Get the free Key Management and Certificates - cypherpunks
Show details
This document discusses various aspects of key management within cryptography, including problems related to key distribution, storage, validity, and the importance of effective key management solutions.
We are not affiliated with any brand or entity on this form
Get, Create, Make and Sign key management and certificates
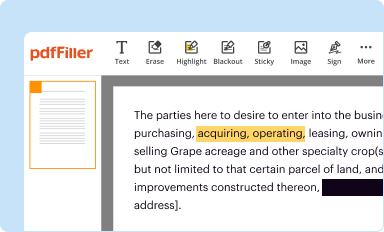
Edit your key management and certificates form online
Type text, complete fillable fields, insert images, highlight or blackout data for discretion, add comments, and more.
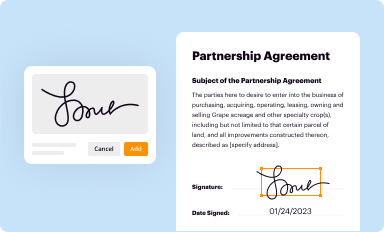
Add your legally-binding signature
Draw or type your signature, upload a signature image, or capture it with your digital camera.
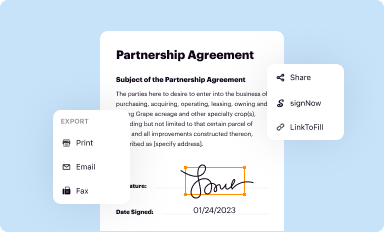
Share your form instantly
Email, fax, or share your key management and certificates form via URL. You can also download, print, or export forms to your preferred cloud storage service.
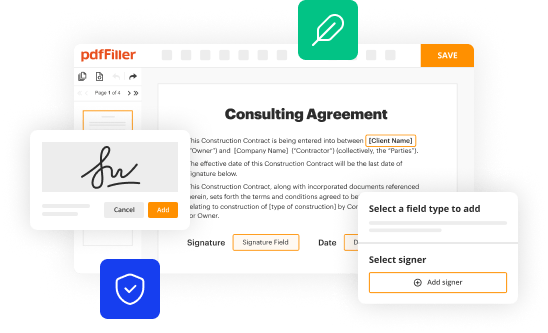
Editing key management and certificates online
Follow the steps down below to use a professional PDF editor:
1
Register the account. Begin by clicking Start Free Trial and create a profile if you are a new user.
2
Prepare a file. Use the Add New button to start a new project. Then, using your device, upload your file to the system by importing it from internal mail, the cloud, or adding its URL.
3
Edit key management and certificates. Rearrange and rotate pages, add new and changed texts, add new objects, and use other useful tools. When you're done, click Done. You can use the Documents tab to merge, split, lock, or unlock your files.
4
Save your file. Choose it from the list of records. Then, shift the pointer to the right toolbar and select one of the several exporting methods: save it in multiple formats, download it as a PDF, email it, or save it to the cloud.
pdfFiller makes working with documents easier than you could ever imagine. Create an account to find out for yourself how it works!
Uncompromising security for your PDF editing and eSignature needs
Your private information is safe with pdfFiller. We employ end-to-end encryption, secure cloud storage, and advanced access control to protect your documents and maintain regulatory compliance.
How to fill out key management and certificates
How to fill out Key Management and Certificates
01
Identify the key management system required for your application.
02
Gather the necessary security requirements for your keys and certificates.
03
Generate the cryptographic keys using a secure method.
04
Obtain digital certificates from a trusted Certificate Authority (CA).
05
Deploy the keys and certificates in the appropriate environment.
06
Regularly review and update keys and certificates to ensure ongoing security.
07
Implement a key rotation policy to mitigate security risks.
Who needs Key Management and Certificates?
01
Organizations handling sensitive data that require encryption for data protection.
02
Businesses that operate in regulated industries such as finance, healthcare, or government.
03
IT and security teams responsible for maintaining secure communications.
04
Developers implementing secure applications that utilize SSL/TLS protocols.
05
Any entity that needs to ensure the authenticity and integrity of data exchanged over networks.
Fill
form
: Try Risk Free






People Also Ask about
What is the difference between a digital certificate and a public key?
Digital Certificates use a system of public key cryptography to secure online communication. Public key cryptography is a system in which a pair of keys is used to encrypt and decrypt data. The keys are mathematically related, but one key can be made public, while the other key is kept private.
What is the function of certificate management?
Certificate Management involves discovering, analyzing, monitoring, and managing all digital certificates deployed by the Certificate Authority. Proper certificate management should be fundamental to your organization's security strategy.
What do you mean by key management?
Key management refers to management of cryptographic keys in a cryptosystem. This includes dealing with the generation, exchange, storage, use, crypto-shredding (destruction) and replacement of keys. It includes cryptographic protocol design, key servers, user procedures, and other relevant protocols.
What is the difference between KMS and PKI?
Public Key Infrastructure (PKI) and Key Management Systems (KMS) are critical for securing digital communications and data. PKI ensures the integrity and authenticity of data through encryption, while KMS manages cryptographic keys used to protect sensitive information.
What is certificate management process?
Certificate management is the act of monitoring, facilitating, and executing digital x. 509 certificates. It plays a critical role in keeping communications between a client and server operating, encrypted, and secure.
What is the key management plan?
The Key Management Plan documents how current and/or planned key management products and services will be supplied by the Key Management Infrastructure and used by the cryptographic application to ensure that lifecycle key management support is available.
What is key and certificate management?
UC's Encryption Key and Certificate Management Standard establishes requirements for selecting cryptographic keys, assigning key strength, managing keys and managing digital certificates.
What is the key and certificate management plan?
The Key and Certificate Management Plan (KCMP) describes the use and control of cryptographic products and services used by a cryptographic application (cryptographic engine, cryptographic module, End Cryptographic Unit (ECU), or system) throughout its lifetime.
For pdfFiller’s FAQs
Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is Key Management and Certificates?
Key Management refers to the processes and technologies involved in handling cryptographic keys within a cryptographic system. Certificates are digital documents used to prove the ownership of a public key.
Who is required to file Key Management and Certificates?
Organizations and individuals that utilize cryptographic systems, such as those involved in secure communications or data protection, are typically required to file Key Management and Certificates.
How to fill out Key Management and Certificates?
To fill out Key Management and Certificates, you must provide relevant information such as the key identifier, the algorithm used, expiration dates, and the certificate holder's details. Follow any specific guidelines provided by your regulatory body.
What is the purpose of Key Management and Certificates?
The purpose of Key Management and Certificates is to ensure the secure creation, distribution, storage, and destruction of cryptographic keys, thus maintaining trust and integrity in digital communications.
What information must be reported on Key Management and Certificates?
Information that must be reported includes the types of keys used, their expiration dates, the identity of the key owners, details about the certificates, and any key compromise incidents.
Fill out your key management and certificates online with pdfFiller!
pdfFiller is an end-to-end solution for managing, creating, and editing documents and forms in the cloud. Save time and hassle by preparing your tax forms online.

Key Management And Certificates is not the form you're looking for?Search for another form here.
Relevant keywords
Related Forms
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.