Get the free uch computer system security statemtn form
Show details
UNIVERSITY OF COLORADO HOSPITAL Information Services Department Computer System Security Statement 1. Any individual who requires use of computer applications will be assigned a unique sign-on code
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign uch computer system security
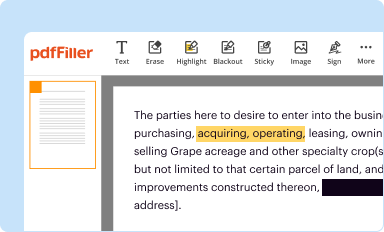
Edit your uch computer system security form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
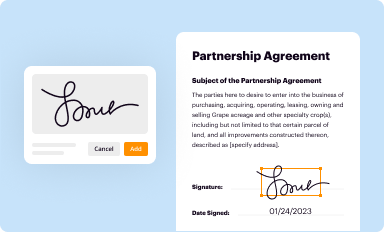
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
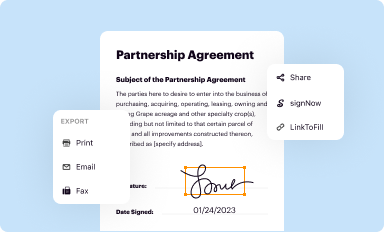
Share your form instantly
Email, fax, or share your uch computer system security form via URL. You can also download, print, or export forms to your preferred cloud storage service.
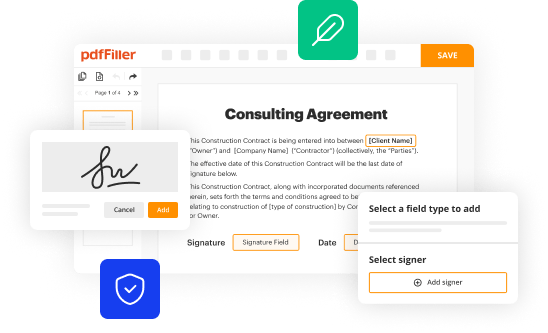
Editing uch computer system security online
To use our professional PDF editor, follow these steps:
1
Log in to account. Start Free Trial and sign up a profile if you don't have one yet.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit uch computer system security. Add and replace text, insert new objects, rearrange pages, add watermarks and page numbers, and more. Click Done when you are finished editing and go to the Documents tab to merge, split, lock or unlock the file.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
It's easier to work with documents with pdfFiller than you can have ever thought. You may try it out for yourself by signing up for an account.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out uch computer system security
To fill out uch computer system security, follow these steps:
01
Identify the potential threats and vulnerabilities to your computer system. Conduct a thorough assessment to understand the specific risks you might face.
02
Implement strong access controls and user authentication measures. This includes requiring complex passwords, regularly changing them, and using multi-factor authentication whenever possible.
03
Install and regularly update reliable antivirus software to protect against malware and other malicious programs. Make sure the software is configured to perform automated scans and updates.
04
Regularly update your operating system and all installed software. Patches and updates often include security fixes that address known vulnerabilities.
05
Encrypt sensitive data to ensure that even if it is compromised, the information remains unreadable and unusable to unauthorized individuals.
06
Set up a robust firewall to monitor and control incoming and outgoing network traffic. Configure it to block access to potentially dangerous websites and unauthorized network connections.
07
Educate yourself and your employees about safe online practices. This includes recognizing phishing attempts, avoiding suspicious downloads or links, and being cautious when sharing sensitive information.
08
Regularly back up important data and ensure that backups are stored securely and independently from your computer system. This will help mitigate the impact of any potential data loss or system failure.
Who needs uch computer system security?
01
Individuals who use computers for personal purposes, such as online banking, shopping, and social media, need computer system security to protect their personal information and prevent identity theft.
02
Small businesses and startups that rely on computer systems to store sensitive customer data, financial records, and intellectual property need computer system security to safeguard their assets and maintain the trust of their clients.
03
Large enterprises and organizations that handle vast amounts of data, including healthcare providers, financial institutions, and government agencies, require computer system security to protect against cyber attacks and data breaches that could have severe consequences.
In conclusion, anyone who uses a computer system, whether it is for personal or professional purposes, needs effective computer system security to ensure the integrity, confidentiality, and availability of their data and systems.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
Where do I find uch computer system security?
It's simple using pdfFiller, an online document management tool. Use our huge online form collection (over 25M fillable forms) to quickly discover the uch computer system security. Open it immediately and start altering it with sophisticated capabilities.
How do I fill out uch computer system security using my mobile device?
You can quickly make and fill out legal forms with the help of the pdfFiller app on your phone. Complete and sign uch computer system security and other documents on your mobile device using the application. If you want to learn more about how the PDF editor works, go to pdfFiller.com.
How do I edit uch computer system security on an Android device?
The pdfFiller app for Android allows you to edit PDF files like uch computer system security. Mobile document editing, signing, and sending. Install the app to ease document management anywhere.
What is uch computer system security?
UCH computer system security refers to the measures in place to protect a computer system from unauthorized access, use, disclosure, disruption, modification, or destruction, ensuring its availability, integrity, and confidentiality.
Who is required to file uch computer system security?
Any individual, organization, or entity that owns, operates, or maintains a computer system is required to file uch computer system security.
How to fill out uch computer system security?
To fill out uch computer system security, you need to gather all relevant information about the computer system's security measures, incident response plans, and any past security breaches or vulnerabilities. This information can then be used to complete the necessary forms or reports.
What is the purpose of uch computer system security?
The purpose of uch computer system security is to safeguard computer systems and the sensitive information they store or process from unauthorized access, use, or disclosure. It helps in preventing security breaches, data theft, disruption of services, and other cyber threats.
What information must be reported on uch computer system security?
The exact information that must be reported on uch computer system security may vary depending on the specific requirements and regulations in place. However, common information that may need to be reported includes the security controls in place, incident response plans, past security incidents or breaches, and any identified vulnerabilities or risks.
Fill out your uch computer system security online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Uch Computer System Security is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.