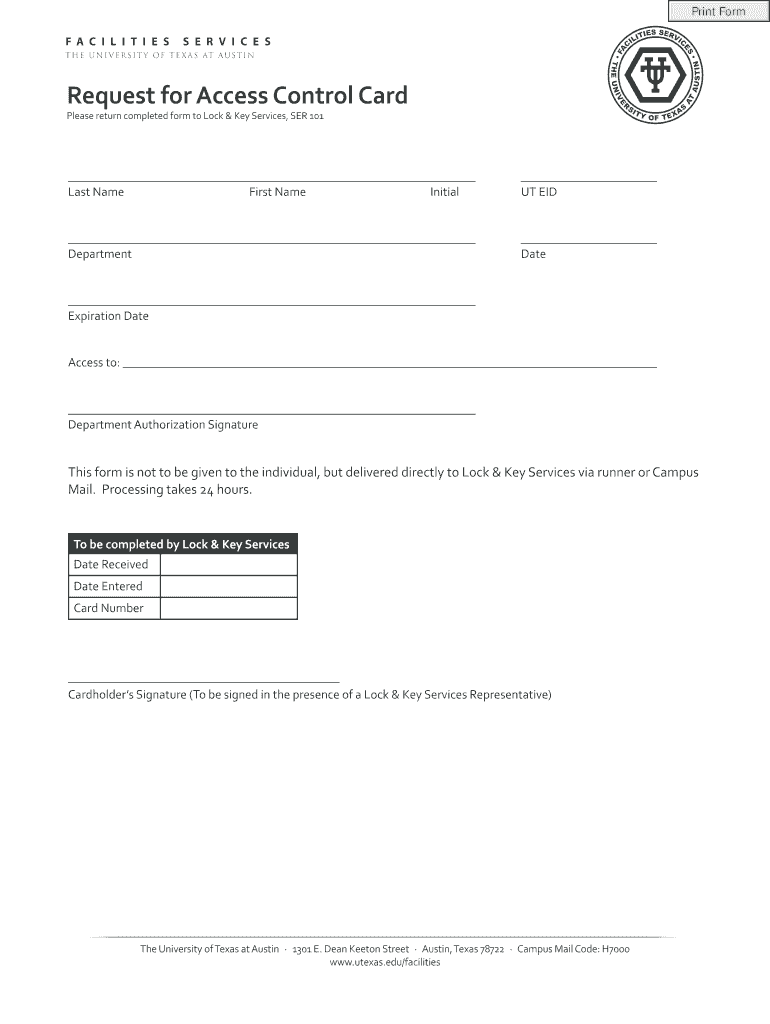
Get the free Request for Access Control Card - utexas
Show details
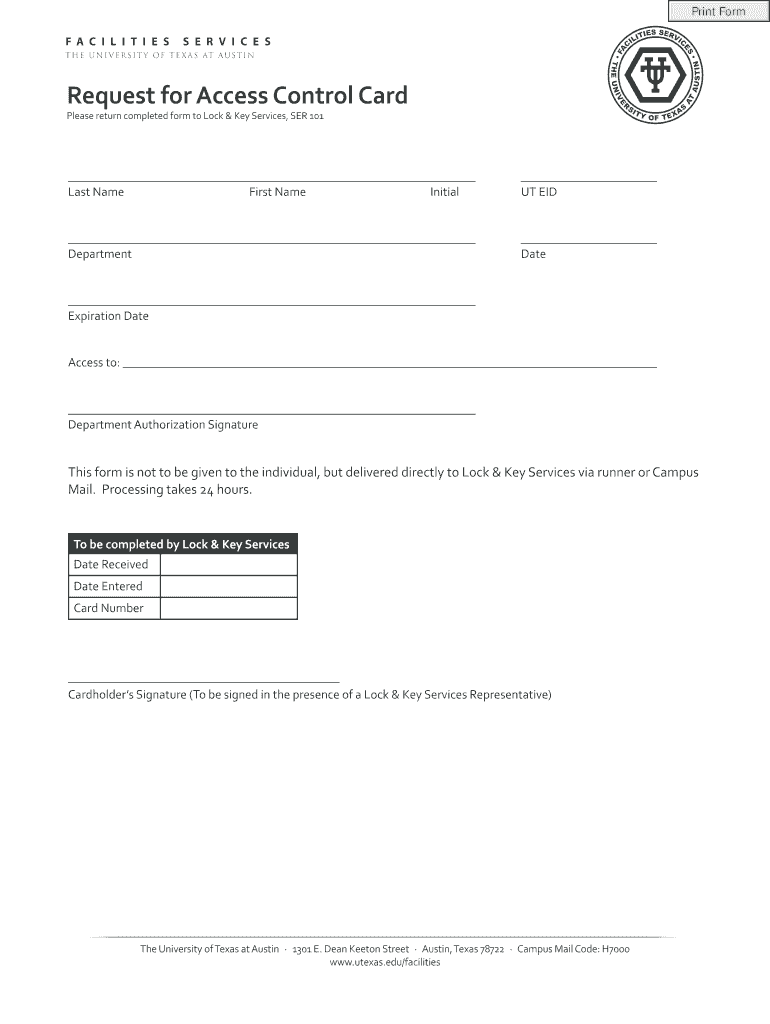
A form used to request an access control card for securing access to facilities at the University.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign request for access control

