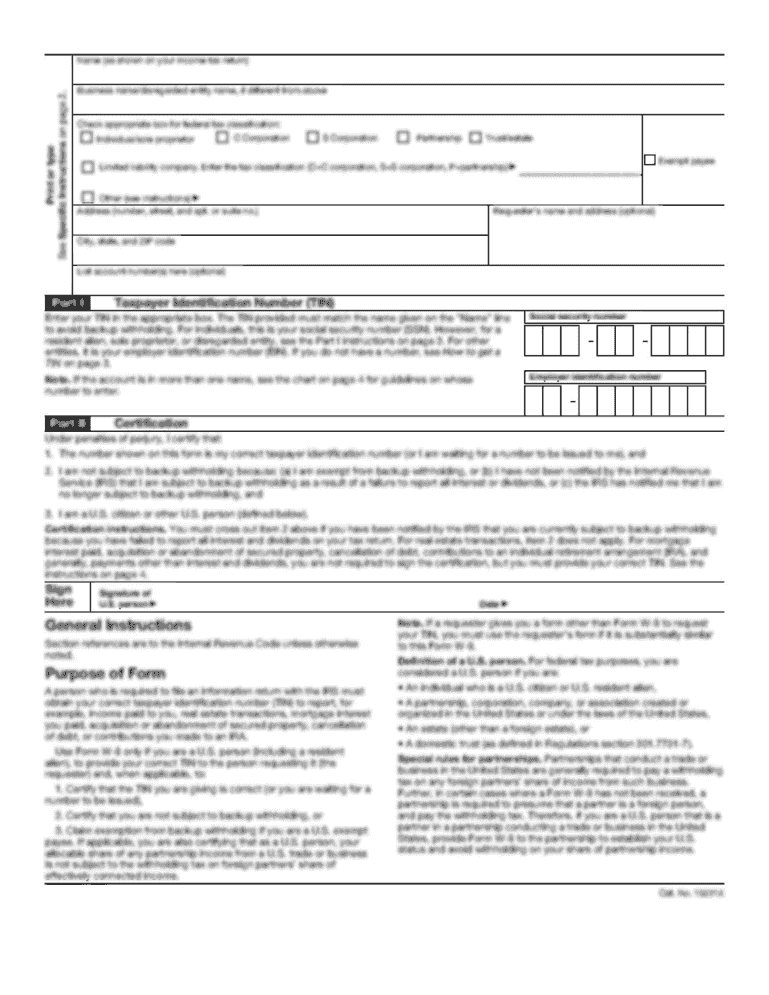
Get the free Automating the Most Critical Security Controls
Show details
This document discusses the importance of automating key cybersecurity controls, the challenges faced by CIOs in managing cyber security efficiently, and how to prioritize investments based on the
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign automating form most critical

Edit your automating form most critical form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your automating form most critical form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit automating form most critical online
Follow the steps down below to take advantage of the professional PDF editor:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit automating form most critical. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Save your file. Select it from your list of records. Then, move your cursor to the right toolbar and choose one of the exporting options. You can save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud, among other things.
Dealing with documents is simple using pdfFiller.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out automating form most critical

How to fill out Automating the Most Critical Security Controls
01
Identify the critical security controls relevant to your organization.
02
Assess current security measures and identify gaps.
03
Select appropriate automation tools and technologies.
04
Define workflows and processes for each security control.
05
Integrate automation tools with existing systems and infrastructure.
06
Test the automation implementation to ensure effectiveness.
07
Monitor and update automation processes regularly.
Who needs Automating the Most Critical Security Controls?
01
Organizations looking to enhance their security posture.
02
Security teams aiming to improve efficiency and accuracy.
03
Compliance officers who need to meet regulatory requirements.
04
IT departments responsible for managing security infrastructure.
05
Businesses seeking to minimize risk and potential data breaches.
Fill
form
: Try Risk Free






People Also Ask about
What are the three types of security controls?
Layered Approach Combining administrative, technical, and physical controls is a layered security approach. This is key to protecting business assets from various threats.
What are the 3 main security control layers?
Types of Security Controls These include barriers such as locks, fences, biometrics, surveillance systems, and guards. Their primary function is to prevent physical intrusion that could lead to data breaches or equipment theft.
Are CIS Controls pay per use?
Are the CIS Controls free? Yes, the CIS Controls are free to use by anyone to improve their own cybersecurity.
Who created the CIS Controls?
Initially published by the SANS Institute in 2009, the CIS controls were produced through knowledge sharing between a consortium of public and private sector organizations.
What is the latest version of CIS?
The Center for Internet Security (CIS) released version 8.1 of its popular CIS Critical Controls on June 25, 2024. Building on version 8.0, CIS Controls v8. 1 provides even clearer guidance for improving organizations' cybersecurity programs.
What are 3 primary types of security controls?
Overview of security controls Security controls are essential components of any risk management strategy and help protect federal information systems from potential threats. The National Institute of Standards and Technology (NIST) defines three types of security controls: preventive, detective, and corrective.
What are the primary security controls?
When it comes to the different types of business security systems they are: CCTV Surveillance / Security Cameras. Access Control. Security & Intruder Alarms.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is Automating the Most Critical Security Controls?
Automating the Most Critical Security Controls refers to the process of implementing automated systems and tools to enhance the efficiency and effectiveness of essential security measures within an organization. These controls are designed to protect sensitive data and systems from vulnerabilities and threats.
Who is required to file Automating the Most Critical Security Controls?
Organizations that are subject to regulatory compliance requirements or that prioritize cybersecurity best practices are required to file Automating the Most Critical Security Controls. This typically includes businesses in industries such as finance, healthcare, and government.
How to fill out Automating the Most Critical Security Controls?
To fill out Automating the Most Critical Security Controls, organizations must gather relevant data about their existing security measures, identify gaps, and document the implementation of automated tools that address these critical controls. This process may involve completing a standardized template or reporting format provided by governing bodies.
What is the purpose of Automating the Most Critical Security Controls?
The purpose of Automating the Most Critical Security Controls is to streamline and improve the organization’s security posture by reducing manual processes, enhancing response times, ensuring compliance, and minimizing human error in security practices.
What information must be reported on Automating the Most Critical Security Controls?
When reporting on Automating the Most Critical Security Controls, organizations must provide information on the specific controls being automated, the tools used, the effectiveness of these controls, incident reports related to security breaches, compliance status, and any ongoing improvements in the security framework.
Fill out your automating form most critical online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Automating Form Most Critical is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.





















