Get the free Hacking (and securing)
Show details
HER CHAUCER CONSULTANTSCabinet de Consultants en Security Informative deputy 1989
Socialist SUR Unix, Windows, TCP/IP et InternetHacking (and securing)
Boss Arnaud Dubourguaisrenaud.dubourguais@hsc.frHerv
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign hacking and securing
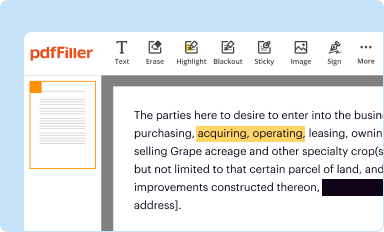
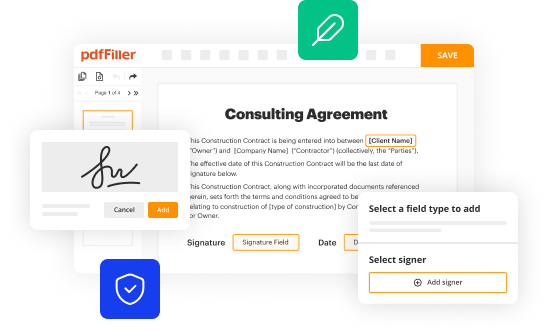
Edit your hacking and securing form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
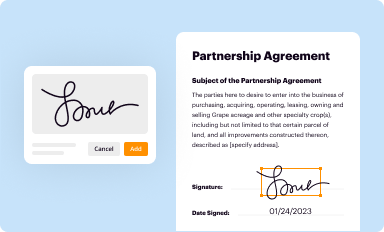
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
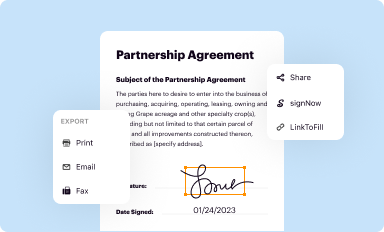
Share your form instantly
Email, fax, or share your hacking and securing form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit hacking and securing online
To use our professional PDF editor, follow these steps:
1
Create an account. Begin by choosing Start Free Trial and, if you are a new user, establish a profile.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit hacking and securing. Rearrange and rotate pages, insert new and alter existing texts, add new objects, and take advantage of other helpful tools. Click Done to apply changes and return to your Dashboard. Go to the Documents tab to access merging, splitting, locking, or unlocking functions.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out hacking and securing
How to Fill Out Hacking and Securing:
01
Research: Start by familiarizing yourself with hacking techniques and cybersecurity concepts. Learn about common vulnerabilities and how to identify and exploit them. Gain knowledge about securing systems and protecting against cyber threats.
02
Training: Participate in hacking and cybersecurity courses, workshops, or online tutorials. These resources can provide hands-on experience and practical skills necessary for understanding and effectively addressing vulnerabilities in digital systems.
03
Practice: Apply the knowledge and skills gained from training exercises in real-world scenarios. Practice ethical hacking within legal frameworks, such as through participating in bug bounty programs or conducting vulnerability assessments for organizations.
04
Tools: Acquire and become proficient in using various hacking tools. Familiarize yourself with popular software and hardware utilized for hacking and securing purposes, such as network scanning tools, vulnerability assessment frameworks, and intrusion detection systems.
05
Continuous Learning: Stay updated with emerging hacking techniques, technologies, and cybersecurity trends. Subscribe to relevant blogs, forums, and podcasts to stay informed about the latest developments in hacking and securing practices.
06
Certification: Consider obtaining recognized certifications in cybersecurity, such as Certified Ethical Hacker (CEH), Certified Information Systems Security Professional (CISSP), or Offensive Security Certified Professional (OSCP). These certifications validate your knowledge and expertise in hacking and securing.
07
Collaboration: Engage with the hacking and cybersecurity community. Attend conferences, join online forums, and participate in networking events to connect with like-minded professionals, share knowledge, and collaborate on projects related to hacking and securing.
Who Needs Hacking and Securing:
01
Individuals: Anyone who wants to ensure the security of their personal devices, online accounts, and digital information can benefit from understanding hacking and securing practices. This includes individuals who use computers, smartphones, social media, or online banking platforms.
02
Organizations: Businesses, government agencies, and non-profit organizations require hacking and securing knowledge and expertise to protect their sensitive data, intellectual property, and customer information. Implementing effective cybersecurity measures is crucial in today's digital landscape to prevent data breaches and financial losses.
03
IT Professionals: IT professionals, including system administrators, software developers, network engineers, and security analysts, need to have a deep understanding of hacking and securing concepts. They are responsible for designing, implementing, and maintaining secure systems, networks, and applications, and must be able to detect and respond to potential cyber threats.
04
Ethical Hackers: Organizations often hire ethical hackers, also known as penetration testers or white-hat hackers, to identify vulnerabilities in their systems and networks. These professionals use hacking techniques to simulate attacks and help organizations strengthen their defenses against potential threats.
05
Law Enforcement and Legal Professionals: Hacking and securing knowledge is essential for law enforcement officers, prosecutors, and judges dealing with cybercrime cases. Understanding hacking techniques and cybersecurity concepts enables them to effectively investigate, prosecute, and adjudicate cybercriminals and ensure justice is served.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I make changes in hacking and securing?
pdfFiller not only lets you change the content of your files, but you can also change the number and order of pages. Upload your hacking and securing to the editor and make any changes in a few clicks. The editor lets you black out, type, and erase text in PDFs. You can also add images, sticky notes, and text boxes, as well as many other things.
How do I edit hacking and securing in Chrome?
Adding the pdfFiller Google Chrome Extension to your web browser will allow you to start editing hacking and securing and other documents right away when you search for them on a Google page. People who use Chrome can use the service to make changes to their files while they are on the Chrome browser. pdfFiller lets you make fillable documents and make changes to existing PDFs from any internet-connected device.
Can I create an eSignature for the hacking and securing in Gmail?
When you use pdfFiller's add-on for Gmail, you can add or type a signature. You can also draw a signature. pdfFiller lets you eSign your hacking and securing and other documents right from your email. In order to keep signed documents and your own signatures, you need to sign up for an account.
What is hacking and securing?
Hacking is the unauthorized access to computer systems or networks, while securing is taking measures to protect these systems from such unauthorized access.
Who is required to file hacking and securing?
Companies and organizations that handle sensitive or confidential information are required to file hacking and securing.
How to fill out hacking and securing?
Hacking and securing forms can usually be filled out online through a secure portal provided by the regulatory authorities.
What is the purpose of hacking and securing?
The purpose of hacking and securing is to ensure that companies are taking necessary measures to protect their systems and prevent data breaches.
What information must be reported on hacking and securing?
Companies must report on their cybersecurity measures, any data breaches or hacking incidents, and the steps taken to address any vulnerabilities.
Fill out your hacking and securing online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Hacking And Securing is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.