breaches.
Implementing a business data protection checklist derived from this assessment can safeguard essential assets while bolstering security protocols within the organization. Furthermore, the financial data security evaluation helps in compliance with regulations and promotes a culture of security within the workplace.
Key Features of the Corporate Account Takeover Data Security Self-Assessment
-
Includes comprehensive checklists to evaluate types of data collected and methods of storage.
-
Helps in identifying vulnerabilities across various storage devices.
-
Facilitates the development of security plans tailored to address identified weaknesses.
-
Offers templates for corporate security measures to streamline the evaluation process.
-
Ensures a user-friendly experience through a practical layout.
Who Needs the Corporate Account Takeover Data Security Self-Assessment?
Target audiences for the Corporate Account Takeover Data Security Self-Assessment include businesses handling sensitive financial data, such as banks, accounting firms, and corporate offices. Understanding and implementing a corporate account takeover security assessment is essential for these organizations to remain compliant with industry standards.
Moreover, utilizing this self-assessment ensures adherence to best practices in data security, thereby mitigating risks associated with data breaches and financial fraud.
How to Fill Out the Corporate Account Takeover Data Security Self-Assessment Online
Filling out the Corporate Account Takeover Data Security Self-Assessment form can be accomplished easily through pdfFiller's platform. Here is a step-by-step guide:
-
Access the self-assessment form on pdfFiller's website.
-
Review each section before filling in the necessary details.
-
Follow the field-by-field instructions provided to ensure accuracy.
-
Gather relevant information to avoid common errors.
-
Submit the completed form using the available options on the platform.
Review and Validation Checklist for the Corporate Account Takeover Data Security Self-Assessment
After completing the self-assessment, it's essential to review the document for accuracy. A review checklist may include:
-
Confirm that all necessary information has been included.
-
Ensure consistency in the data provided across different sections.
-
Verify the completion of all checklist items as per the guidelines.
-
Avoid common errors related to data entry and context.
How to Submit the Corporate Account Takeover Data Security Self-Assessment
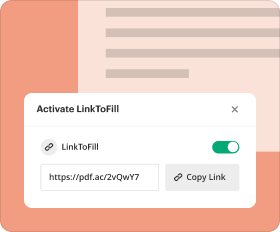
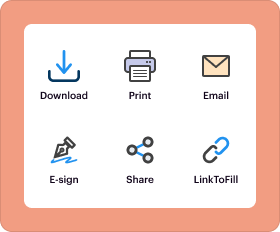
Submission methods for the Corporate Account Takeover Data Security Self-Assessment are flexible. Businesses can choose to submit electronically via pdfFiller or physically via mailing options. Factors to consider include:
-
Available electronic submission methods through pdfFiller.
-
Deadlines for submission to ensure compliance.
-
Potential fees associated with submission methods.
-
Tracking options to monitor the status of submissions.
Security and Compliance of the Corporate Account Takeover Data Security Self-Assessment
Maintaining security throughout the assessment process is paramount when handling sensitive data. pdfFiller ensures the confidentiality and integrity of data through robust encryption methods and compliance with standards such as SOC 2 Type II, HIPAA, and GDPR.
Utilizing a corporate security measures template can further assist in establishing secure practices while conducting the self-assessment.
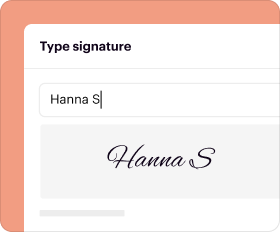
How pdfFiller Supports Your Corporate Account Takeover Data Security Self-Assessment Needs
pdfFiller provides significant support for businesses in the form-filling process, offering capabilities like eSigning and document editing. The platform is designed to simplify the completion of the data security self-assessment while ensuring security measures are in place to protect sensitive documents.
With its user-friendly interface, pdfFiller enhances the experience of users navigating the assessment form, making it efficient and trustworthy for managing corporate data security.
Next Steps for Implementing Your Corporate Account Takeover Data Security Self-Assessment Results
Once users have completed their self-assessment, taking actionable steps based on the results is crucial for reinforcing security measures. Resources or tools available through pdfFiller can assist users in implementing changes effectively, thus enhancing overall data security protocols.
By leveraging the features of pdfFiller, users can ensure their assessment process is efficient and secure, solidifying their commitment to data protection.
How to fill out the CATO Security Assessment
-
1.To access the Corporate Account Takeover Data Security Self-Assessment form on pdfFiller, visit the pdfFiller website and log in to your account or sign up for a new account if you don't have one.
-
2.Use the search bar to locate the form by typing in its name. Once you've found it, click on the form to open it in the pdfFiller interface.
-
3.Take some time to gather all necessary information before filling out the form, including details about the types of data your business collects, methods of storage, and the locations of both physical and electronic storage.
-
4.Navigate through the form, filling in the checkboxes and fields provided. Click on each section to input your data, ensuring that you complete all required fields for an accurate assessment.
-
5.As you fill out the form, be sure to assess the security controls in place for different devices and consider any vulnerabilities that may arise.
-
6.After you have completed all sections, review the form carefully to ensure all information is accurate and complete. Use the pdfFiller 'Review' feature to go through the filled form.
-
7.Once you are satisfied with the content of your assessment, save your progress. You have options to either download the form as a PDF or submit it directly through pdfFiller, depending on your needs.
Who should fill out the Corporate Account Takeover Data Security Self-Assessment?
This form is essential for business owners, IT managers, compliance officers, and anyone responsible for data security within an organization. It assesses current security measures against potential vulnerabilities.
Are there any deadlines for submitting this form?
While there may not be a specific deadline for this assessment form, it is recommended to complete it regularly or when new data security measures are implemented to ensure up-to-date evaluations.
How do I submit the completed form?
After completing the form on pdfFiller, you can submit it directly using the platform's submission features or download it and send it via email or your chosen communication method.
What supporting documents are needed to complete this assessment?
Typically, you should have information related to your data storage methods, security protocols, and an inventory of sensitive data. Having recent security audit reports can also be helpful.
What common mistakes should I avoid while filling out this form?
Common mistakes include skipping required fields, providing outdated information, or failing to review your answers. Make sure to validate every detail for accuracy.
How long will it take to process the assessment once submitted?
Processing times may vary, but as this form is generally self-assessed, review and reflection can take a few hours to a few days, depending on the complexity of your data security measures.
Can I edit the form after it’s been saved?
Yes, on pdfFiller, you can reopen and edit the saved form at any time. Just ensure that you save changes to avoid losing any new information you enter.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.