Get the free Security Policies and Prohibited Items
Show details
Security Policies and Prohibited ItemsThese below security measures will be in effect within Super Bowl LIVE presented by Verizon.
Spectators entering the below performance areas will be subject to
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign security policies and prohibited
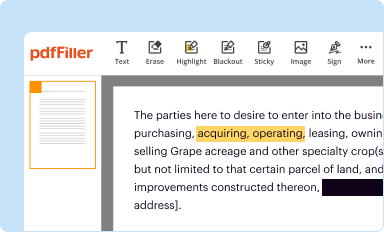
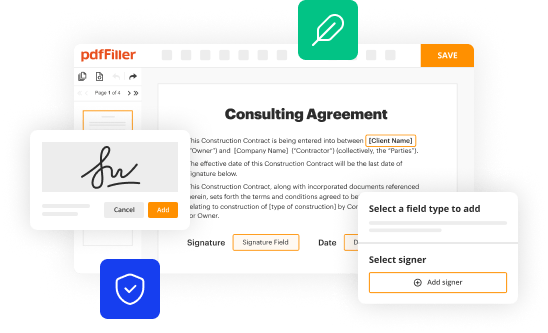
Edit your security policies and prohibited form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
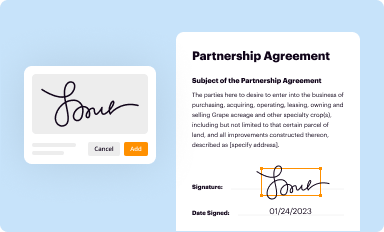
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your security policies and prohibited form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing security policies and prohibited online
Follow the steps down below to take advantage of the professional PDF editor:
1
Log in to your account. Start Free Trial and sign up a profile if you don't have one yet.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit security policies and prohibited. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
Dealing with documents is always simple with pdfFiller. Try it right now
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out security policies and prohibited
How to fill out security policies and prohibited?
01
Identify the purpose: Start by understanding the specific security requirements of your organization. Think about the potential risks, threats, and vulnerabilities that need to be addressed through security policies and prohibited activities.
02
Define the scope: Determine the boundaries of your security policies and prohibited activities. Consider which departments, systems, or individuals should be covered and specify the extent of enforcement.
03
Involve stakeholders: Collaborate with key stakeholders such as management, IT specialists, legal advisors, and employees to gather their input and ensure that the policies align with the organizational goals.
04
Research industry best practices: Look into established security frameworks, guidelines, and regulations that are relevant to your organization's industry. Incorporate these best practices into your security policies and prohibited activities.
05
Clearly articulate policies: Write clear and concise policies that explicitly state what is permitted and what is prohibited in terms of security measures. Use simple language, avoiding jargon, to ensure that everyone can understand and follow the policies.
06
Provide examples: If possible, provide examples, case studies, or scenarios that illustrate the desired behaviors and actions related to security policies. This helps employees better understand and apply the policies in their day-to-day activities.
07
Communicate the policies: Once the security policies and prohibited activities are finalized, disseminate them to all employees and stakeholders. Ensure that everyone is aware of the policies and knows where to access them for reference.
08
Train and educate: Conduct training sessions to educate employees on the importance of security policies and prohibited activities. Offer guidance on how to comply with the policies and clarify any doubts or questions that may arise.
09
Regularly review and update: Security threats and technologies evolve over time, so it is crucial to review and update the security policies and prohibited activities periodically. Keep up with new risks and incorporate any necessary revisions to ensure the continued effectiveness of the policies.
Who needs security policies and prohibited?
01
Organizations of all sizes: Whether large or small, organizations need security policies and prohibited activities to safeguard their assets, information, and reputation.
02
Different industries: Every industry faces unique security challenges, and security policies and prohibited activities help address these challenges specifically. From healthcare to finance to technology, all sectors benefit from having well-defined security measures.
03
Employees and stakeholders: Security policies and prohibited activities are not limited to top-level management; they apply to every individual within the organization. All employees, contractors, vendors, and visitors need to understand and abide by the security policies to minimize potential risks.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I edit security policies and prohibited in Chrome?
Adding the pdfFiller Google Chrome Extension to your web browser will allow you to start editing security policies and prohibited and other documents right away when you search for them on a Google page. People who use Chrome can use the service to make changes to their files while they are on the Chrome browser. pdfFiller lets you make fillable documents and make changes to existing PDFs from any internet-connected device.
How can I edit security policies and prohibited on a smartphone?
You can do so easily with pdfFiller’s applications for iOS and Android devices, which can be found at the Apple Store and Google Play Store, respectively. Alternatively, you can get the app on our web page: https://edit-pdf-ios-android.pdffiller.com/. Install the application, log in, and start editing security policies and prohibited right away.
How do I fill out security policies and prohibited on an Android device?
On Android, use the pdfFiller mobile app to finish your security policies and prohibited. Adding, editing, deleting text, signing, annotating, and more are all available with the app. All you need is a smartphone and internet.
What is security policies and prohibited?
Security policies and prohibited refer to the set of rules and regulations implemented by an organization to ensure the safety and security of its assets, information, and personnel.
Who is required to file security policies and prohibited?
All employees and contractors of the organization are required to adhere to and comply with the security policies and prohibited.
How to fill out security policies and prohibited?
Security policies and prohibited can be filled out by reviewing the guidelines provided by the organization and following the outlined procedures.
What is the purpose of security policies and prohibited?
The purpose of security policies and prohibited is to prevent unauthorized access, protect sensitive information, and maintain a secure environment for the organization.
What information must be reported on security policies and prohibited?
Information that must be reported includes any security breaches, violations of policies, and incidents involving the compromise of security measures.
Fill out your security policies and prohibited online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Security Policies And Prohibited is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.