Cloud Security Trust Signatory For Free




Join the world’s largest companies
How to Send a PDF for eSignature









Why choose pdfFiller for eSignature and PDF editing?

Cross-platform solution

Unlimited document storage

Widely recognized ease of use

Reusable templates & forms library
The benefits of electronic signatures

Efficiency

Accessibility

Cost savings

Security

Legality

Sustainability
Enjoy straightforward eSignature workflows without compromising data security

GDPR compliance

SOC 2 Type II Certified

PCI DSS certification

HIPAA compliance

CCPA compliance
Cloud Security Trust Signatory Feature
The Cloud Security Trust Signatory feature offers a straightforward way to enhance your trust in cloud service providers. It ensures that your data remains secure and compliant with industry standards. You gain confidence in your cloud environment, allowing you to focus on your core business functions.
Key Features
Potential Use Cases and Benefits
By implementing the Cloud Security Trust Signatory feature, you effectively address concerns related to data security and compliance. This feature provides you with the tools to mitigate risks, ensuring your cloud environment remains secure and reliable. You can rest easier, knowing you have taken essential steps to protect your business and its data.
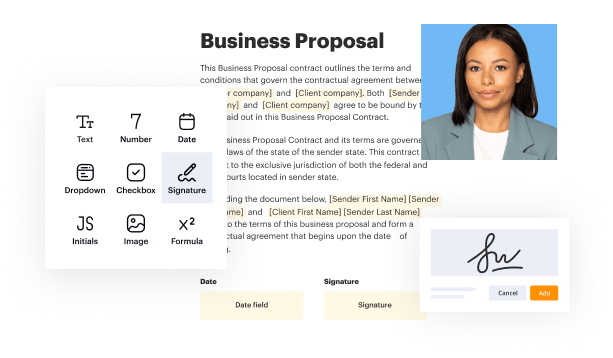
Add a legally-binding Cloud Security Trust Signatory with no hassle
pdfFiller enables you to deal with Cloud Security Trust Signatory like a pro. No matter what system or device you run our solution on, you'll enjoy an intuitive and stress-free method of executing documents.
