Get the free A PATTERN SYSTEM FOR ACCESS CONTROL
Show details
This document presents a pattern system for authorization and access control models, emphasizing the importance of considering security aspects during the early stages of information system development.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign a pattern system for
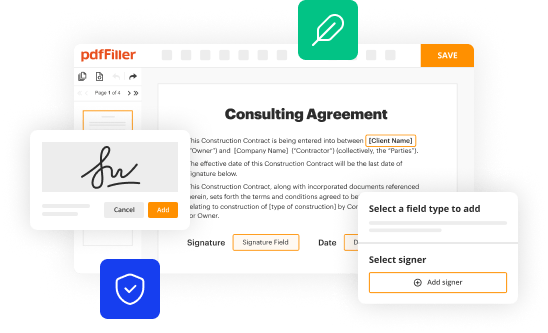
Edit your a pattern system for form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
Share your form instantly
Email, fax, or share your a pattern system for form via URL. You can also download, print, or export forms to your preferred cloud storage service.
Editing a pattern system for online
Follow the guidelines below to benefit from a competent PDF editor:
1
Set up an account. If you are a new user, click Start Free Trial and establish a profile.
2
Upload a file. Select Add New on your Dashboard and upload a file from your device or import it from the cloud, online, or internal mail. Then click Edit.
3
Edit a pattern system for. Rearrange and rotate pages, add and edit text, and use additional tools. To save changes and return to your Dashboard, click Done. The Documents tab allows you to merge, divide, lock, or unlock files.
4
Get your file. Select your file from the documents list and pick your export method. You may save it as a PDF, email it, or upload it to the cloud.
Dealing with documents is always simple with pdfFiller.
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out a pattern system for
How to fill out A PATTERN SYSTEM FOR ACCESS CONTROL
01
Step 1: Gather the necessary information about the access control requirements.
02
Step 2: Define the types of access required for different user roles.
03
Step 3: Create a list of patterns that represent each access level.
04
Step 4: Determine the rules for granting access based on the defined patterns.
05
Step 5: Implement the patterns into the access control system.
06
Step 6: Test the system to ensure it functions correctly with the defined patterns.
07
Step 7: Document the process and patterns for future reference.
Who needs A PATTERN SYSTEM FOR ACCESS CONTROL?
01
Organizations that require structured access to sensitive information.
02
IT departments responsible for managing user permissions.
03
Security professionals aiming to enhance digital security measures.
04
Compliance officers needing to meet regulatory access requirements.
05
Developers creating applications that require granular access controls.
Fill
form
: Try Risk Free






People Also Ask about
What do you mean by access control system?
Access Control Definition Access control is a data security process that enables organizations to manage who is authorized to access corporate data and resources. Secure access control uses policies that verify users are who they claim to be and ensures appropriate control access levels are granted to users.
What are the three 3 types of access control?
A basic access control system is a collection of equipment and organizational practices that allows you to grant convenient access to verified tenants and their guests. Your access control equipment list might include: Intercoms. Smart locks.
What is access control system in English?
Access control is a security technique that regulates who or what can view or use resources in a computing environment. It is a fundamental concept in security that minimizes risk to the business or organization.
What are the design patterns for access control?
Some common access control design patterns include hierarchical access control, mandatory access control, and discretionary access control. Hierarchical access control organizes users into hierarchical groups with different levels of access.
What are the 4 types of access control?
Here are the key steps to design and implement an effective access control solution for your business: Assess Your Security Requirements. Define Access Levels and Permissions. Choose the Right Access Control Technology. Implement Physical Security Measures. Establish User Enrollment and Authentication Processes.
What are examples of an access control system?
This includes devices such as electronic door locks, turnstiles, gates, and card readers that authenticate users' identity and determine their level of access based on their credentials. PACS can also incorporate biometric technologies such as fingerprint or facial recognition scanners for enhanced security.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is A PATTERN SYSTEM FOR ACCESS CONTROL?
A PATTERN SYSTEM FOR ACCESS CONTROL refers to a structured method or framework used to manage permissions and access to resources within an organization, ensuring that only authorized personnel can access sensitive information and areas.
Who is required to file A PATTERN SYSTEM FOR ACCESS CONTROL?
Organizations and entities that handle sensitive data or regulated information are typically required to file a PATTERN SYSTEM FOR ACCESS CONTROL to comply with legal and regulatory standards.
How to fill out A PATTERN SYSTEM FOR ACCESS CONTROL?
To fill out a PATTERN SYSTEM FOR ACCESS CONTROL, individuals or organizations should provide detailed information about their access control policies, identify the users and their access levels, and outline the security measures implemented to enforce these controls.
What is the purpose of A PATTERN SYSTEM FOR ACCESS CONTROL?
The purpose of a PATTERN SYSTEM FOR ACCESS CONTROL is to establish a framework that helps protect sensitive resources by managing who can access them, thereby reducing the risk of unauthorized access and data breaches.
What information must be reported on A PATTERN SYSTEM FOR ACCESS CONTROL?
Information that must be reported includes user identities, access levels, access rights, security protocols in place, training provided to users, and any incidents or breaches related to access control.
Fill out your a pattern system for online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

A Pattern System For is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.