Get the free Firewall Change Customer Procedure - utoledo
Show details
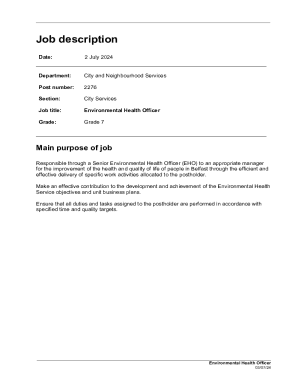
Firewall Change Customer Procedure Primary Point of Contact Chad Hrivnyak Overview IT Security processes firewall change requests from appropriate faculty and staff. Vendors must work through their application specialists to process requests.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign firewall change customer procedure

Edit your firewall change customer procedure form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your firewall change customer procedure form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit firewall change customer procedure online
Use the instructions below to start using our professional PDF editor:
1
Check your account. In case you're new, it's time to start your free trial.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit firewall change customer procedure. Text may be added and replaced, new objects can be included, pages can be rearranged, watermarks and page numbers can be added, and so on. When you're done editing, click Done and then go to the Documents tab to combine, divide, lock, or unlock the file.
4
Get your file. When you find your file in the docs list, click on its name and choose how you want to save it. To get the PDF, you can save it, send an email with it, or move it to the cloud.
With pdfFiller, it's always easy to work with documents. Check it out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out firewall change customer procedure

How to fill out Firewall Change Customer Procedure
01
Begin by accessing the Firewall Change Request Form.
02
Enter the customer's information, including name, company, and contact details.
03
Specify the current firewall configuration that requires changes.
04
Clearly outline the requested changes, detailing both new rules and deletions.
05
Include justification for the changes, explaining the necessity and expected impact.
06
Specify the timeframe for the changes to be implemented.
07
Review the request for accuracy and completeness.
08
Submit the change request to the appropriate department for approval.
09
Monitor the request status and follow up as necessary.
Who needs Firewall Change Customer Procedure?
01
Network administrators managing firewall settings.
02
IT security teams needing to update firewall rules.
03
Compliance officers ensuring adherence to security policies.
04
Any personnel responsible for overseeing network security operations.
Fill
form
: Try Risk Free






People Also Ask about
How to build a firewall for beginners?
Step 1: Secure your firewall (Seems redundant, we know.) Step 2: Architect firewall zones and IP addresses (No heavy lifting required.) Step 3: Configure access control lists (It's your party, invite who you want.) Step 4: Configure your other firewall services and logging (Your non-vinyl record collection.)
What is the firewall rule language?
A firewall rule consists of several clauses chained together to match specific criteria for each packet. The clauses represent specific layers in the protocol stack. Each clause can be broken down into conditions and expressions.
How to configure a firewall step by step?
Here is how to configure a firewall securely: Secure the firewall. Establish firewall zones and an IP address structure. Configure access control lists (ACLs) Configure other firewall services and logging. Test the firewall configuration. Manage firewall continually.
How to configure a firewall in 5 steps?
How to Configure a Firewall in 5 Steps Step 1: Secure your firewall. Step 2: Architect your firewall zones and IP addresses. Step 3: Configure access control lists. Step 4: Configure your other firewall services and logging. Step 5: Test your firewall configuration.
How do I setup a firewall on my computer?
8 Steps to Set Up a Firewall Prepare for Installation. Set Secure Firewall Rules & ACLs. Establish Your Network Zones Structure. Configure Firewall Policies. Configure Logging & Alerts. Test & Audit Your Firewall. Deploy the Firewall. Manage & Maintain the Correct Firewall Configuration.
How do you configure a firewall?
How To Configure A Firewall Secure the firewall. Establish firewall zones and an IP address structure. Configure access control lists (ACLs) Configure other firewall services and logging. Test the firewall configuration. Manage firewall continually.
What are the five 5 steps to configure a firewall?
How to Configure a Firewall in 5 Steps Step 1: Secure your firewall. Step 2: Architect your firewall zones and IP addresses. Step 3: Configure access control lists. Step 4: Configure your other firewall services and logging. Step 5: Test your firewall configuration.
What is the firewall rule management process?
It involves setting up rules to allow or block specific traffic, regularly auditing these rules, and monitoring logs to detect and respond to potential security incidents. Effective firewall management ensures vulnerabilities are addressed, threats are mitigated, and network operations remain secure and uninterrupted.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is Firewall Change Customer Procedure?
The Firewall Change Customer Procedure is a set of guidelines and steps that must be followed when requesting changes to firewall configurations within an organization's network infrastructure.
Who is required to file Firewall Change Customer Procedure?
Typically, IT personnel, network administrators, or any authorized staff member responsible for managing network security must file the Firewall Change Customer Procedure.
How to fill out Firewall Change Customer Procedure?
To fill out the Firewall Change Customer Procedure, a requester must provide details such as the type of change requested, the reason for the change, affected systems, and the desired implementation date, along with any required approvals.
What is the purpose of Firewall Change Customer Procedure?
The purpose of the Firewall Change Customer Procedure is to ensure that all changes to firewall settings are thoroughly documented, reviewed, and approved to maintain network security and compliance.
What information must be reported on Firewall Change Customer Procedure?
The information that must be reported includes the description of the change, the rationale behind it, technical details of the systems affected, potential impacts, and the signature of the person requesting the change.
Fill out your firewall change customer procedure online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Firewall Change Customer Procedure is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.