Get the free ACCESS CONTROL APPLICATION
Show details
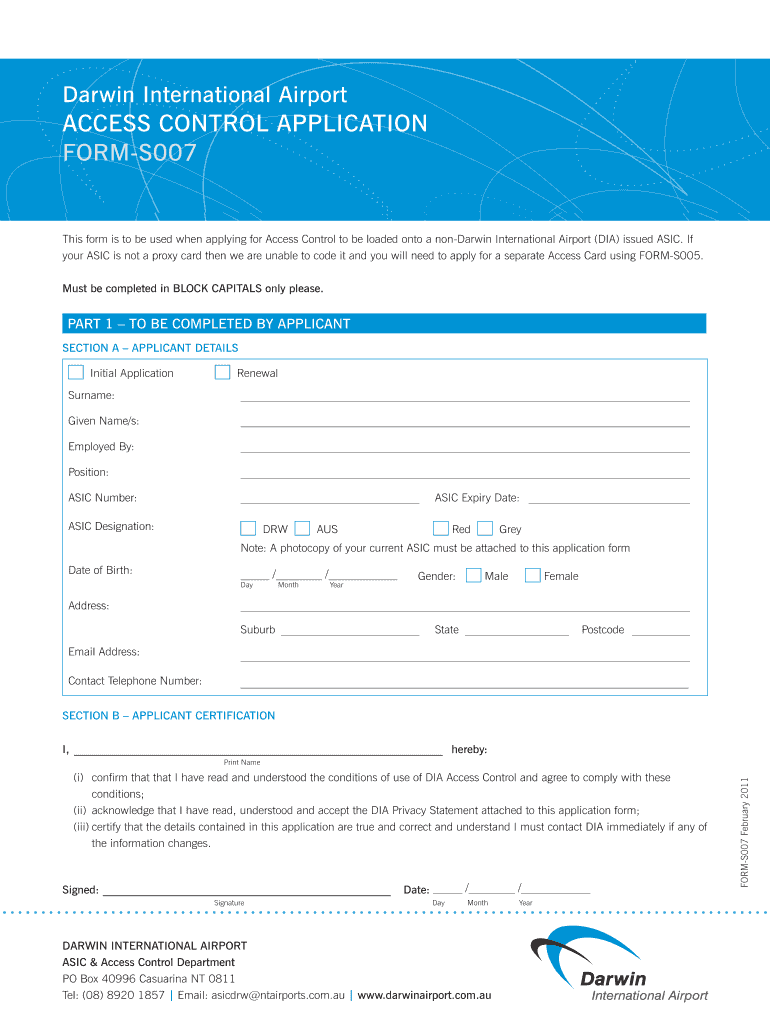
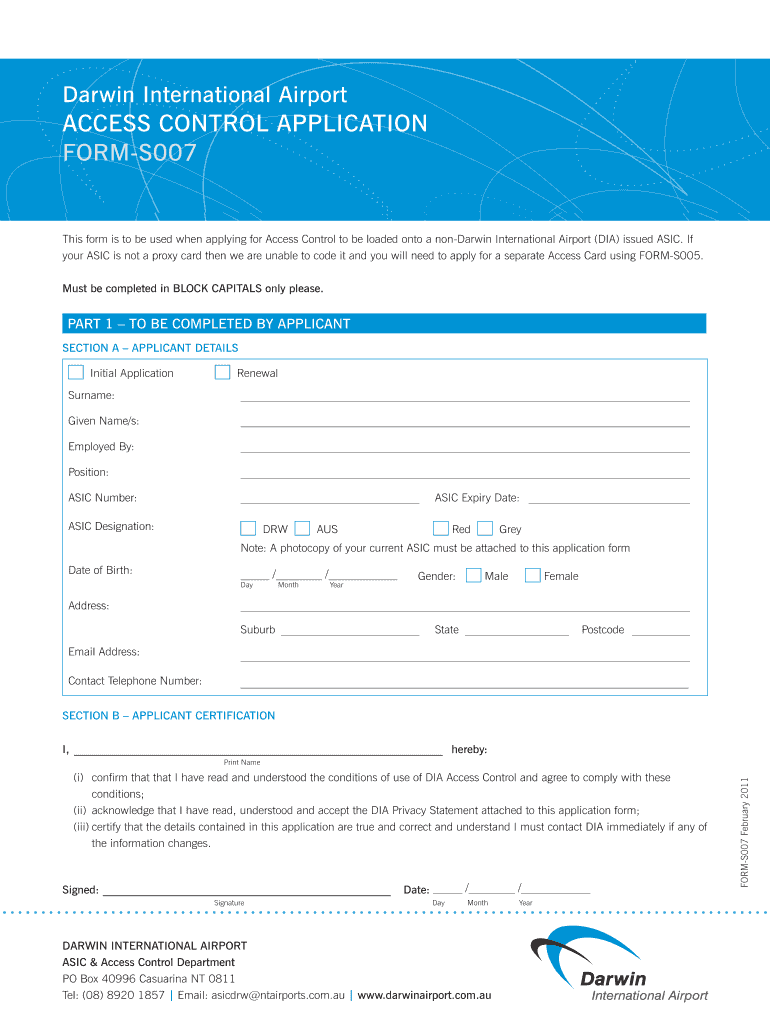
This form is used for applying for Access Control to be loaded onto a non-Darwin International Airport issued ASIC, including details about the applicant and employer, certification of correctness,
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign access control application

