Get the free Information Security Encryption Project - utdallas
Show details
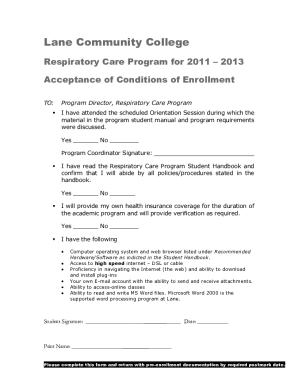
Information Security Encryption Project Pre-Encryption Waiver Laptop Owner Print Name Signature By signing above, I hereby certify that my answers, below, are complete and correct: ? Inventory tag
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign information security encryption project
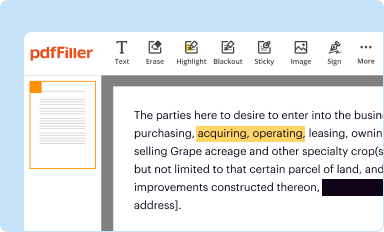
Edit your information security encryption project form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
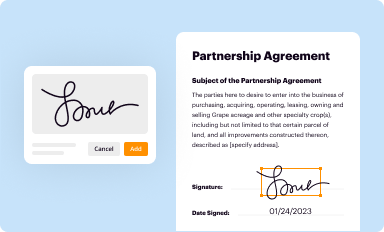
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your information security encryption project form via URL. You can also download, print, or export forms to your preferred cloud storage service.
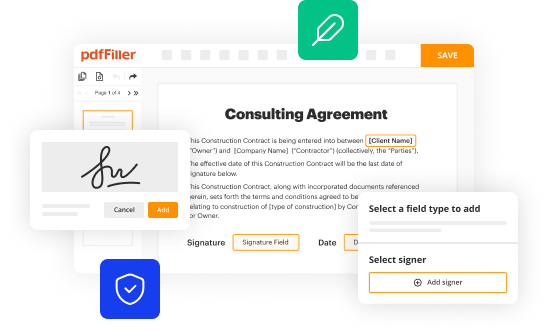
Editing information security encryption project online
Use the instructions below to start using our professional PDF editor:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit information security encryption project. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Save your file. Select it from your records list. Then, click the right toolbar and select one of the various exporting options: save in numerous formats, download as PDF, email, or cloud.
pdfFiller makes dealing with documents a breeze. Create an account to find out!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out information security encryption project
How to fill out information security encryption project:
01
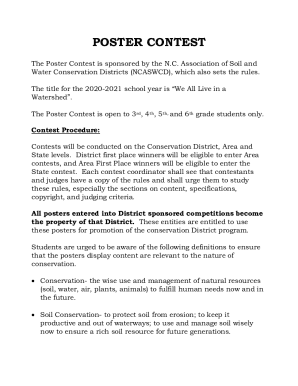
Identify the specific data and information that needs to be protected through encryption. This includes sensitive personal information, financial records, intellectual property, and any other confidential data that may be at risk.
02
Conduct a comprehensive risk assessment to determine the potential vulnerabilities and threats to the data. This will help in prioritizing the encryption efforts and allocating resources effectively.
03
Select an appropriate encryption algorithm and encryption method that aligns with the organization's security requirements and industry best practices. Consider factors such as key length, encryption strength, and compatibility with existing systems.
04
Develop an encryption policy that outlines the guidelines and procedures for implementing encryption throughout the organization. This policy should cover key management, encryption protocols, data storage, and encryption software usage.
05
Implement the encryption solution by encrypting the identified data and information. This may involve deploying encryption software, configuring encryption settings, and ensuring proper encryption of data at rest and in transit.
06
Regularly monitor and assess the effectiveness of the encryption measures. This includes conducting audits, penetration testing, and vulnerability assessments to identify any weaknesses or security gaps in the encryption implementation.
07
Provide training and awareness programs to end-users and staff members about the importance of information security encryption, its benefits, and how to properly use encryption tools and protocols.
08
Continuously update and adapt the encryption measures based on emerging technologies, evolving threats, and changes in regulatory requirements.
Who needs information security encryption project:
01
Organizations that handle sensitive customer data, such as healthcare providers, financial institutions, and e-commerce platforms, need information security encryption projects to protect the privacy and confidentiality of their customers' information.
02
Government agencies and military organizations that deal with classified or sensitive data require robust encryption to safeguard national security and prevent unauthorized access or data breaches.
03
Businesses and industries that heavily rely on intellectual property, trade secrets, or confidential research and development also need information security encryption projects to protect their sensitive information from theft, espionage, or unauthorized disclosure.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is information security encryption project?
Information Security Encryption Project is a project that aims to protect sensitive information by converting it into code or cipher to prevent unauthorized access.
Who is required to file information security encryption project?
Any organization or individual who handles sensitive information and wants to ensure its security is required to file an information security encryption project.
How to fill out information security encryption project?
To fill out an information security encryption project, you need to gather all the necessary information about the sensitive data that needs encryption, analyze the potential risks, and outline the encryption methods and procedures that will be implemented.
What is the purpose of information security encryption project?
The purpose of an information security encryption project is to safeguard sensitive data from unauthorized access, protect privacy, and prevent data breaches or information leaks.
What information must be reported on information security encryption project?
The information reported on an information security encryption project may include the types of sensitive data being encrypted, encryption methods and algorithms used, risk assessment findings, encryption key management practices, and any relevant certification or compliance requirements.
How can I modify information security encryption project without leaving Google Drive?
By integrating pdfFiller with Google Docs, you can streamline your document workflows and produce fillable forms that can be stored directly in Google Drive. Using the connection, you will be able to create, change, and eSign documents, including information security encryption project, all without having to leave Google Drive. Add pdfFiller's features to Google Drive and you'll be able to handle your documents more effectively from any device with an internet connection.
Can I create an eSignature for the information security encryption project in Gmail?
When you use pdfFiller's add-on for Gmail, you can add or type a signature. You can also draw a signature. pdfFiller lets you eSign your information security encryption project and other documents right from your email. In order to keep signed documents and your own signatures, you need to sign up for an account.
How can I edit information security encryption project on a smartphone?
You can do so easily with pdfFiller’s applications for iOS and Android devices, which can be found at the Apple Store and Google Play Store, respectively. Alternatively, you can get the app on our web page: https://edit-pdf-ios-android.pdffiller.com/. Install the application, log in, and start editing information security encryption project right away.
Fill out your information security encryption project online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Information Security Encryption Project is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.