Edit your request for access control form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.

Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.

Share your form instantly
Email, fax, or share your request for access control form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing request for access control online
To use our professional PDF editor, follow these steps:
1
Check your account. If you don't have a profile yet, click Start Free Trial and sign up for one.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit request for access control. Replace text, adding objects, rearranging pages, and more. Then select the Documents tab to combine, divide, lock or unlock the file.
4
Get your file. Select the name of your file in the docs list and choose your preferred exporting method. You can download it as a PDF, save it in another format, send it by email, or transfer it to the cloud.
With pdfFiller, dealing with documents is always straightforward. Now is the time to try it!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out request for access control

How to fill out Request for Access Control Card
01
Obtain the Request for Access Control Card form from the relevant authority or department.
02
Fill in your personal information, including your full name, employee ID, and contact details.
03
Indicate the purpose for which you need the access control card.
04
Provide information about the areas or facilities you need access to.
05
Include your supervisor's name and signature to validate your request.
06
Review the form for any errors or missing information.
07
Submit the completed form to the designated office or administrator.
08
Follow up to ensure your request is being processed.
Who needs Request for Access Control Card?
01
Employees who require access to secure areas within a building or facility.
02
Contractors or vendors who need temporary access to specific locations.
03
Visitors who are authorized to enter secured premises for meetings or events.
04
Permanent staff members needing access to restricted zones as part of their job responsibilities.
Fill
form
: Try Risk Free






People Also Ask about
What is access control system in English?
Access control is a security technique that regulates who or what can view or use resources in a computing environment. It is a fundamental concept in security that minimizes risk to the business or organization.
How to write a mail for a system access request?
Begin with a brief introduction stating the purpose of your email, followed by a detailed explanation of your request. Include specific information about the access you need, such as the system or data you're requesting access to, the level of access required, and the duration14.
What is the main benefit of access control?
Access control is not just about allowing or denying access. It involves identifying an individual or system, authenticating their identity, authorizing them to access the resource, and auditing their access patterns. This process minimizes the risk of unauthorized access, protecting sensitive information and systems.
Which of the following is an example of an access control system?
The benefits of access control security Access control acts as a resolute layer of security that protects assets, applications, data and networks from unauthorized access. It significantly reduces the chances of data leaks, privilege escalation, malware and other security incidents.
What are the 3 types of access control?
Examples of access controls include physical controls like locks and biometric scanners, and logical controls like passwords, network access control systems, and data encryption. More advanced systems may use multi-factor authentication, which requires users to present multiple credentials for access.
What is access control card?
Card-Based Access Control: Types of Cards & Evolution of Access Control. Access control card readers are used for maintaining physical safety commonly at the doors. Such readers read credentials stored on a card in one or the other form to allow or restrict access to the cardholder.
How to write a mail for an internet access request?
Dear Sir, We have the honour to draw your kind attention to the fact that there is no internet facility in our college computer lab. Though we have computers, we lag behind in the race of technological development for want of internet connection with the computers.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is Request for Access Control Card?
A Request for Access Control Card is a formal application submitted to gain permission and access to restricted areas within a facility, usually requiring an identification card.
Who is required to file Request for Access Control Card?
Individuals who need access to secured areas, such as employees, contractors, or visitors, are typically required to file a Request for Access Control Card.
How to fill out Request for Access Control Card?
To fill out a Request for Access Control Card, you need to provide personal information, the purpose of the access, the duration of access needed, and any required identification or authorization signatures.
What is the purpose of Request for Access Control Card?
The purpose of a Request for Access Control Card is to ensure that only authorized individuals can enter restricted areas, thereby enhancing security and protecting sensitive information or assets.
What information must be reported on Request for Access Control Card?
The information that must be reported includes the applicant's name, position, department, reason for access, duration of access, and any relevant identification numbers or codes.
Fill out your request for access control online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.
Request For Access Control is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.