The whole pexecution flow is carefully safeguarded: from importing a file to storing it.
Here's the best way to create Cloud Security Trust Signatory with pdfFiller:
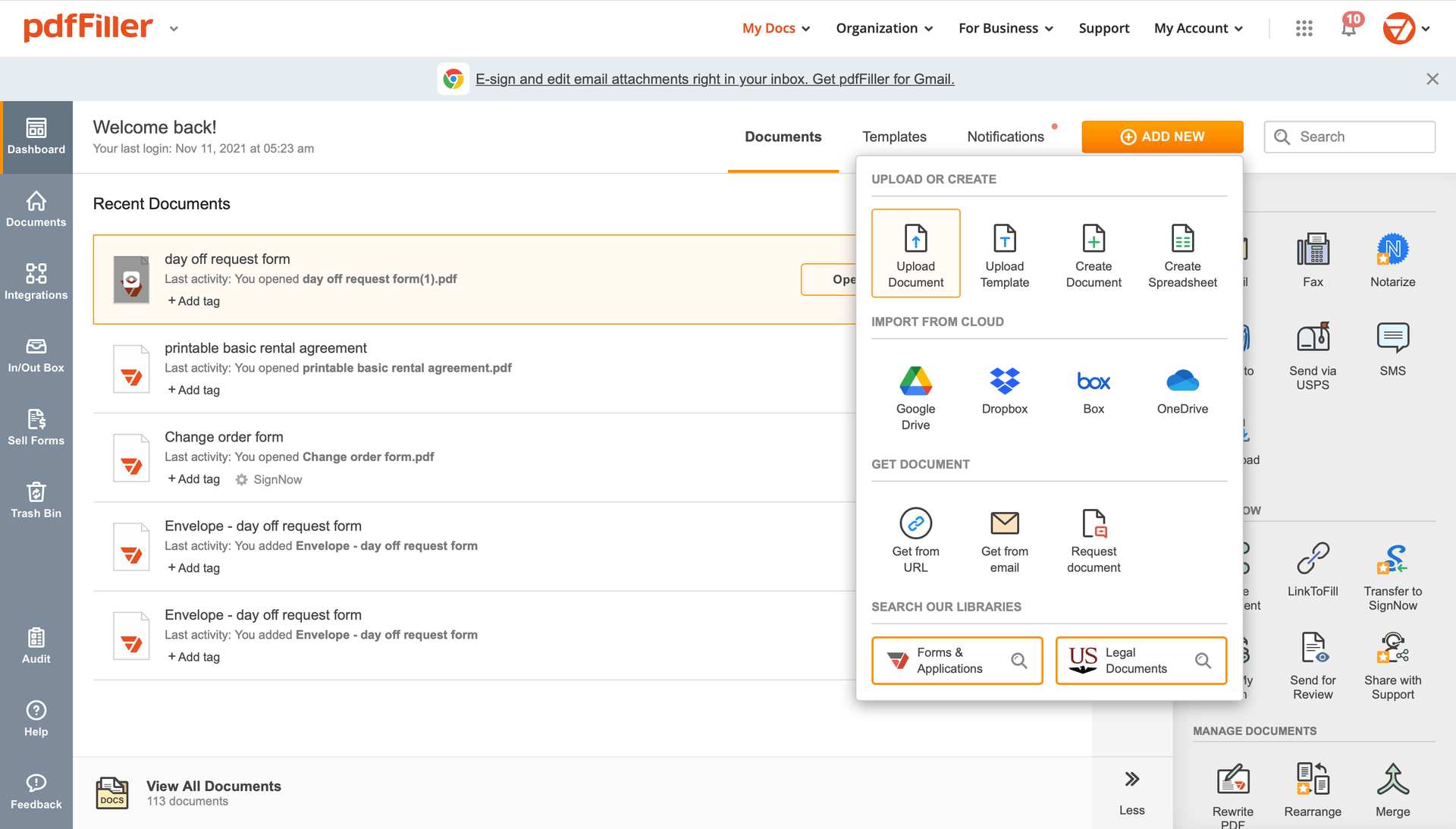
Select any readily available way to add a PDF file for signing.
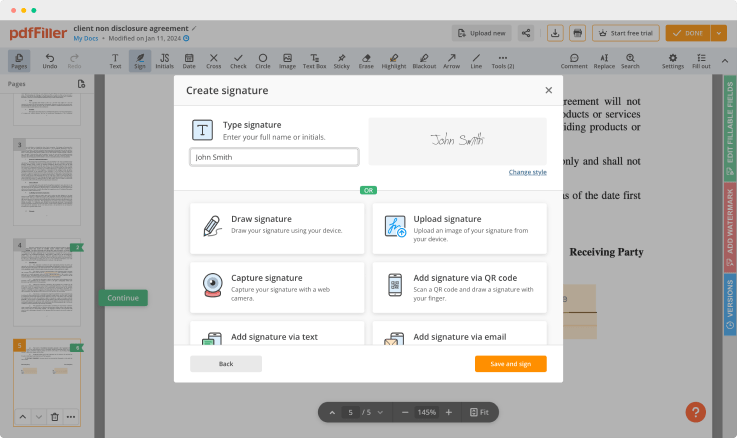
Use the toolbar at the top of the interface and choose the Sign option.
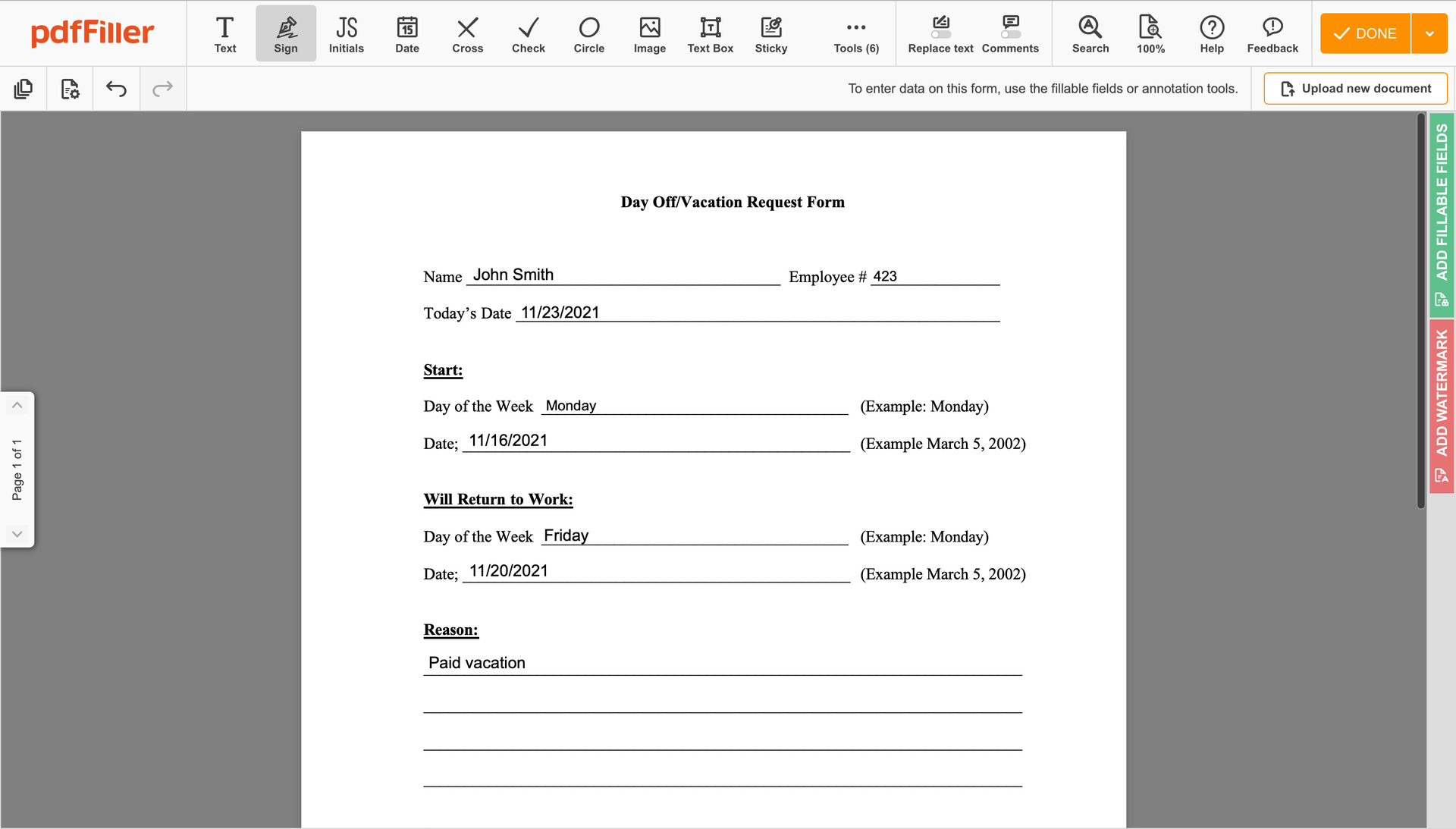
