Get the free SAMPLE SECURITY REQUIREMENT DOCUMENTS - Social Security - ssa
Show details
Understanding SSI Home Page / Understanding Supplemental Security Income Documents You May Need When You Apply ... Unearned Income any records you have (for example, award letters, bank statements,
pdfFiller is not affiliated with any government organization
Get, Create, Make and Sign sample security requirement documents

Edit your sample security requirement documents form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your sample security requirement documents form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing sample security requirement documents online
To use our professional PDF editor, follow these steps:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit sample security requirement documents. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
The use of pdfFiller makes dealing with documents straightforward.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out sample security requirement documents

01
First, gather all necessary information about the project or system for which the security requirement documents are being prepared. This includes understanding the purpose, goals, and scope of the project, as well as any existing security policies or guidelines that need to be followed.
02
Begin by creating a clear and concise introduction section in the document. This should provide an overview of the document, its purpose, and its intended audience. It should also outline any applicable regulations or standards that need to be adhered to.
03
Identify the specific security requirements that need to be addressed. This could include items such as access control, data protection, encryption, network security, physical security, and incident response. Be sure to align these requirements with the goals and objectives of the project.
04
For each security requirement, provide a detailed description and any necessary background information. This helps to ensure that everyone understands why the requirement is important and how it relates to the overall security of the project.
05
Clearly define any security controls or measures that need to be implemented in order to meet each requirement. This could involve documenting technical solutions, processes, or policies that need to be put in place. It is important to be as specific and detailed as possible to ensure a comprehensive security posture.
06
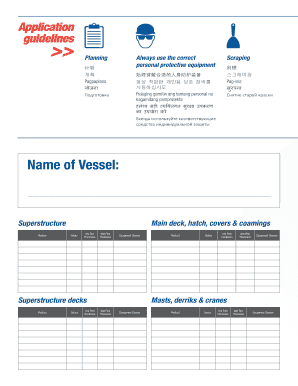
Include any relevant diagrams, flowcharts, or visuals to assist in understanding the security requirements and controls. This can help to convey complex ideas or relationships between different components of the system.
07
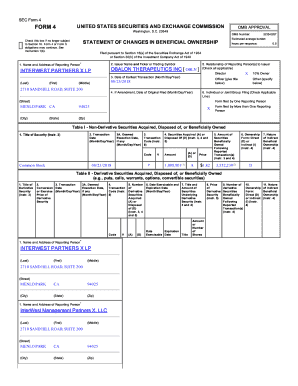
Don't forget to include any legal or compliance considerations that may impact the project. This could involve regulations such as GDPR, HIPAA, or PCI DSS, as well as any contractual obligations with clients or vendors.
08
Finally, review and validate the completed security requirement documents with key stakeholders. This ensures that everyone is in agreement with the proposed requirements, controls, and any associated risks.
Who needs sample security requirement documents?
01
Organizations or businesses that are developing new software or systems and want to ensure their security from the start.
02
Companies that are updating or enhancing existing systems and need to identify and address any security gaps or vulnerabilities.
03
Consultants or security professionals who need a template or reference guide to create security requirement documents for their clients.
04
Companies that are subject to specific industry regulations or standards and need to demonstrate compliance by documenting their security requirements.
In summary, filling out sample security requirement documents requires gathering project information, providing an introduction, identifying specific requirements, describing them in detail, defining necessary security controls, including visuals if needed, considering legal and compliance aspects, and validating the documents with stakeholders. These documents are needed by organizations, consultants, and companies subject to regulations to ensure proper security measures are met.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is sample security requirement documents?
Sample security requirement documents are documents that outline the specific security measures and protocols that must be followed to protect sensitive information and data.
Who is required to file sample security requirement documents?
Any organization or entity that handles sensitive information or data is required to file sample security requirement documents.
How to fill out sample security requirement documents?
Sample security requirement documents should be filled out by detailing the specific security procedures, protocols, and measures that will be implemented to protect sensitive information.
What is the purpose of sample security requirement documents?
The purpose of sample security requirement documents is to ensure that sensitive information is adequately protected from potential security breaches.
What information must be reported on sample security requirement documents?
Sample security requirement documents should include details on access controls, encryption methods, network security, incident response procedures, and compliance measures.
How do I make edits in sample security requirement documents without leaving Chrome?
Adding the pdfFiller Google Chrome Extension to your web browser will allow you to start editing sample security requirement documents and other documents right away when you search for them on a Google page. People who use Chrome can use the service to make changes to their files while they are on the Chrome browser. pdfFiller lets you make fillable documents and make changes to existing PDFs from any internet-connected device.
How can I fill out sample security requirement documents on an iOS device?
Make sure you get and install the pdfFiller iOS app. Next, open the app and log in or set up an account to use all of the solution's editing tools. If you want to open your sample security requirement documents, you can upload it from your device or cloud storage, or you can type the document's URL into the box on the right. After you fill in all of the required fields in the document and eSign it, if that is required, you can save or share it with other people.
How do I complete sample security requirement documents on an Android device?
Use the pdfFiller mobile app to complete your sample security requirement documents on an Android device. The application makes it possible to perform all needed document management manipulations, like adding, editing, and removing text, signing, annotating, and more. All you need is your smartphone and an internet connection.
Fill out your sample security requirement documents online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Sample Security Requirement Documents is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.