Safeguard Compulsory Field Log
Note: Integration described on this webpage may temporarily not be available.
0
Forms filled
0
Forms signed
0
Forms sent
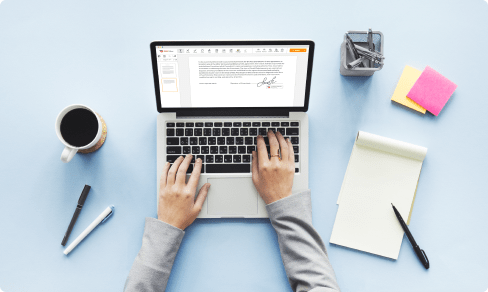
Upload your document to the PDF editor
Type anywhere or sign your form

Print, email, fax, or export

Try it right now! Edit pdf
Users trust to manage documents on pdfFiller platform
All-in-one PDF software
A single pill for all your PDF headaches. Edit, fill out, eSign, and share – on any device.
What our customers say about pdfFiller
See for yourself by reading reviews on the most popular resources:
Lisa C
2016-05-07
Great concept - I can finally share my documents with people. Although it would be good to be able to switch things off like the steps clip note as on some of my pages there are 300+ fields to fill in!

Sharon M
2016-05-19
I need to know more about how to use PDFFiller before I can give it a 5 star rating. Please let me know when the next webinar is scheduled so that I can attend.


Get a powerful PDF editor for your Mac or Windows PC
Install the desktop app to quickly edit PDFs, create fillable forms, and securely store your documents in the cloud.

Edit and manage PDFs from anywhere using your iOS or Android device
Install our mobile app and edit PDFs using an award-winning toolkit wherever you go.

Get a PDF editor in your Google Chrome browser
Install the pdfFiller extension for Google Chrome to fill out and edit PDFs straight from search results.
pdfFiller scores top ratings in multiple categories on G2
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How long should you keep security logs?
While most logs are covered by some form of regulation these days and should be kept as long as the requirements call for, any that are not should be kept for a minimum period of one year, in case they are needed for an investigation.
How often should security logs be reviewed?
Security/Compliance Review To be precise under the PCI DSS Requirement 10, which is dedicated to logging and log management, logs for all system components must be reviewed at least daily.
Should audit logs be maintained?
Long term maintenance of audit logs can prove difficult for many organizations because the logs can occupy extensive storage space that may not be readily available. However, if possible, maintain the audit trail for the life of the records.
Why do we review logs?
From a security point of view, the purpose of a log is to act as a red flag when something bad is happening. Reviewing logs regularly could help identify malicious attacks on your system. Often this is done using real-time reporting systems that alert you via email or text when something suspicious is detected.
How do you protect audit logs?
Ensure Integrity Digital records need to maintain integrity from tampering. External threats to your environment can be mitigated by firewalls, but you also need to make sure that internal actors cannot change the logs. Two ways to protect the data integrity are using complete replicas or read-only files.
What are the main reasons for keeping old log files?
Log files can be very useful resources for security incident investigations. They can also be essential for prosecution of criminal activity. For these reasons log files should be periodically backed up to separate media, and precautions need to be taken to prevent tampering with the log files.
How long should logs be kept?
While most logs are covered by some form of regulation these days and should be kept as long as the requirements call for, any that are not should be kept for a minimum period of one year, in case they are needed for an investigation.
How do you clear a log file?
Launch Event Viewer. Go to the event log and hit Action. Choose Clear Log and then hit Clear.
eSignature workflows made easy
Sign, send for signature, and track documents in real-time with signNow.