Get the free Information Security Training for LSUHSC-NO's Non-Computer Users - lsuhsc
Show details
This document serves as a self-study training packet for employees, volunteers, contractors, and other members of LSUHSC-NO’s workforce who do not have access to the network, focusing on compliance
We are not affiliated with any brand or entity on this form
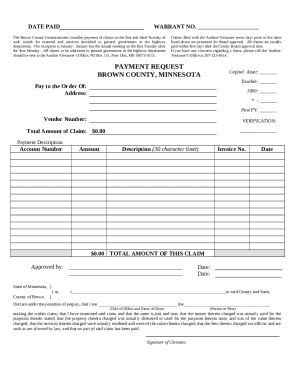
Get, Create, Make and Sign information security training for
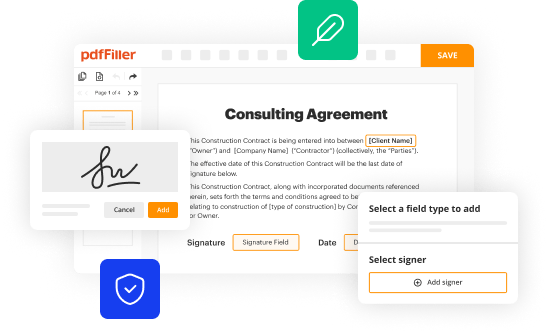
Edit your information security training for form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
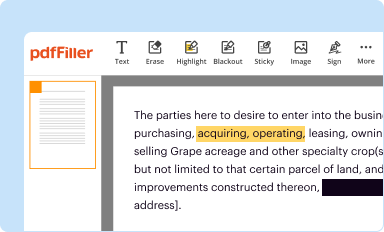
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
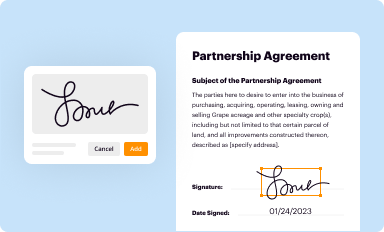
Share your form instantly
Email, fax, or share your information security training for form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit information security training for online
Here are the steps you need to follow to get started with our professional PDF editor:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Simply add a document. Select Add New from your Dashboard and import a file into the system by uploading it from your device or importing it via the cloud, online, or internal mail. Then click Begin editing.
3
Edit information security training for. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
The use of pdfFiller makes dealing with documents straightforward.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out information security training for
How to fill out Information Security Training for LSUHSC-NO's Non-Computer Users
01
Visit the LSUHSC-NO Information Security Training portal.
02
Log in using your LSUHSC credentials.
03
Navigate to the 'Non-Computer Users Training' section.
04
Review the provided training materials and guidelines.
05
Complete the required training modules.
06
Take the assessment quiz to evaluate your understanding.
07
Submit your completed training for certification.
08
Keep a copy of your completion certificate for your records.
Who needs Information Security Training for LSUHSC-NO's Non-Computer Users?
01
All non-computer users at LSUHSC-NO who handle sensitive information.
02
Staff members in administrative or support roles that do not utilize computers directly.
03
Any personnel involved in patient care or handling confidential materials without direct computer access.
Fill
form
: Try Risk Free






People Also Ask about
What is information security program training?
Home Training Information Security. The Information Security (INFOSEC) Program establishes policies, procedures, and requirements to protect classified and controlled unclassified information (CUI) that, if disclosed, could cause damage to national security.
What is the purpose of IT security training?
Security awareness training empowers employees to recognize and mitigate cyber risks, fostering a culture of vigilance and resilience. It minimizes human error, reducing breaches, and safeguarding sensitive data and assets.
What is information security training?
Security training often teaches employees best practices and security protocols for communicating through email, managing social media accounts and accessing sensitive business data from mobile devices.
Is information security high paying?
For example, the median salary for an information security analyst is $124,910, which is over double the median salary across all industries. The U.S. Bureau of Labor and Statistics also reported that the typical experience for the role is less than five years, and a common education level is a Bachelor's degree.
Why do we need to study information security?
Security awareness training can help organizations reduce the risk of data breaches, malware infections, phishing attempts, and other malicious activities. By providing employees with the knowledge and skills they need to stay safe online, organizations can ensure their data is secure and protected from cyberattacks.
What is the information security course about?
Learn about a variety of topics related to IT Security, including the different types of information and how to store them and best practice when using the internet and email.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is Information Security Training for LSUHSC-NO's Non-Computer Users?
Information Security Training for LSUHSC-NO's Non-Computer Users is a program designed to educate individuals who do not regularly use computers on the principles and practices of safeguarding sensitive information. The training focuses on recognizing security threats, maintaining confidentiality, and following proper protocols to mitigate risks.
Who is required to file Information Security Training for LSUHSC-NO's Non-Computer Users?
All non-computer users at LSUHSC-NO, including staff and personnel who handle sensitive information without utilizing computer systems, are required to complete the Information Security Training.
How to fill out Information Security Training for LSUHSC-NO's Non-Computer Users?
To fill out Information Security Training for LSUHSC-NO's Non-Computer Users, participants need to complete the training modules, usually available online, and then submit any required documentation or forms as instructed by the training program guidelines.
What is the purpose of Information Security Training for LSUHSC-NO's Non-Computer Users?
The purpose of Information Security Training for LSUHSC-NO's Non-Computer Users is to ensure that all staff understand the importance of information security, the potential risks they may encounter, and the appropriate actions to take to protect sensitive information from unauthorized access or breaches.
What information must be reported on Information Security Training for LSUHSC-NO's Non-Computer Users?
Participants must report their completion status, any test scores associated with the training, and feedback on the training materials, as well as any identified areas needing improvement in their understanding of information security practices.
Fill out your information security training for online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Information Security Training For is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.