You can mouse-draw your signature, type it or add a photo of it - our solution will digitize it automatically. Once your signature is created, click Save and sign.
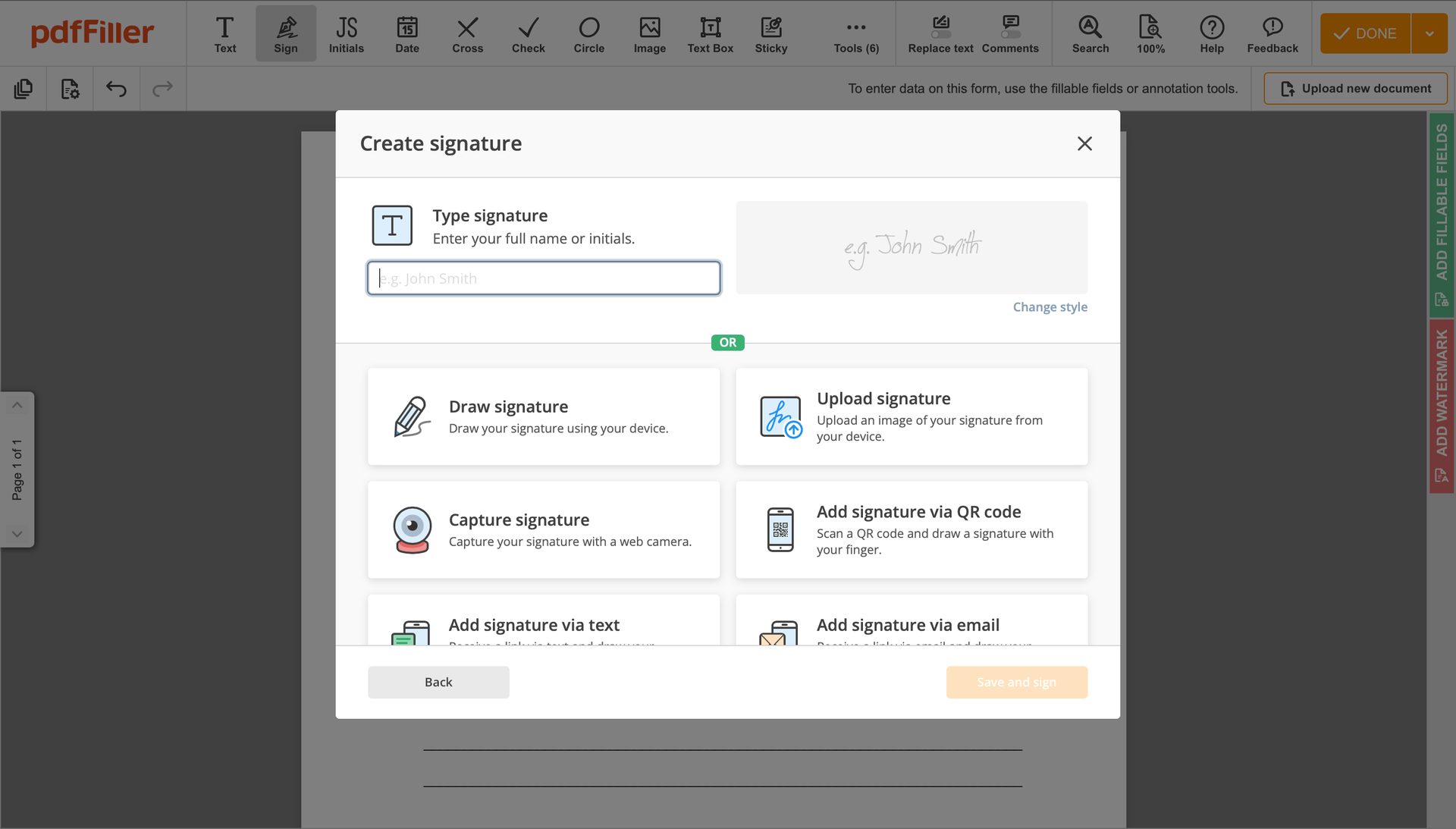
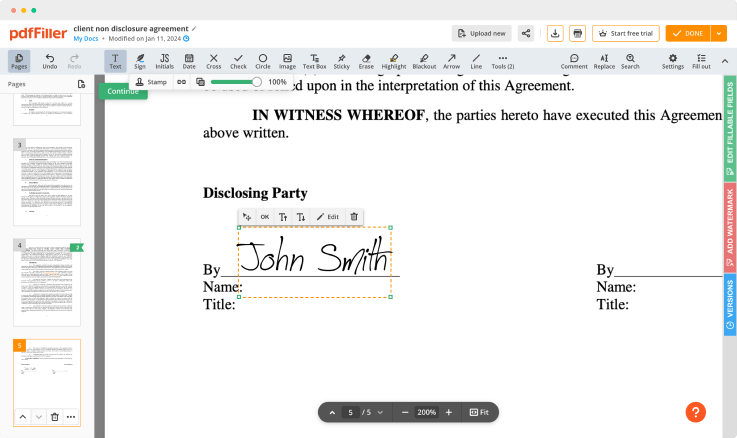
Click on the document place where you want to put an Cloud Security Trust Signatory. You can drag the newly created signature anywhere on the page you want or change its configurations. Click OK to save the changes.
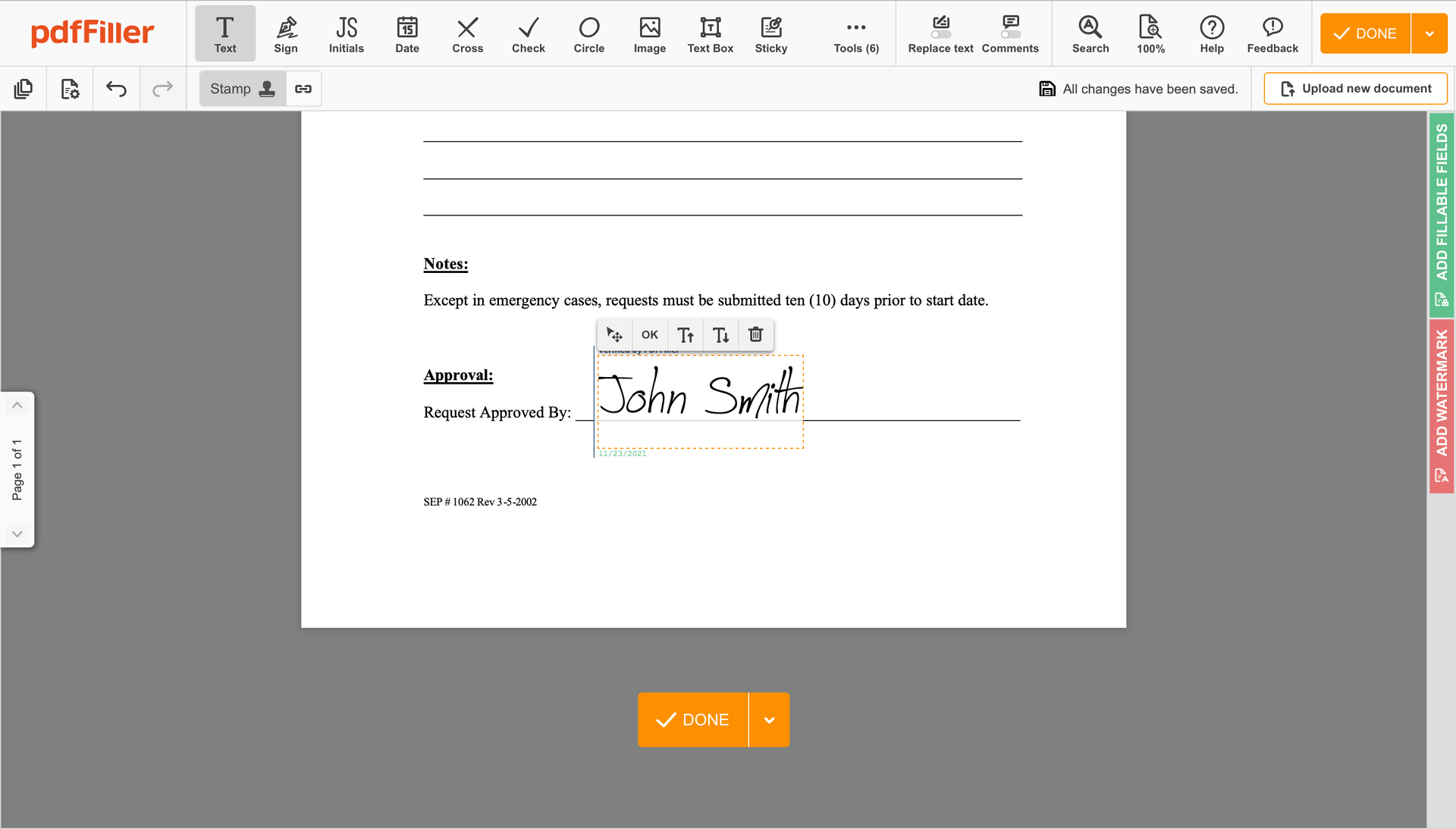
As soon as your form is all set, hit the DONE button in the top right area.
