Get the free Smith College Information Security Risk Assessment Checklist - smith
Show details
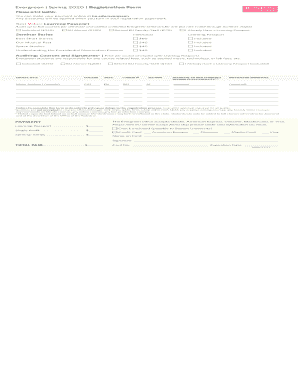
This checklist is designed for individual data handlers conducting an information security risk assessment, helping them evaluate security risks related to personal and classified information.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign smith college information security

Edit your smith college information security form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your smith college information security form via URL. You can also download, print, or export forms to your preferred cloud storage service.
How to edit smith college information security online
To use our professional PDF editor, follow these steps:
1
Log in. Click Start Free Trial and create a profile if necessary.
2
Upload a document. Select Add New on your Dashboard and transfer a file into the system in one of the following ways: by uploading it from your device or importing from the cloud, web, or internal mail. Then, click Start editing.
3
Edit smith college information security. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
With pdfFiller, dealing with documents is always straightforward. Try it now!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out smith college information security

How to fill out Smith College Information Security Risk Assessment Checklist
01
Gather all relevant information regarding the systems and processes being assessed.
02
Review the checklist to understand each section and its requirements.
03
Identify the assets to be evaluated, such as data, hardware, and software.
04
Assess the potential risks associated with each asset, considering threats and vulnerabilities.
05
Document existing security controls that mitigate identified risks.
06
Rate the likelihood and impact of each risk occurring.
07
Provide recommendations for improving security measures based on the assessment.
08
Compile the completed checklist into a final document for review.
Who needs Smith College Information Security Risk Assessment Checklist?
01
Administrative staff responsible for information security.
02
Departments handling sensitive or regulated data.
03
IT personnel involved in risk management and compliance.
04
Staff involved in policy-making or security governance.
Fill
form
: Try Risk Free






People Also Ask about
What is a security risk assessment checklist?
A Security Risk Assessment Checklist is a tool used to identify and assess potential security risks in a given environment. It is typically used by organizations to evaluate the security of their systems and to identify areas that may need improvement.
What is the Committee on Academic Priorities Smith College?
The provost chairs the Committee on Academic Priorities (CAP), an elected committee of faculty, charged with establishing and maintaining the educational and curricular priorities of the undergraduate, certificate and graduate programs of the college.
Is Smith College a prestigious school?
The acceptance rate at Smith College is 19.7%. In other words, of 100 students who apply, only 20 are admitted. This means the school is very selective. Scores are vital to getting past their first round of filters.
What is the acceptance rate for Smith College?
The Committee on Academic Standing (CAS) meets bi-weekly during the academic year to consider General Petitions submitted by students for exceptions to certain deadlines (i.e. add/drop and Credit/No Credit) and certain academic policies and regulations.
Is Smith College liberal or conservative?
Smith College is one of the top private universities in Northampton, United States. It is ranked #601-650 in QS World University Rankings 2022.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is Smith College Information Security Risk Assessment Checklist?
The Smith College Information Security Risk Assessment Checklist is a tool designed to systematically identify and evaluate potential security risks to information systems and data within the college.
Who is required to file Smith College Information Security Risk Assessment Checklist?
All staff and faculty who manage or handle sensitive information or information systems at Smith College are required to file the Information Security Risk Assessment Checklist.
How to fill out Smith College Information Security Risk Assessment Checklist?
To fill out the checklist, individuals must assess their information systems for vulnerabilities, document existing security measures, and identify areas for improvement while following the provided guidelines.
What is the purpose of Smith College Information Security Risk Assessment Checklist?
The purpose of the checklist is to ensure that all potential risks to information security are identified and assessed, promoting a safe and secure environment for handling sensitive information.
What information must be reported on Smith College Information Security Risk Assessment Checklist?
The checklist requires reporting on the types of data being handled, current security controls in place, identified vulnerabilities, and any potential impacts of data breaches.
Fill out your smith college information security online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Smith College Information Security is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.