Edit your access control application form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your access control application form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing access control application online
To use the services of a skilled PDF editor, follow these steps below:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit access control application. Add and change text, add new objects, move pages, add watermarks and page numbers, and more. Then click Done when you're done editing and go to the Documents tab to merge or split the file. If you want to lock or unlock the file, click the lock or unlock button.
4
Save your file. Select it in the list of your records. Then, move the cursor to the right toolbar and choose one of the available exporting methods: save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out access control application

How to fill out ACCESS CONTROL APPLICATION
01
Obtain the ACCESS CONTROL APPLICATION form from the relevant authority or their website.
02
Fill in your personal details, including name, address, contact number, and email.
03
Specify the purpose of access control in the designated section.
04
Provide details of the area or facility you wish to access.
05
Complete any required background information or verification sections.
06
If necessary, include any references or endorsements from relevant parties.
07
Review the application for completeness and accuracy.
08
Submit the application either online or via the specified submission method.
Who needs ACCESS CONTROL APPLICATION?
01
Individuals or organizations requiring restricted access to secure areas or facilities.
02
Employees needing access to company premises.
03
Contractors or service providers who need to enter secured locations.
04
Guests or visitors who require temporary access for specific purposes.
Fill
form
: Try Risk Free






People Also Ask about
What is access control application?
Access control is an essential element of security that determines who is allowed to access certain data, apps, and resources—and in what circumstances. In the same way that keys and preapproved guest lists protect physical spaces, access control policies protect digital spaces.
What are the 3 types of access control?
Here's a summary: The main purpose of access control is to exclude unauthorized persons from access while streamlining access for those with proper authorizations. Access control systems support operational efficiency, compliance with regulations, and site safety.
What is an access control application?
Access control is an essential element of security that determines who is allowed to access certain data, apps, and resources—and in what circumstances. In the same way that keys and preapproved guest lists protect physical spaces, access control policies protect digital spaces.
What is access control in English?
Access Control Definition Access control is a data security process that enables organizations to manage who is authorized to access corporate data and resources. Secure access control uses policies that verify users are who they claim to be and ensures appropriate control access levels are granted to users.
What are the 4 types of access control?
Below we have talked about the foundational elements of access control that collectively strengthen organizations defense and ensure integrity of its resources. Identification: Authentication: Authorization: Mandatory Access Control (MAC) Discretionary Access Control (DAC) Role-Based Access Control (RBAC)
What is an example of an access control?
Access control is a security measure which is put in place to regulate the individuals that can view, use, or have access to a restricted environment. Various access control examples can be found in the security systems in our doors, key locks, fences, biometric systems, motion detectors, badge system, and so forth.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is ACCESS CONTROL APPLICATION?
ACCESS CONTROL APPLICATION is a formal procedure or system used to manage and restrict access to specific resources, facilities, or information. It ensures that only authorized individuals have the ability to enter, utilize, or view sensitive data or areas.
Who is required to file ACCESS CONTROL APPLICATION?
Individuals or organizations that require access to restricted areas, data, or systems are required to file an ACCESS CONTROL APPLICATION. This typically includes employees, contractors, vendors, and anyone needing permission for access.
How to fill out ACCESS CONTROL APPLICATION?
To fill out an ACCESS CONTROL APPLICATION, individuals must provide personal identification information, the specific areas or systems they seek access to, the purpose of access, and any relevant background or security information. Additionally, applicants may need to adhere to specific guidelines or templates provided by the issuing authority.
What is the purpose of ACCESS CONTROL APPLICATION?
The purpose of ACCESS CONTROL APPLICATION is to ensure security by regulating who can access certain areas or information. It enables organizations to safeguard sensitive data, control physical access to buildings or facilities, and maintain compliance with regulations.
What information must be reported on ACCESS CONTROL APPLICATION?
Information that must be reported on an ACCESS CONTROL APPLICATION usually includes the applicant's full name, contact details, purpose of access, date of requested access, specific areas or resources needed, any associated approvals, and potentially a background check or identification verification.
Fill out your access control application online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Access Control Application is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.