Get the free chapter 7 lab exploring encryption methods - faculty weber
Show details
CCNA Security Chapter 7 Lab A, Exploring Encryption Methods Topology Objectives Part 1: (Optional) Build the Network and Configure the PCs Connect the PCs and configure IP addresses. Part 2: Decipher
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign chapter 7 lab exploring
Edit your chapter 7 lab exploring form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
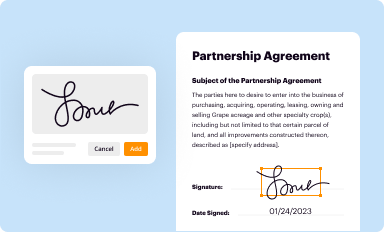
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
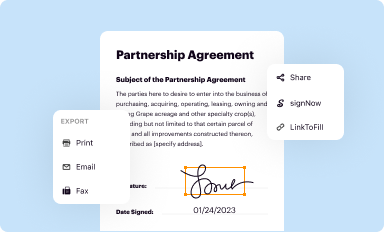
Share your form instantly
Email, fax, or share your chapter 7 lab exploring form via URL. You can also download, print, or export forms to your preferred cloud storage service.
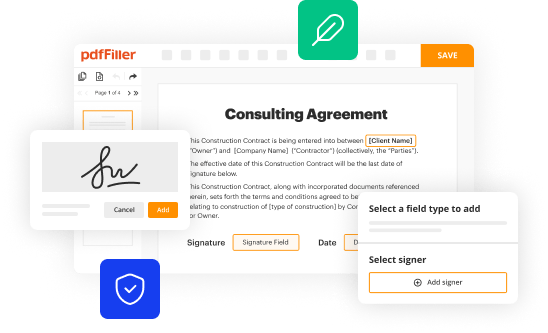
How to edit chapter 7 lab exploring online
Use the instructions below to start using our professional PDF editor:
1
Log in to your account. Start Free Trial and sign up a profile if you don't have one yet.
2
Prepare a file. Use the Add New button. Then upload your file to the system from your device, importing it from internal mail, the cloud, or by adding its URL.
3
Edit chapter 7 lab exploring. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Save your file. Select it in the list of your records. Then, move the cursor to the right toolbar and choose one of the available exporting methods: save it in multiple formats, download it as a PDF, send it by email, or store it in the cloud.
Dealing with documents is simple using pdfFiller.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out chapter 7 lab exploring
01
The first step in filling out the lab exploring encryption methods is to gather all the necessary materials and resources. This may include a computer, software programs or tools related to encryption, and any accompanying lab instructions.
02
Once you have all the required materials, carefully read through the lab instructions to understand the objectives and tasks involved. Familiarize yourself with the concepts of encryption and the specific methods that will be explored in the lab.
03
Follow the step-by-step instructions provided in the lab to perform the assigned tasks. This may involve using encryption algorithms, encrypting and decrypting data, analyzing the results, or experimenting with different encryption methods.
04
It is important to document your progress and observations throughout the lab. Take notes, record any challenges faced, and document the results obtained from each task. This documentation will help you in analyzing and reflecting on the lab experience.
05
After completing the lab tasks, review your notes and observations to summarize your findings. Reflect on the effectiveness and practicality of the encryption methods explored. Consider any advantages or limitations of each method.
06
Finally, compile all the information gathered during the lab into a comprehensive report or presentation. Include your observations, analysis, and any recommendations for further exploration or improvement in the encryption methods.
Who needs lab exploring encryption methods?
01
Professionals working in the field of computer security or data protection may require a lab exploring encryption methods to enhance their understanding and skills in implementing secure encryption techniques.
02
Students studying computer science, information technology, or cybersecurity can benefit from this lab to gain practical knowledge and hands-on experience in encryption methods. It can also help them understand the importance of encryption in securing data and communications.
03
Research organizations or institutions focusing on cryptography or data privacy may utilize this lab to expand their research and develop innovative encryption methods or algorithms.
04
Organizations dealing with sensitive information, such as financial institutions, government agencies, or healthcare providers, may find value in conducting this lab to ensure the security and confidentiality of their data.
05
Individuals who are interested in learning about encryption and its applications can also engage in this lab to explore the various methods and understand how encryption works to protect sensitive information.
Fill
form
: Try Risk Free






For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
How do I make edits in chapter 7 lab exploring without leaving Chrome?
Install the pdfFiller Google Chrome Extension in your web browser to begin editing chapter 7 lab exploring and other documents right from a Google search page. When you examine your documents in Chrome, you may make changes to them. With pdfFiller, you can create fillable documents and update existing PDFs from any internet-connected device.
How can I edit chapter 7 lab exploring on a smartphone?
Using pdfFiller's mobile-native applications for iOS and Android is the simplest method to edit documents on a mobile device. You may get them from the Apple App Store and Google Play, respectively. More information on the apps may be found here. Install the program and log in to begin editing chapter 7 lab exploring.
How do I complete chapter 7 lab exploring on an Android device?
Use the pdfFiller Android app to finish your chapter 7 lab exploring and other documents on your Android phone. The app has all the features you need to manage your documents, like editing content, eSigning, annotating, sharing files, and more. At any time, as long as there is an internet connection.
What is chapter 7 lab exploring?
Chapter 7 lab exploring is a practical exercise in a specific chapter of a textbook or educational material that focuses on exploring and applying the concepts covered in the chapter.
Who is required to file chapter 7 lab exploring?
Chapter 7 lab exploring is typically required to be completed by students who are studying the subject matter covered in the chapter.
How to fill out chapter 7 lab exploring?
To fill out chapter 7 lab exploring, students need to follow the instructions provided in the lab guidelines or assignment given by the instructor. They may need to perform experiments, answer questions, or complete specific tasks related to the chapter.
What is the purpose of chapter 7 lab exploring?
The purpose of chapter 7 lab exploring is to provide students with hands-on experience and practical application of the concepts and theories taught in the corresponding chapter.
What information must be reported on chapter 7 lab exploring?
The specific information that needs to be reported on chapter 7 lab exploring will vary depending on the nature of the lab and the instructions given by the instructor. It may include data, observations, analysis, conclusions, and any other relevant information specified in the lab guidelines.
Fill out your chapter 7 lab exploring online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Chapter 7 Lab Exploring is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.