Last updated on Apr 5, 2026

Get the free HIPAA Security Checklist
We are not affiliated with any brand or entity on this form
Why pdfFiller is the best tool for your documents and forms
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is hipaa security checklist
The HIPAA Security Checklist is a document used by healthcare organizations to assess their compliance with HIPAA Security Rule requirements.
pdfFiller scores top ratings on review platforms




Who needs hipaa security checklist?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to hipaa security checklist
Understanding the HIPAA Security Checklist
The HIPAA Security Checklist is a vital tool used in the healthcare sector to ensure compliance with the HIPAA Security Rule. This checklist assists organizations in evaluating their adherence to regulations that safeguard electronic protected health information (EPHI). By assessing compliance, healthcare entities can not only protect sensitive data but also mitigate vulnerabilities associated with EPHI.
-
The checklist defines the key areas that organizations must address to meet compliance.
-
It offers a succinct overview of the HIPAA Security Rule, emphasizing its importance in healthcare.
-
Vulnerabilities associated with EPHI are identified to help organizations fortify their security measures.
Purpose and Benefits of Using the HIPAA Security Checklist
Utilizing the HIPAA Security Checklist brings numerous advantages for organizations in the healthcare sector. This tool highlights essential factors that reinforce compliance and streamline the management of EPHI protection.
-
It aids in identifying gaps in existing security measures, allowing for proactive improvements.
-
The checklist enhances organizational compliance with HIPAA regulations, reducing potential penalties.
-
It facilitates better management of EPHI protection, ultimately fostering trust with patients.
Key Features of the HIPAA Security Checklist
The HIPAA Security Checklist consists of several main components that are crucial for comprehensive compliance. Its structure allows for thorough evaluation and easy completion.
-
Sections dedicated to administrative, physical, and technical safeguards provide a comprehensive framework.
-
It distinguishes between required and addressable implementation specifications, clarifying compliance expectations.
-
The form’s structure includes checkboxes and fillable fields to ensure all necessary data is captured.
Who Needs the HIPAA Security Checklist?
Various stakeholders in the healthcare industry can benefit from utilizing the HIPAA Security Checklist. Understanding the target audience is essential for ensuring compliance.
-
Healthcare organizations must comply with HIPAA regulations, making this checklist indispensable.
-
Key roles within these organizations, including IT and compliance officers, will find it useful for their duties.
-
Business associates must also adhere to compliance responsibilities, highlighting the checklist's relevance.
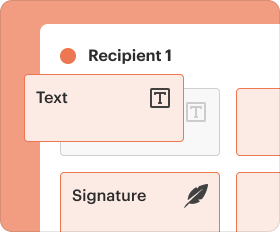
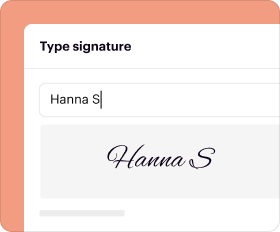
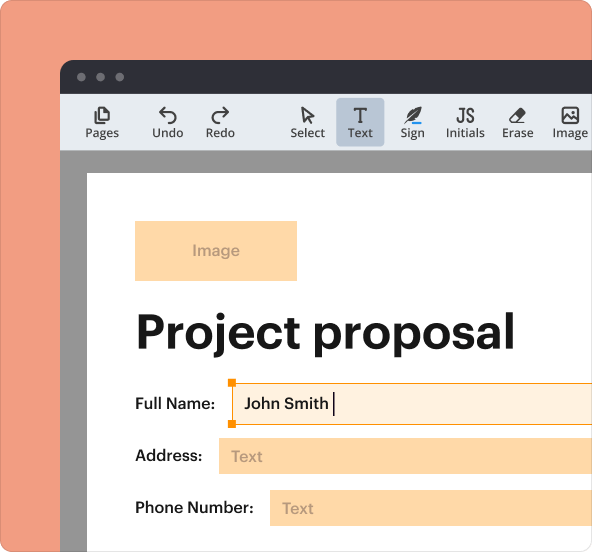
How to Fill Out the HIPAA Security Checklist Online
Completing the HIPAA Security Checklist online using pdfFiller offers a streamlined process. Below are detailed instructions to aid users in effectively finishing the form.
-
Navigate to the pdfFiller platform and open the HIPAA Security Checklist form.
-
Carefully fill in all required fields, paying particular attention to sections regarding safeguards.
-
Utilize the cloud storage option for easy access and secure keeping of your filled document.
Common Errors to Avoid When Completing the HIPAA Security Checklist
To maximize compliance, users should be aware of common pitfalls when filling out the HIPAA Security Checklist. Avoiding these mistakes can significantly enhance the quality and accuracy of submissions.
