Document Editor - Tls Online For Free
Drop document here to upload
Up to 100 MB for PDF and up to 25 MB for DOC, DOCX, RTF, PPT, PPTX, JPEG, PNG, JFIF, XLS, XLSX or TXT
Note: Integration described on this webpage may temporarily not be available.
0
Forms filled
0
Forms signed
0
Forms sent
Discover the simplicity of processing PDFs online
Upload your document in seconds
Fill out, edit, or eSign your PDF hassle-free

Download, export, or share your edited file instantly
Top-rated PDF software recognized for its ease of use, powerful features, and impeccable support






Every PDF tool you need to get documents done paper-free
Create & edit PDFs
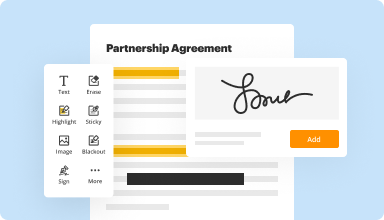
Generate new PDFs from scratch or transform existing documents into reusable templates. Type anywhere on a PDF, rewrite original PDF content, insert images or graphics, redact sensitive details, and highlight important information using an intuitive online editor.
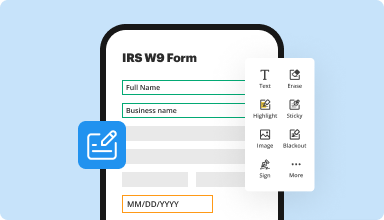
Fill out & sign PDF forms
Say goodbye to error-prone manual hassles. Complete any PDF document electronically – even while on the go. Pre-fill multiple PDFs simultaneously or extract responses from completed forms with ease.
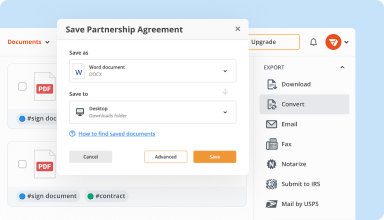
Organize & convert PDFs
Add, remove, or rearrange pages inside your PDFs in seconds. Create new documents by merging or splitting PDFs. Instantly convert edited files to various formats when you download or export them.
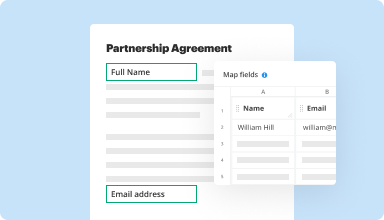
Collect data and approvals
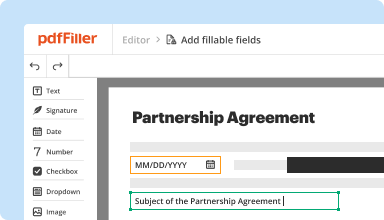
Transform static documents into interactive fillable forms by dragging and dropping various types of fillable fields on your PDFs. Publish these forms on websites or share them via a direct link to capture data, collect signatures, and request payments.
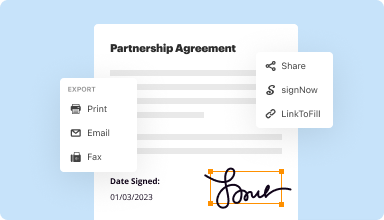
Export documents with ease
Share, email, print, fax, or download edited documents in just a few clicks. Quickly export and import documents from popular cloud storage services like Google Drive, Box, and Dropbox.
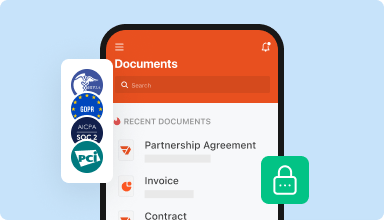
Store documents safely
Store an unlimited number of documents and templates securely in the cloud and access them from any location or device. Add an extra level of protection to documents by locking them with a password, placing them in encrypted folders, or requesting user authentication.
Customer trust by the numbers
64M+
users worldwide
4.6/5
average user rating
4M
PDFs edited per month
9 min
average to create and edit a PDF
Join 64+ million people using paperless workflows to drive productivity and cut costs
Why choose our PDF solution?
Cloud-native PDF editor
Access powerful PDF tools, as well as your documents and templates, from anywhere. No installation needed.
Top-rated for ease of use
Create, edit, and fill out PDF documents faster with an intuitive UI that only takes minutes to master.
Industry-leading customer service
Enjoy peace of mind with an award-winning customer support team always within reach.
What our customers say about pdfFiller
See for yourself by reading reviews on the most popular resources:
I love the convenience of sending a fax from anywhere I have a wifi connection. The ease of filling PDF documents is great compared with other programs.