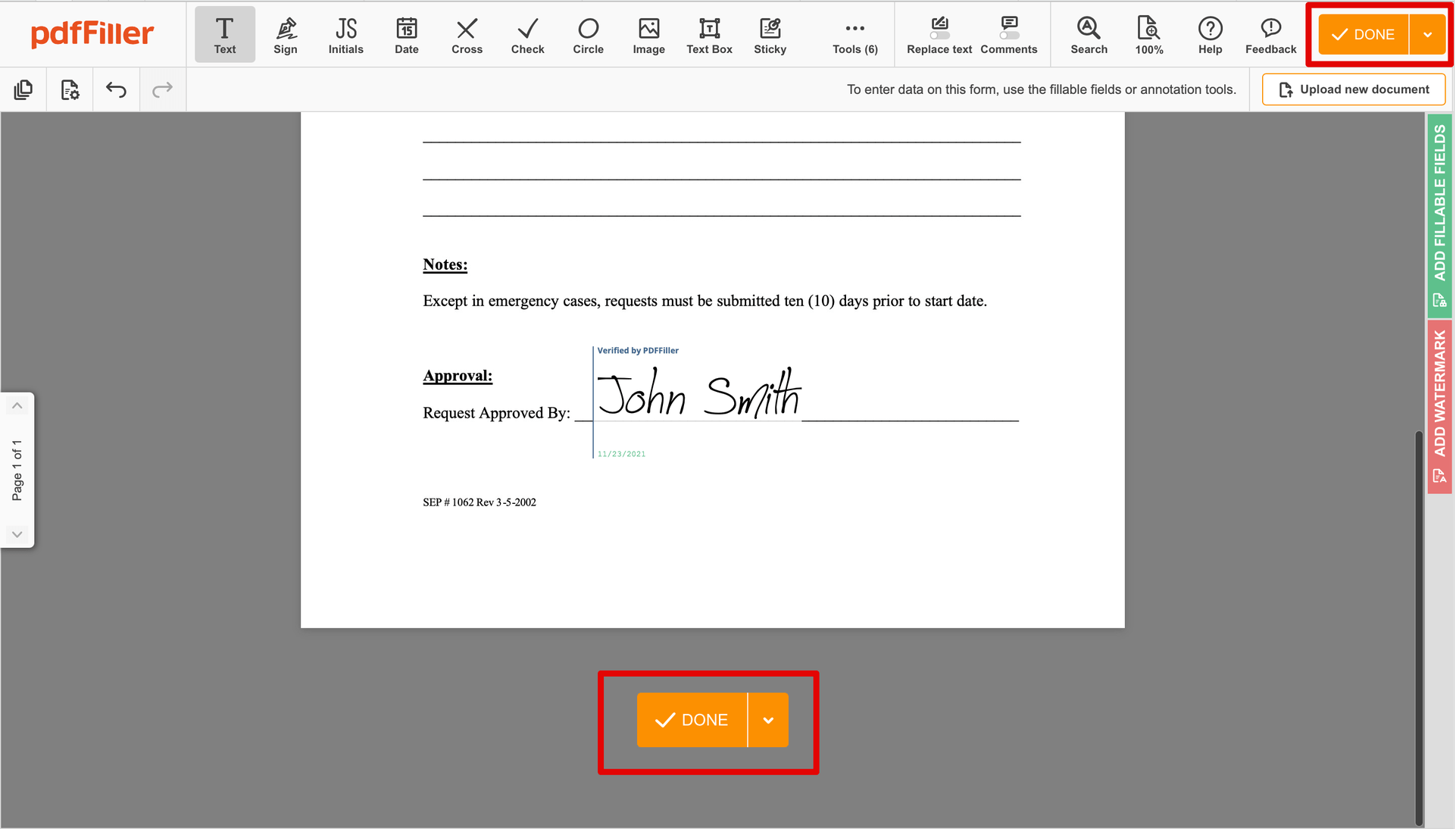
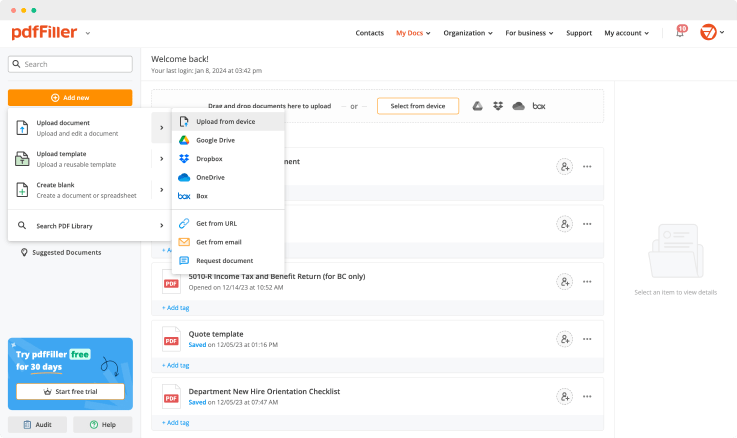
Once you're through with certifying your paperwork, you will be taken back to the Dashboard.
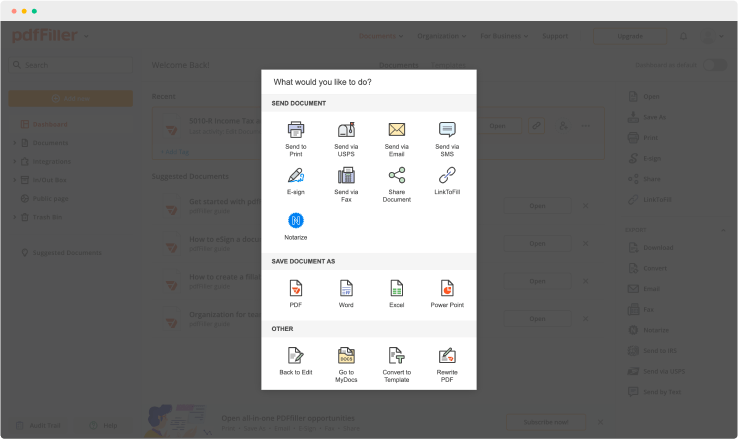
Utilize the Dashboard settings to get the completed form, send it for further review, or print it out.
Still using numerous programs to create and modify your documents? Try this solution instead. Use our document management tool for the fast and efficient process. Create forms, contracts, make document template sand many more useful features, within your browser. Plus, you can use Cloud Security Trust Signatory and add more features like orders signing, alerts, attachment and payment requests, easier than ever. Pay as for a lightweight basic app, get the features as of a pro document management tools. The key is flexibility, usability and customer satisfaction.
How to edit a PDF document using the pdfFiller editor:
For pdfFiller’s FAQs
Ready to try pdfFiller's? Cloud Security Trust Signatory