-
Do not overlook essential fields and safeguards that could compromise compliance.
-
Ensure the distinction between required and addressable standards is understood to prevent misinterpretation.
-
Validate all entries before submission to rectify potential errors.
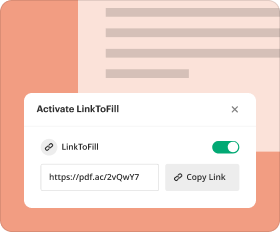
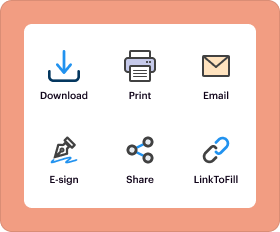
How to Submit the HIPAA Security Checklist
Understanding the submission process for the HIPAA Security Checklist is crucial for effective compliance. This section clarifies the methods available for submission.
-
Consider both electronic and physical submission options based on your organizational preferences.
-
Implement best practices for record retention to safeguard your submitted documents.
-
Track the submission status to confirm compliance throughout the review process.
Security and Compliance Considerations for the HIPAA Security Checklist
When managing sensitive documents like the HIPAA Security Checklist, security and compliance should remain a priority. This section discusses key considerations to bear in mind.
-
Familiarize yourself with HIPAA and other data protection regulations relevant to the checklist.
-
Utilize pdfFiller's compliance and security features, including encryption, for enhanced safety.
-
Adhere to recommendations on the secure storage and handling of sensitive documents.
Realizing the Benefits of Using pdfFiller for the HIPAA Security Checklist
Leveraging pdfFiller for the HIPAA Security Checklist enhances the overall user experience and compliance capabilities. The platform offers several noteworthy advantages.
-
Users can enjoy a user-friendly interface for filling out and editing forms efficiently.
-
Security features provided by pdfFiller align with HIPAA compliance, ensuring document safety.
-
A community of support and comprehensive resources is available to assist users in the process.
Next Steps for Ensuring HIPAA Compliance with the Checklist
After completing the HIPAA Security Checklist, organizations should take subsequent steps to uphold compliance. Consider the following suggestions for ongoing security management.
-
Engage in regular audits and updates to your security measures to stay ahead of regulatory requirements.
-
Utilize available resources for continuous education and compliance training for staff members.
-
Explore pdfFiller’s tools for effective document management beyond the checklist.
How to fill out the hipaa security checklist
-
1.Access pdfFiller and search for 'HIPAA Security Checklist'.
-
2.Open the document by clicking on the form's title in the search results.
-
3.Review the first section, which outlines the purpose and requirements of the form, to understand how to complete it effectively.
-
4.Begin filling out the checkboxes for administrative safeguards, physical safeguards, and technical safeguards based on your organization's current practices and policies.
-
5.For each safeguard listed, indicate your compliance status by checking the appropriate boxes for required and addressable specifications.
-
6.Gather necessary information beforehand, such as security policies, procedures, and any existing security assessments to accurately fill out the form.
-
7.Utilize pdfFiller's fillable fields for any required text inputs, ensuring you provide detailed descriptions where needed.
-
8.After completing the form, review each section carefully to ensure all information is accurate and reflective of your security measures.
-
9.Save your changes periodically to avoid losing information by clicking the save icon in pdfFiller.
-
10.Once satisfied with the completed form, download it as a PDF or submit it directly through pdfFiller as per your organizational procedures.
Who needs to fill out the HIPAA Security Checklist?
The HIPAA Security Checklist is essential for healthcare organizations, compliance officers, IT professionals, and administrative staff overseeing HIPAA compliance and data security measures.
Is notarization required for the HIPAA Security Checklist?
No, notarization is not required for the HIPAA Security Checklist, making the process easier for organizations to complete and maintain.
What are the deadlines for completing this checklist?
While there are no specific deadlines for the HIPAA Security Checklist itself, conducting regular assessments is essential to ensure continuous compliance with HIPAA regulations.
How can I submit the completed HIPAA Security Checklist?
You can submit the completed HIPAA Security Checklist through pdfFiller by utilizing the integrated submission options or by downloading and sharing it via your organization’s preferred methods.
What common mistakes should I avoid when filling out the form?
Avoid skipping sections or checking boxes without verifying compliance status. Ensure all information is accurate and reflective of current practices to prevent gaps in assessments.
How long does it take to process the HIPAA Security Checklist?
Processing time for the HIPAA Security Checklist can vary; however, since it is an internal assessment tool, results should ideally be reviewed and finalized promptly after completion.
What information do I need before filling out this checklist?
Gather information related to your organization's security policies, procedures, past security audits, and any documentation of existing security measures to ensure accurate completion of the checklist.
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.