Get the free Phase II Report on Intelligent Software Decoys: Intelligent Software Decoy Tools for...
Show details
This report documents advancements in the development of intelligent software decoys for cybersecurity, focusing on cyber deception strategies, countermeasures, and ethical considerations within the
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign phase ii report on

Edit your phase ii report on form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your phase ii report on form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing phase ii report on online
To use our professional PDF editor, follow these steps:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit phase ii report on. Add and change text, add new objects, move pages, add watermarks and page numbers, and more. Then click Done when you're done editing and go to the Documents tab to merge or split the file. If you want to lock or unlock the file, click the lock or unlock button.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
With pdfFiller, it's always easy to deal with documents. Try it right now
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
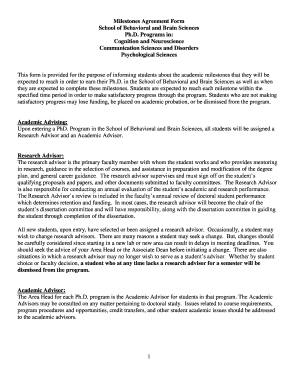
How to fill out phase ii report on

How to fill out Phase II Report on Intelligent Software Decoys: Intelligent Software Decoy Tools for Cyber Counterintelligence and Security Countermeasures
01
Start by reviewed the Phase II Report guidelines provided by the funding agency or organization.
02
Gather all necessary data and findings from your research on Intelligent Software Decoys.
03
Outline the report structure, including sections such as Introduction, Background, Methodology, Findings, and Conclusion.
04
Write the Introduction, summarizing the purpose and scope of the report.
05
Present the Background, detailing the context and relevance of Intelligent Software Decoys in cybersecurity.
06
Describe the Methodology used in developing the tools, including any experiments and tests conducted.
07
Summarize your Findings, highlighting the effectiveness of the software decoys and any significant outcomes.
08
Conclude with insights and recommendations based on your research results.
09
Include any appendices or supporting documents needed to validate your report.
10
Review and edit your report for clarity, coherence, and adherence to formatting guidelines before submission.
Who needs Phase II Report on Intelligent Software Decoys: Intelligent Software Decoy Tools for Cyber Counterintelligence and Security Countermeasures?
01
Cybersecurity professionals seeking advanced counterintelligence solutions.
02
Government agencies aiming to enhance national security measures.
03
Organizations interested in improving their defenses against cyber threats.
04
Researchers and developers working in the field of cybersecurity.
05
Contractors and vendors developing tools for security and counterintelligence purposes.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is Phase II Report on Intelligent Software Decoys: Intelligent Software Decoy Tools for Cyber Counterintelligence and Security Countermeasures?
The Phase II Report on Intelligent Software Decoys involves documenting the development and effectiveness of software tools designed to deceive and mislead cyber adversaries, enhancing security countermeasures and cyber counterintelligence efforts.
Who is required to file Phase II Report on Intelligent Software Decoys: Intelligent Software Decoy Tools for Cyber Counterintelligence and Security Countermeasures?
Entities or organizations that have developed or are utilizing intelligent software decoy tools for cyber counterintelligence and security measures are required to file the Phase II Report.
How to fill out Phase II Report on Intelligent Software Decoys: Intelligent Software Decoy Tools for Cyber Counterintelligence and Security Countermeasures?
To fill out the Phase II Report, individuals or organizations should provide detailed descriptions of their software decoy tools, methodologies used, outcomes and effectiveness metrics, as well as any insights gained during the implementation of these tools.
What is the purpose of Phase II Report on Intelligent Software Decoys: Intelligent Software Decoy Tools for Cyber Counterintelligence and Security Countermeasures?
The purpose of the Phase II Report is to evaluate the performance and impact of intelligent software decoys in strengthening cybersecurity measures and to inform further developments and strategic decisions in the realm of cyber counterintelligence.
What information must be reported on Phase II Report on Intelligent Software Decoys: Intelligent Software Decoy Tools for Cyber Counterintelligence and Security Countermeasures?
The report must include information such as the design and architecture of the decoy tools, implementation strategies, performance metrics, lessons learned, and recommendations for future improvements in cybersecurity practices.
Fill out your phase ii report on online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Phase Ii Report On is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.