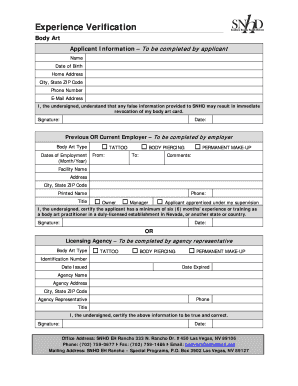
Get the free Penetration Testing Guidance. Penetration Testing - pcisecuritystandards
Show details
Standard: PCI Data Security Standard (PCI DSS) Version: 1.0 Date: March 2015 Author: Penetration Test Guidance Special Interest Group PCI Security Standards Council Information Supplement: Penetration
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign penetration testing guidance penetration
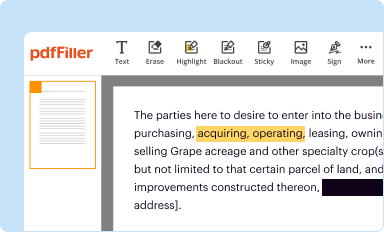
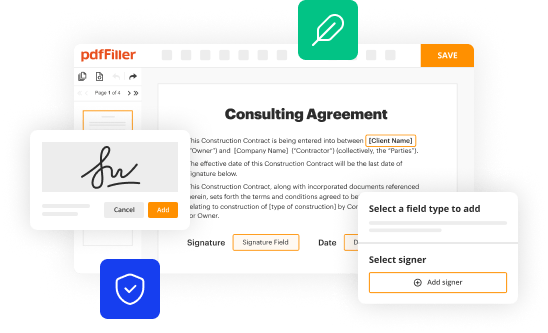
Edit your penetration testing guidance penetration form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
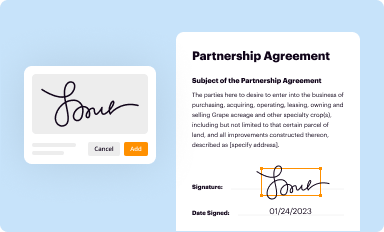
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
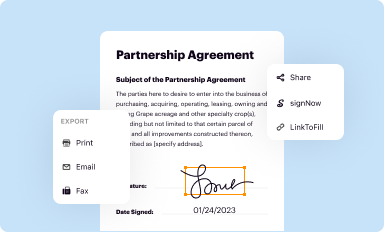
Share your form instantly
Email, fax, or share your penetration testing guidance penetration form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit penetration testing guidance penetration online
To use our professional PDF editor, follow these steps:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit penetration testing guidance penetration. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
Dealing with documents is always simple with pdfFiller. Try it right now
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out penetration testing guidance penetration
How to fill out penetration testing guidance penetration?
01
Read the instructions carefully to understand the purpose and objectives of the penetration testing guidance penetration.
02
Identify the scope of the penetration testing and determine the systems or applications that need to be tested.
03
Gather all the necessary information and documentation related to the systems or applications to be tested.
04
Identify and document any specific objectives, goals, or constraints for the penetration testing.
05
Determine the methodology to be used for the penetration testing, whether it's black-box, white-box, or gray-box testing.
06
Create a detailed plan and schedule for the penetration testing activities, including the timeline and resources required.
07
Conduct a thorough risk assessment to identify potential vulnerabilities and weaknesses in the systems or applications.
08
Perform the penetration testing activities according to the plan, including vulnerability scanning, exploiting vulnerabilities, and attempting to gain unauthorized access.
09
Document all the findings, including vulnerabilities discovered, exploited, or successfully mitigated.
10
Provide recommendations and remediation steps to address the identified vulnerabilities and improve the security posture of the systems or applications.
Who needs penetration testing guidance penetration?
01
Organizations that handle sensitive or confidential data, such as financial institutions, healthcare providers, or government agencies, need penetration testing guidance penetration to ensure the security of their systems and protect sensitive information.
02
Companies that develop software or web applications need penetration testing guidance penetration to identify vulnerabilities and weaknesses in their products before they are released to the market, reducing the risk of breaches or attacks.
03
Organizations that have experienced security incidents in the past or have concerns about their current security measures can benefit from penetration testing guidance penetration to assess the effectiveness of their existing controls and identify areas for improvement.
04
Compliance requirements, such as those imposed by regulatory bodies or industry standards, may mandate penetration testing for certain organizations or sectors. These organizations need penetration testing guidance penetration to meet the compliance requirements and demonstrate their commitment to security.
05
Organizations that outsource their IT infrastructure or services to third-party providers need penetration testing guidance penetration to assess the security of the outsourced systems and ensure that they are adequately protected.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I edit penetration testing guidance penetration in Chrome?
penetration testing guidance penetration can be edited, filled out, and signed with the pdfFiller Google Chrome Extension. You can open the editor right from a Google search page with just one click. Fillable documents can be done on any web-connected device without leaving Chrome.
How can I edit penetration testing guidance penetration on a smartphone?
You may do so effortlessly with pdfFiller's iOS and Android apps, which are available in the Apple Store and Google Play Store, respectively. You may also obtain the program from our website: https://edit-pdf-ios-android.pdffiller.com/. Open the application, sign in, and begin editing penetration testing guidance penetration right away.
How do I complete penetration testing guidance penetration on an iOS device?
Get and install the pdfFiller application for iOS. Next, open the app and log in or create an account to get access to all of the solution’s editing features. To open your penetration testing guidance penetration, upload it from your device or cloud storage, or enter the document URL. After you complete all of the required fields within the document and eSign it (if that is needed), you can save it or share it with others.
What is penetration testing guidance penetration?
Penetration testing guidance penetration refers to the process of assessing the security of a computer system or network by simulating an attack.
Who is required to file penetration testing guidance penetration?
Organizations that handle sensitive data or have critical infrastructure are typically required to conduct penetration testing and file the guidance penetration report.
How to fill out penetration testing guidance penetration?
Penetration testing guidance penetration is typically filled out by trained cybersecurity professionals who conduct the penetration testing and report their findings.
What is the purpose of penetration testing guidance penetration?
The purpose of penetration testing guidance penetration is to identify vulnerabilities in a system or network before they can be exploited by malicious actors.
What information must be reported on penetration testing guidance penetration?
The report should include details of the testing methodology, findings of vulnerabilities, and recommendations for improving security.
Fill out your penetration testing guidance penetration online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Penetration Testing Guidance Penetration is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.