2015-10-07
Initial problem was apparently that I had failed to save the (almost) completed form that I had made, and when I went bace to it, only the original blank form was available. I see the error of my way. Quite interested in learning lots more about program and the ways it couod be useful to me.
2018-07-09
Everything was easy to mange till I got to printing & I get an error message. I could not print from your Site. I used my computer system to print.printing
2019-01-12
overall my experience with PDF filler has been great. I have been able to generate numerous forms and have been able to save and email them as needed.
2019-04-15
I love it for the most part. Just wish I could send a document to a person without knowing their email (ex. directly to their Facebook account) with the ability to view and sign not edit the document. Other than that, it's been great!
2019-09-25
The staff service is impeccable
The staff service is impeccable. The online platform works like magic. I am just happy with the service I received, and how good the quality of their online platform is. 20 stars for excellent customer service and 20 stars for excellent platform
2019-10-04
PdfFiller has been an extremely convenient tool and service for me and my business. I basically have admin on demand without all the extra machinery of fax, printers, Scanners, etc. I can do it all from my device. I am happy to have found this service.
2024-04-05
The product is very good and it works very nice and...
The product is very good and it works very nice and it's very easy to comprehend how to use it, but the way you have the purchase setup I feel is very misleading I signed up for the month the month payment and you took a full year out of my account I did not like that that is why I would never recommend your product to anyone want to use because you can really mess up a person and you could be taking money that they could not have to be taken at the time. You need the fix your payment process area or you will lose other customers like myself because I did report it to the Better Business Bureau cuz I did not appreciate that.
2020-04-27
Quick sign up, User friendly for beginners and love the functionality!!
What made my experience great is that it was simple and easy to use, I had only used docusign once before and decided to try pdfFiller for some court papers that needed electronically signed immediately. It is super user friendly. Great pricing after the 30 day free trial. But my favorite part is the set up and how many different things you can easily do!!!!
2025-05-10
Document Editor - TLS Feature: Secure Your Documents Effectively
The Document Editor with TLS (Transport Layer Security) offers a reliable way to keep your documents safe during editing and sharing. This feature ensures that your information remains private and protected from unauthorized access. With the increasing need for data security in your daily workflow, using this advanced technology is essential.
Key Features
Secure data transmission using robust encryption methods
Real-time collaboration without compromising security
User-friendly interface that simplifies document editing
Compatibility with various document formats
Automatic updates to keep your systems secure
Use Cases and Benefits
Ideal for professionals needing to share sensitive information
Supports teams working remotely on confidential projects
Enhances compliance with data protection regulations
Reduces the risk of data breaches during collaboration
Facilitates smooth communication without worrying about security
In conclusion, the Document Editor with TLS feature helps you solve the problem of document security. By integrating this tool into your workflow, you can confidently collaborate with others while ensuring that your data remains safe and sound. Embrace a secure editing experience that empowers you to focus on what truly matters—creating and sharing your best work.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What if I have more questions?
Contact Support
What is TLS record protocol?
The Transport Layer Security (TLS) Record protocol secures application data using the keys created during the Handshake. The Record Protocol is responsible for securing application data and verifying its integrity and origin.
What services are provided by the TLS Record Protocol?
encryption, Authentication, and Integrity. The TLS protocol is designed to provide three essential services to all applications running above it: encryption, authentication, and data integrity.
What steps are involved in the TLS record protocol transmission?
The basic operation of the TLS Record Protocol is as follows: Read messages for transmit. Fragment messages into manageable chunks of data. Compress the data, if compression is required and enabled.
What is the use of TLS protocol?
TLS is a cryptographic protocol that provides end-to-end communications' security over networks and is widely used for internet communications and online transactions. It is an IETF standard intended to prevent eavesdropping, tampering and message forgery.
How is a TLS session established?
A TLS handshake is the process that kicks off a communication session that uses TLS encryption. During a TLS handshake, the two communicating sides exchange messages to acknowledge each other, verify each other, establish the encryption algorithms they will use, and agree on session keys.
What is TLS and how it works?
TLS is a cryptographic protocol that provides end-to-end security of data sent between applications over the Internet. It should be noted that TLS does not secure data on end systems. It simply ensures the secure delivery of data over the Internet, avoiding possible eavesdropping and/or alteration of the content.
How does TLS work step by step?
Client is ready: The client sends a “finished” message that is encrypted with a session key. Server is ready: The server sends a “finished” message encrypted with a session key. Secure symmetric encryption achieved: The handshake is completed, and communication continues using the session keys.
What is TLS used for?
TLS is a cryptographic protocol that provides end-to-end communications' security over networks and is widely used for internet communications and online transactions. It is an IETF standard intended to prevent eavesdropping, tampering and message forgery.
Video Review on How to Document Editor - Tls Online
#1 usability according to G2
Try the PDF solution that respects your time.






